The DevSecOps lifecycle is usually shown as an infinite loop, but the diagram alone doesn’t explain how security decisions are enforced as software moves through the delivery process. What matters in practice is where controls exist, who owns them, and what evidence remains after each step.
This article treats the DevSecOps lifecycle as a set of specific decisions applied to the software delivery process. It shows how security fits into code, build, test, release, and runtime without assuming a specific platform or DevSecOps toolchain. Each phase is described in terms of gates, ownership, and outputs rather than concepts.
Key inisghts
- The DevSecOps lifecycle is a system of enforceable security decisions applied across the software delivery process, from planning to runtime, where each stage defines what is allowed, what is blocked, and what evidence remains.
- The DevSecOps stages only become useful when each stage answers a concrete operational question. Planning defines acceptable risk and ownership. Build determines what never ships. Release controls who can override a gate. Runtime verifies whether what is running still matches what was approved.
- The DevSecOps planning phase determines whether the rest of the lifecycle will remain stable. Missing decisions at this stage reappear later as exceptions, unclear approvals, and audit reconstruction work.
- A healthy DevSecOps process flow can be described simply: a change moves forward only when current risk, target environment, and ownership rules remain aligned.
- The DevSecOps infinity loop exists because security decisions expire. Runtime findings must influence future builds, policies, and approval logic instead of remaining isolated.
- A mature DevSecOps software development lifecycle relies on explicit decisions, stable ownership, and durable evidence rather than memory or ad hoc coordination.
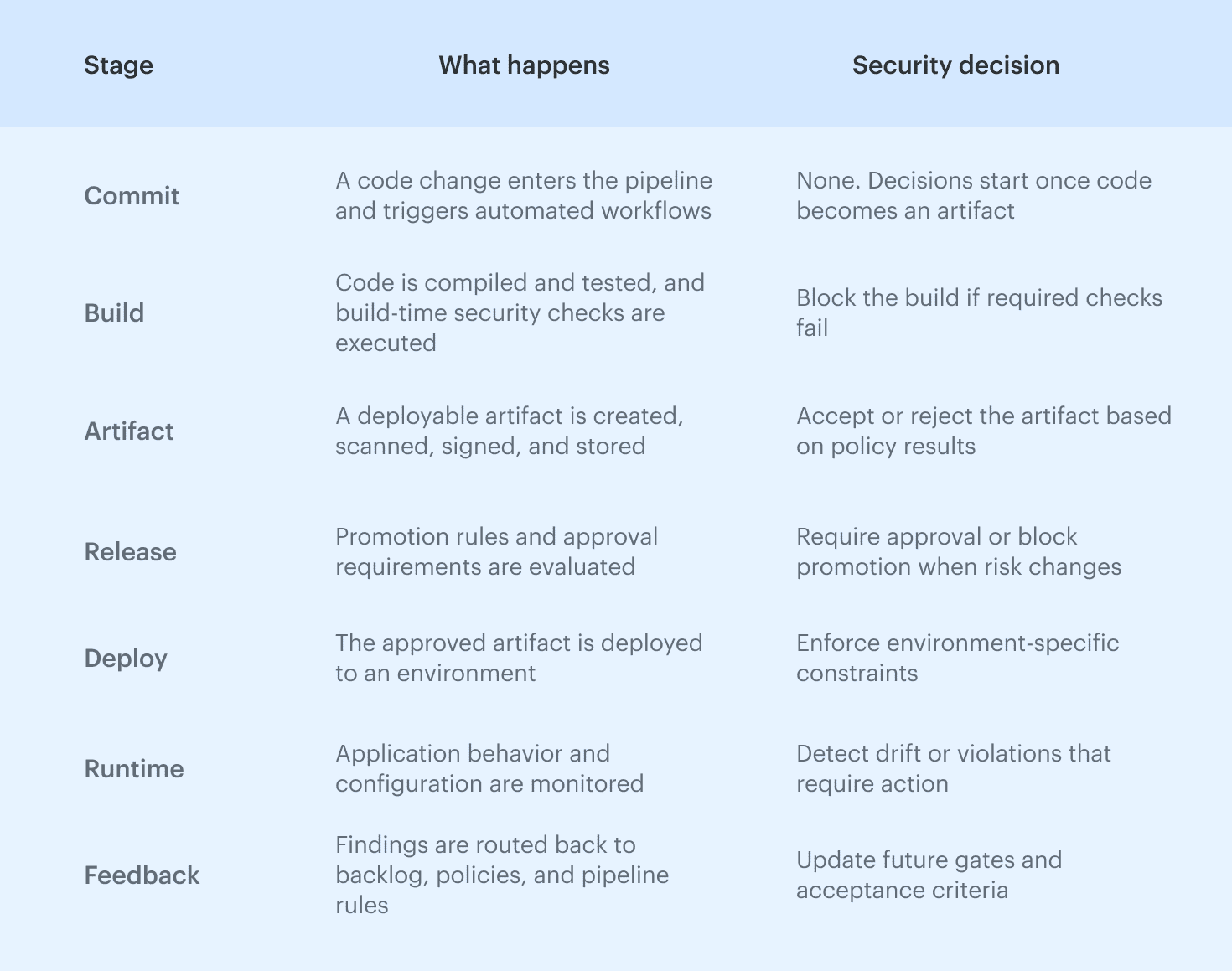
DevSecOps stages at a glance
Most explanations of the DevSecOps lifecycle begin with a loop, but in practice, teams need a clear stage model first. Each stage answers the same four questions: what is decided, what is enforced, who owns it, and what evidence remains.
| Stage | Decisions | Enforcement | Owner | Evidence |
|---|---|---|---|---|
| Plan | Scope, risk, ownership, acceptance criteria | Requirements, policies, control expectations | Architecture and security | Approved scope, owners, control requirements |
| Code | Secure patterns, dependencies, review conditions | Repository rules, branch protections, PR, and pre-commit checks | Engineering | Violations, review records, ownership context |
| Build | What can ship, what must fail | CI gates, artifact policies, dependency checks, SBOM | Platform | Build logs, policy outcomes, artifact metadata |
