Faster Audits, Stronger Compliance Case Study
Find out how Cloudaware helped automate AWS compliance, bring it in line with 94% of best practices, and cut audits by 60%.
This case study shows how a global cybersecurity company that manages 188 AWS accounts and 7.12 million assets used Cloudaware Compliance Engine to meet 94% of AWS security best practices, follow ISO 27001, NIST 800-53, and GDPR standards, and cut the time it takes to prepare for audits by 60%.
About The Customer
Company S is a top worldwide cybersecurity company with its main office in Texas, USA, and numerous locations in Europe. The Company started out as an IT reseller in the 1990s, but now it offers a full range of security solutions, such as data loss prevention, cloud access security broker (CASB), firewall technologies, AI-driven data classification, insider threat prevention, and data detection and response (DDR). The Company S has more than 12,000 customers around the world, including governments and businesses in more than 150 countries.
AWS Footprint:
- 188 AWS accounts and 7,276 Amazon EC2 instances
- 2,100 Amazon S3 buckets and 480 Amazon RDS instances
- 900 IAM roles and rules
- 120 Amazon VPCs that can link to each other across regions
Infrastructure Assets: 7.12M
Asset Types: 798
Problem Statement
The Company S manages a huge AWS deployment with more than 180 AWS accounts and more than 7,000,000 assets that can be changed.
Company S is a multinational cybersecurity provider that handles sensitive customer data and mission-critical services in AWS environments. Its major goal is to provide security solutions, but keeping AWS compliant with internal rules is just as important. The Company S must make sure that its cloud infrastructure meets tight regulatory standards (including GDPR, ISO 27001, and NIST 800-53) and the terms of its contracts with customers. It was getting harder to make sure that its cloud infrastructure followed the rules and was run properly because it was so big and constantly changing.
The manual auditing of resource configurations, uneven tagging, and slow detection of non-compliant assets all posed risks of data breaches, regulatory infractions, and operational inefficiencies. As many as 45% of AWS resources were not regularly tagged, which made it more likely that they would be mismanaged and made audits more difficult. When thousands of resources are used around the world, it becomes hard to make sure that tagging policies are followed, security control are monitored, and fixing problems across accounts is done automatically. The primary problems were:
- Full access to AWS inventory across several accounts and regions
- Following the rules for the AWS environment
- Keeping up with internal tagging standards and making sure tags are always the same
- Streamlining and automating remediation tasks
Solution
Company S used the Cloudaware Compliance Engine and CMDB to deal with these problems.
Cloudaware works with AWS Organizations to find and manage accounts. It uses CloudFormation templates to set up permissions and resources without any problems. These templates include the permissions needed to automatically find and gather customer data from important AWS security and monitoring services, such as:
- AWS Security Hub: securityhub:Des*, securityhub:G*, securityhub:L*
- Amazon GuardDuty: guardduty:Des*, guardduty:G*, guardduty:L*
AWS Config: config:Describe*, config:List* - AWS CloudTrail:, cloudtrail:DescribeTrails, cloudtrail:GetTrailStatus, cloudtrail:LookupEvents
AWS IAM: iam:Get*, iam:L*, iam:GenerateCredentialReport
With these rights, Cloudaware can automatically add AWS asset data to the CMDB, giving you a single, up-to-date view of all your resources. The Compliance Engine employs the CMDB as a central hub, which cuts down on AWS API calls.
The Company S got a full compliance management solution by putting the Compliance Engine along with BI analytics and automation solutions.
Architecture
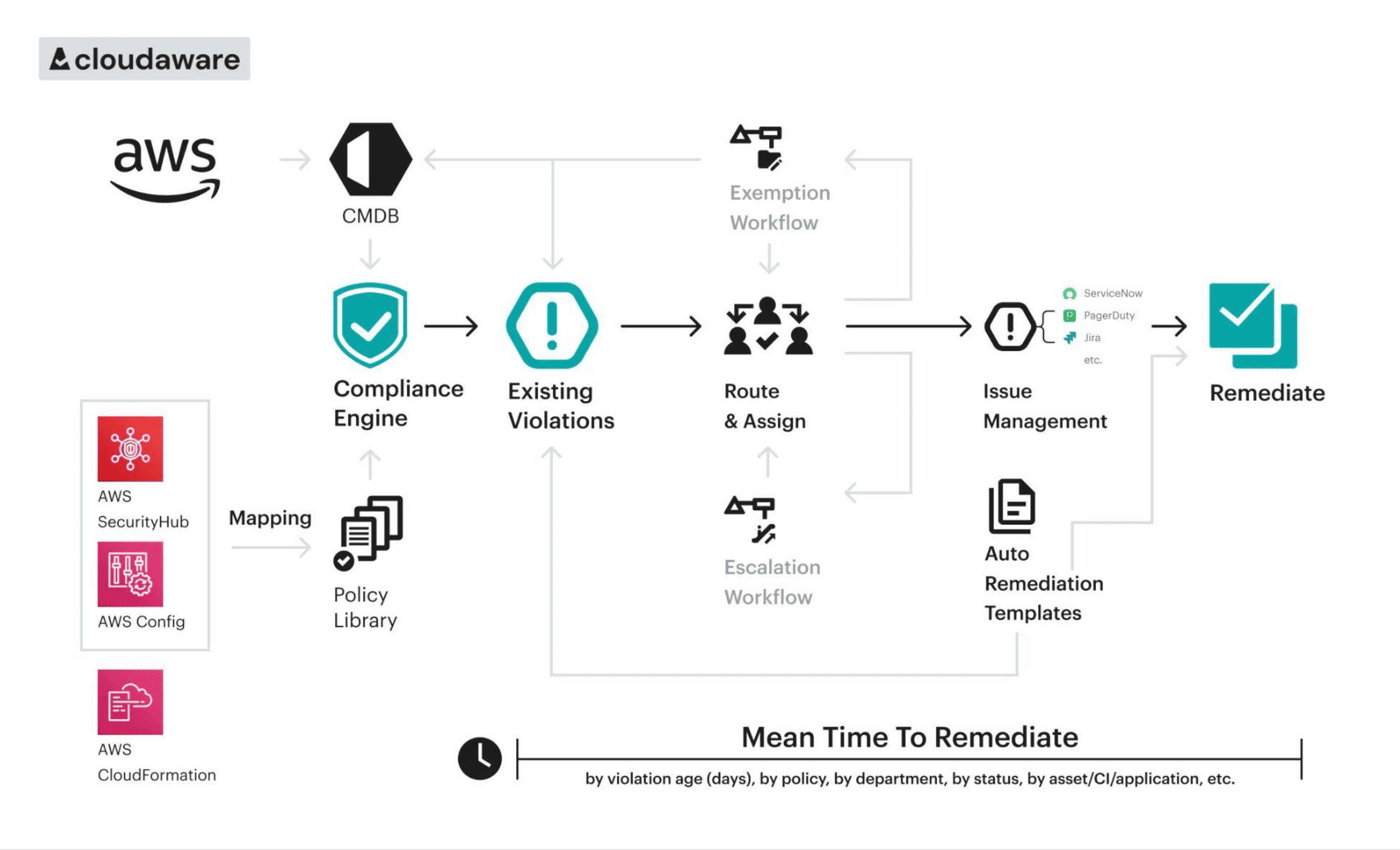
Compliance Engine
The Cloudaware Compliance Engine combines AWS security standards like AWS Foundational Security Best Practices (FSBP) and CIS Benchmarks so that AWS environments can be checked all the time. Cloudaware lets companies monitor compliance against policies that follow FSBP, CIS, NIST, and ISO by taking in data from AWS services like AWS Config, Security Hub, and CloudTrail.