| Test | What blocks release, what stays advisory, when overrides apply | Release-grade security and API test gates | Platform and security | Release-linked test results, recorded overrides |
| Release | What can be promoted, where approval is required | Approval policies, promotion rules, environment-aware gates | Platform and risk owners | Approval records, deployment decisions |
| Operate | What must remain true in runtime, what deviations require action | Baseline checks, runtime controls, drift detection | Platform | Runtime state, drift records, exceptions |
| Monitor and feedback | What must change in controls, policies, or gates | Feedback into backlog, policies, and pipeline rules | Security and platform | Policy updates, incident-driven follow-up |
DevSecOps lifecycle explained in one loop
The DevSecOps lifecycle is a framework that integrates security practices into every stage of the software development lifecycle, shifting security "left" to identify vulnerabilities early.
The SDLC defines how software is built, while the DevSecOps lifecycle defines where security decisions are introduced, enforced, and carried forward. It overlays the delivery process with controls that repeat whenever code, infrastructure, or environments change. This DevSecOps lifecycle diagram and process flow diagram show where controls are applied across the delivery pipeline.
This DevSecOps lifecycle diagram and process flow diagram show where controls are applied across the delivery pipeline.
The infinity loop reflects the fact that security decisions do not end at release. A vulnerability identified in runtime feeds back into backlog, code, tests, and policies, while a misconfiguration detected in production changes future deployment gates. The loop represents continuous reuse of decisions rather than continuous scanning.
This distinction separates DevSecOps from “DevOps plus security tools.” Tools generate signals, but the lifecycle defines enforceable decision points that determine whether a build is blocked, a release is approved, or a runtime change requires action.
Because these decisions are connected, they remain consistent over time even as teams, services, and pipelines evolve. When teams describe the DevSecOps life cycle only in terms of tools or stages, they miss this continuity.
In practice, the lifecycle is defined by decisions, ownership, and evidence that persist across change.
How to read the DevSecOps lifecycle diagram
The DevSecOps lifecycle diagram highlights where different types of control apply rather than simply showing a loop.
- Preventive controls appear early, primarily in planning, code, and build, where failures are deterministic and inexpensive to fix.
- Approval-driven controls appear at release boundaries, where risk changes and ownership decisions must be explicit.