Policy mappings example:
| NIST SP 800-53 | Cloudaware CE Policies | AWS Security Hub |
|---|---|---|
| NIST CSF v1.1 → PR.AC-7: Users, devices, and other assets are authenticated (e.g., single-factor, multi-factor) commensurate with the risk of the transaction (e.g., individuals' security and privacy risks and other organizational risks | AWS Account Root User MFA is not enabled. AWS Account Root User Hardware MFA is not enabled | IAM.5 MFA should be enabled for all IAM users that have a console password. IAM.6 Hardware MFA should be enabled for the root user |
Policy Library & Editor
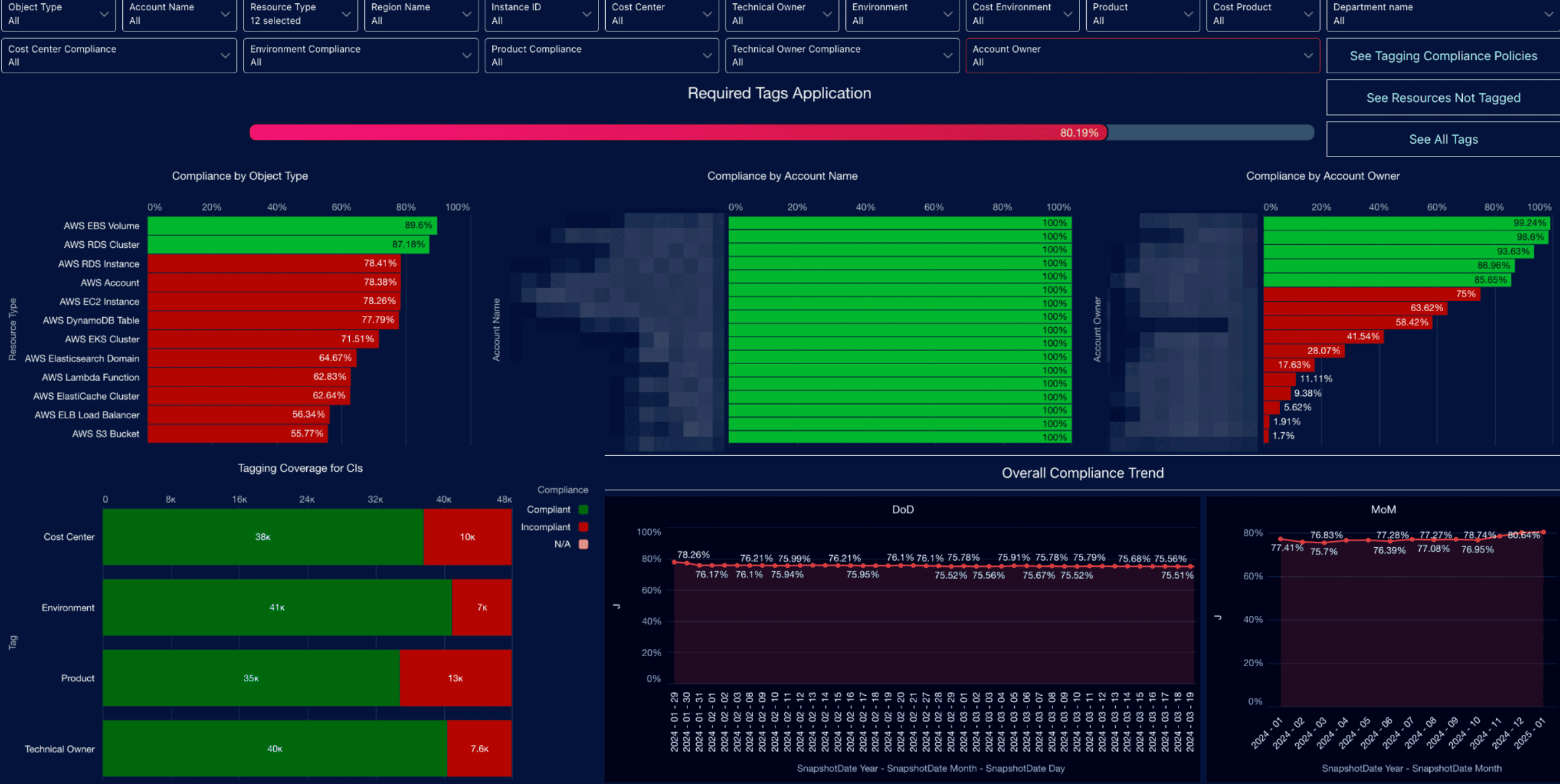
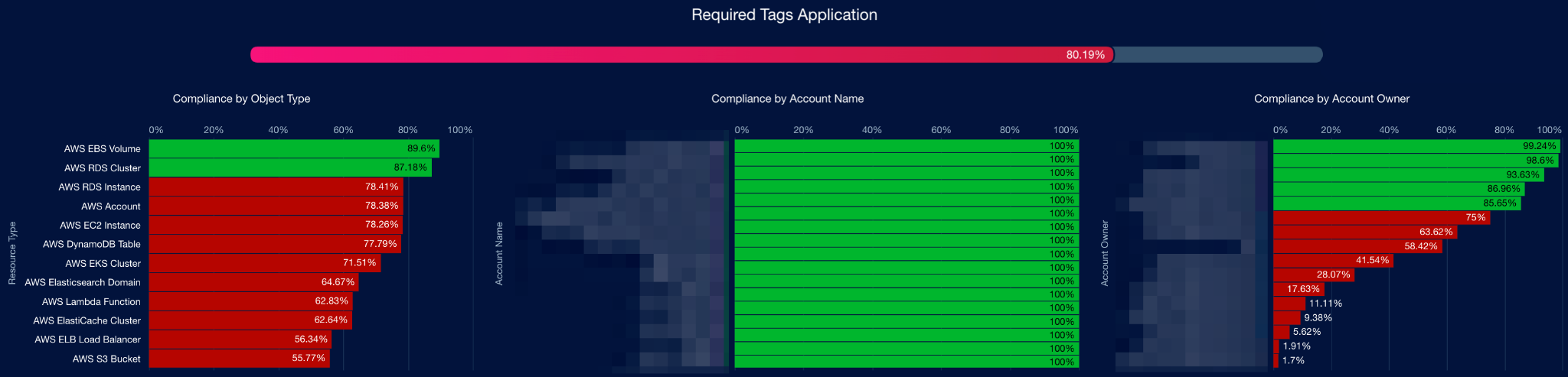
The built-in Compliance Engine Policy Library and Editor are part of the solution. The Company S worked with Cloudaware to create and put into place unique policies to make sure that tagging was done correctly. These rules provide obligatory tags for several sorts of resources, like EC2, S3, RDS, and Lambda. These tags included Account Owner, Application, Product, and others.
Cloudaware also gave Company S a tagging compliance dashboard so they could keep an eye on how well they were fixing things.
An example of a custom tagging policy is the Application tag:
inputType: "CA10__CaAwsInstance__c"
conditions:
# Checking that the required tag exist
- status: "COMPLIANT"
currentStateMessage: "Required tag is present on the resource."
check:
TAG_EXISTS:
name:
BYTES: "Application"
otherwise:
status: "INCOMPLIANT"
currentStateMessage: "The resource doesn't have the required tag."
remediationMessage: "Ensure that the required tag is present and valid: Application."
Tagging compliance dashboard example:
Workflows
The Compliance Engine was linked to Jira to make sure that compliance was enforced automatically. Checks for the most important policies were set up to automatically make tickets for the teams in charge.
After the remedy was made, Cloudaware changed the compliance status, closed the Jira ticket, and wrote down the time and date of the modification, making sure that everything could be tracked and audited.
Automation
Cloudaware used lambda-based remediation processes to automatically add tags that met Forcepoint's tagging compliance rules. Escalation workflows made sure that problems that weren't fixed quickly were handled by the right teams.
Analytics
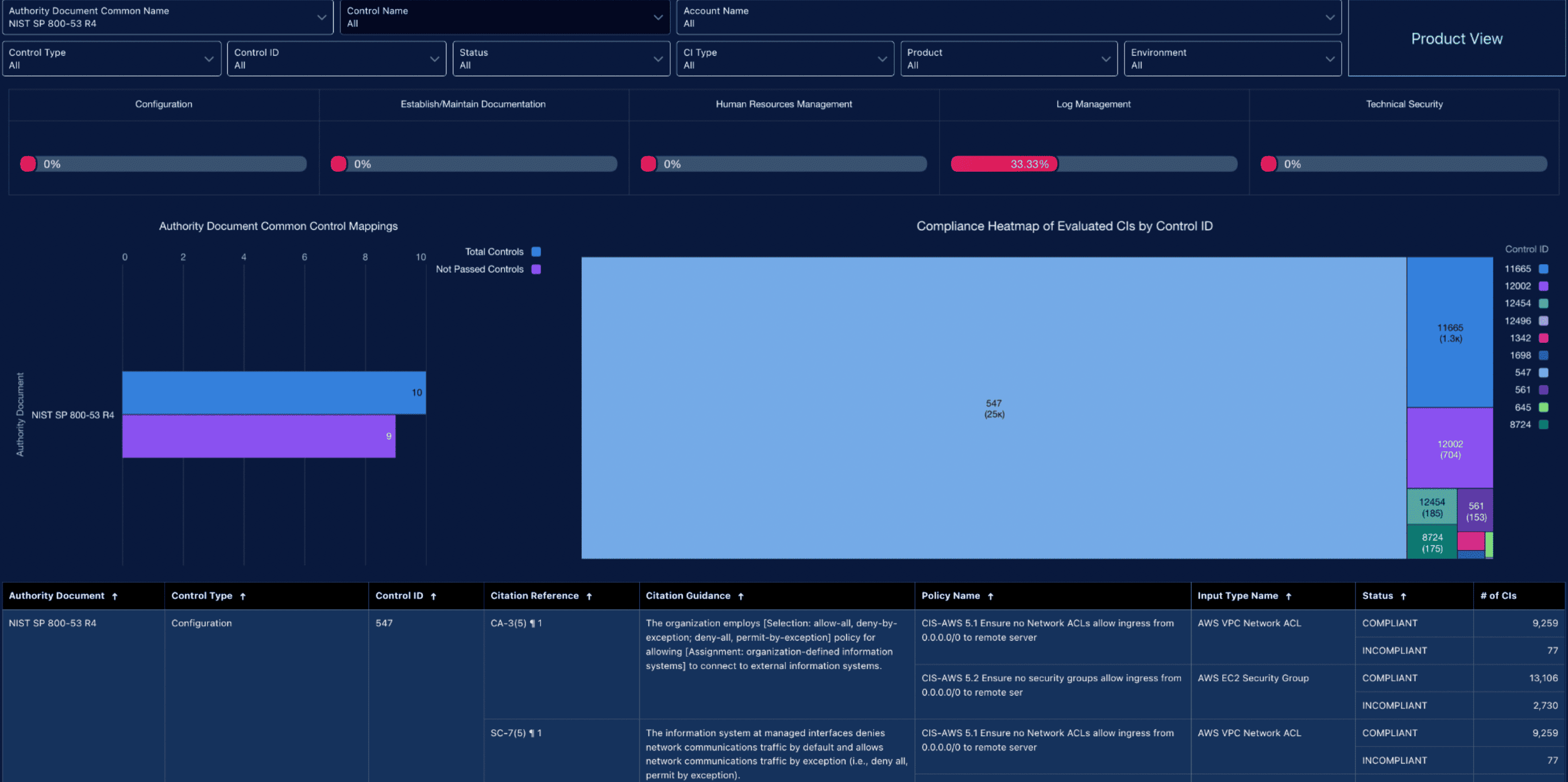
Cloudaware built a Unified Compliance Framework dashboard that used a set of common controls for both internal and external audits.