- Runtime controls validate whether earlier assumptions still hold and feed real conditions back into future builds and policies.
DevSecOps infinity loop: how the cycle actually works
The DevSecOps infinity loop describes how security decisions are re-evaluated as inputs change. Code changes, dependency updates, infrastructure drift, and incidents all invalidate earlier assumptions.
Without this loop, security becomes a set of disconnected checks with no memory.
Why the loop never ends
The loop continues because:
- Code changes alter behavior
- Dependencies introduce new risk
- Infrastructure drift changes exposure
- Incidents redefine acceptable conditions
Each of these feeds back into backlog priorities, pipeline gates, and policy rules instead of living in isolated reports.
Where security decisions live inside the loop
Security is enforced at three points:
- When code becomes an artifact
- When an artifact is promoted
- When software runs in an environment
Each point produces a binary outcome: allow, block, or require approval. The loop ensures those outcomes are re-evaluated whenever conditions change.
DevSecOps process flow from commit to production
The DevSecOps process flow describes how a change moves through the pipeline and where security decisions are enforced. Each transition, from commit to build, build to artifact, and artifact to deployment, introduces a point where risk is evaluated and a clear outcome is required.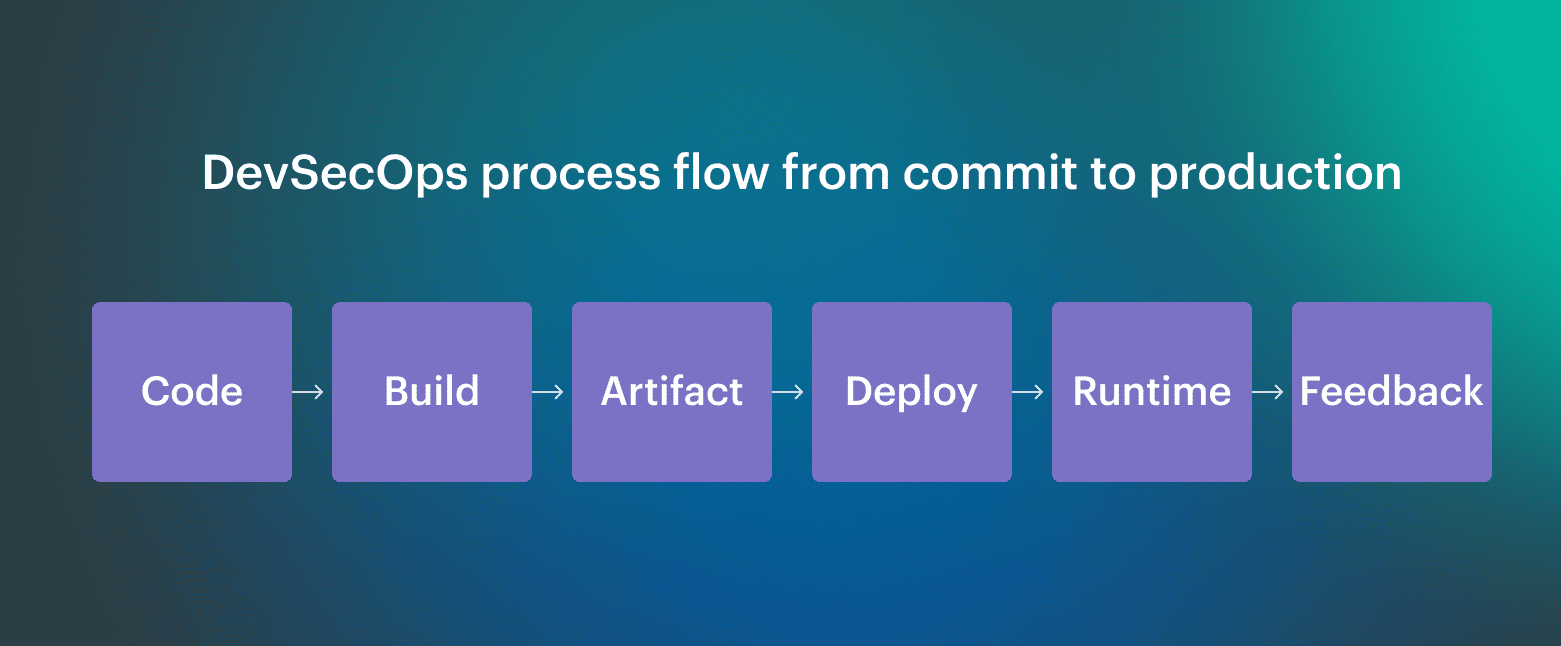 This DevSecOps process and flow diagram representation helps teams understand how decisions move across the pipeline without becoming disconnected checks.