The Cloudaware Compliance Engine uses a one-to-many mapping mechanism to link each common control to several compliance frameworks. By choosing a certain control ID, audit teams could find the overlaps between compliance and security frameworks, break down and understand the relevant controls, and make sure that the organization's regulatory needs were all in line with each other. This allowed Company S to see how well it followed its own rules for following the law.
Unified compliance dashboard example (NIST 800-53 Rev4 is selected in filters):
Implementation
Week 1: CMDB setup – the Company S imported AWS inventory into Cloudaware CMDB.
Week 2-3: The solution deployment – Cloudaware enabled the Compliance Engine, which contains over 500 pre-built compliance policies, including CIS. The unified Cloudaware compliance framework, which cross-references ISO 27001, SOC 2, NIST, and other standards, was also introduced.
Week 4-5: Exception tuning – the Company S customized rules for specific VPCs, accounts, and services to avoid false positives.
Week 6: Customizations – custom policies for tagging compliance were implemented by Cloudaware, along with a comprehensive dashboard generated for executives and teams.
Week 7-8: Automation activation – Cloudaware enabled automated remediation for recurring misconfigurations.
Results
The Company S's compliance with AWS Foundational Security Best Practices (FSBP) went up from 72% to 94%, and with CIS AWS Benchmarks, it went up from 70% to 92% across all accounts.
The average compliance rate for AWS resources went up from 71.95% to 83–87%.
The average compliance rate for AWS resources with the Account Owner tag went up from 48.63% to 75–80%.
The average compliance rate for AWS resources with the Application tag went from 69% to 80%.
The Mean Time to Remediate (MTTR) went down by 67%, from about 30 days to 10 days.
About 85% of infractions that are found are completely fixed within five weeks of the solution being put in place.
There was a 65% drop in the frequency of recurring misconfigurations, such as open security groups, public S3 buckets, and IAM keys that weren't being used.
Compliance monitoring and automatic deactivation operations cut down on inactive IAM keys by 80%.
90% of IAM roles are now in line with least-privilege access criteria.
According to Company S, the amount of manual auditing was cut by 60%.
Privacy Controls
With Cloudaware's single compliance architecture, Company S was able to swiftly find sensitive Amazon S3 and RDS resources, enforce required encryption, and set up automated lifecycle policies for all AWS services.
- 98% of sensitive data assets were found and sorted using automatic tagging.
- Over 95% of resources had lifecycle and backup procedures put in place to make sure they followed GDPR and company rules.
- All sensitive datasets are protected by multi-region KMS-based encryption.
Because of this, Company S's privacy and data protection stance become a lot stronger.
Regulatory Compliance Outcomes
The Company S uses the Cloudaware Compliance Engine to:
- strengthened key controls to improve audit readiness and maintain ISO 27001 certification
- enabled automated continuous monitoring of NIST 800-53 controls enterprise-wide
- achieved and demonstrated over 99.5% GDPR compliance across all EU operations
- reduced audit preparation time by 60% through automated evidence collection and reporting
Testimonial
“With Cloudaware, we streamlined our compliance processes, achieving 94% alignment with AWS best practices and strengthening our security posture. The solution saved our teams hours, allowing them to focus on higher-value initiatives””, – Company S Company S's Chief Information Security Officer.
Conclusion
Cloudaware automated compliance monitoring, enforced tagging regulations across all of Company Soint's business apps, and added real-time notifications for security measures that weren't set up correctly or were missing. The Company S used the Cloudaware Compliance Engine to improve its internal security, make sure it followed industry standards, and keep customers' trust by showing that it followed strict cloud governance that was in line with its own cybersecurity policies.
If your organization is facing similar challenges in securing your public cloud infrastructure, we encourage you to explore how Cloudaware can help. Contact us today to schedule a demo and learn more about our solutions.