This DevSecOps process and flow diagram representation helps teams understand how decisions move across the pipeline without becoming disconnected checks.
Security enforcement follows three rules:
- Automated checks run where outcomes are deterministic
- Approvals exist only where risk changes
- Policies define allowed and blocked paths
End-to-end flow: code, build, artifact, deploy, runtime, feedback
Read also: 15 DevSecOps Tools - Software Features & Pricing Review
DevSecOps steps from planning to feedback
The DevSecOps steps follow a consistent pattern across the lifecycle. A change moves forward only when risk is evaluated, a decision is enforced, and evidence is recorded, from the first planning decision through runtime feedback.
Each transition produces a clear outcome:
- Build: allowed or blocked
- Release: approved or escalated
- Runtime: acceptable or requires action
This consistency makes the DevSecOps process predictable.
Mapping the DevSecOps lifecycle to the software development lifecycle
The DevSecOps software development lifecycle extends a traditional SDLC by introducing enforceable security decisions at each stage. Instead of adding separate security activities, DevSecOps embeds controls, ownership, and feedback directly into planning, build, release, and runtime.
DevSecOps does not redefine how software is built. It operates as a decision layer on top of the SDLC, whether that model is iterative, incremental, or release-driven.
There is no single best software development life cycle in DevSecOps because the approach adapts to existing delivery models. In the DevSecOps software development lifecycle, roles are tied to decision ownership rather than stages, ensuring each control has a clear accountable owner.
SDLC to DevSecOps mapping
| SDLC stage | DevSecOps control | Evidence |
|---|---|---|
| Plan | Risk definition and ownership | Approved scope |
| Build | CI enforcement and SBOM generation | Build records |
| Test | Release gates | Test results |
| Release | Approval policies | Deployment decisions |
| Operate | Drift detection | Runtime state |
This mapping is what allows teams to adopt DevSecOps without rewriting their development process. The SDLC continues to define delivery mechanics, while the DevSecOps lifecycle defines where security decisions are made and how they persist across change.
Read also: DevSecOps Architecture (A Practical Reference Model Teams Actually Use)
Phases of DevSecOps: what actually happens at each stage
The DevSecOps lifecycle is usually described in phases or stages, but the important part is not the names. What matters is that the same DevSecOps processes repeat at each step, even though the controls and owners change.
- What decisions are made
- Where enforcement happens
- Who owns the outcome
- What “done” looks like before moving forward
Read also: DevSecOps Frameworks in 2026: NIST, OWASP, SLSA Explained
Phase 1. Plan: DevSecOps planning phase before code exists
This stage exists to make later enforcement possible without manual reviews or last-minute exceptions. If a decision is not made in planning, it will be guessed later by a pipeline, a reviewer, or an auditor.
At this point, teams decide:
- Which services and environments are in scope
- What security requirements apply to them
- Which risks are acceptable by default
- Who owns those decisions
Threat modeling at this stage is lightweight and practical. The goal is not to document every possible attack, but to identify assumptions that must hold true later. Security requirements and acceptance criteria are written so they can be checked automatically during build, release, or runtime.
What “done” means in the planning phase
- Scope and ownership are explicit and traceable
- Security requirements are tied to services, not documents
- Acceptance criteria can be verified later without human interpretation
Cloudaware insight: Planning only holds if intent can be checked after deployment. Cloudaware helps teams establish service ownership and baselines early using CMDB relationships, so later stages can verify that runtime configurations and changes still match approved intent.
Phase 2. Code: secure development without slowing teams
This phase ensures that expectations defined during planning are reflected in how code is written and reviewed, without turning development into a bottleneck. The goal is not enforcement at any cost, but early signal where developers still control outcomes.
Teams define:
- Mandatory secure coding patterns
- Dependency policies and allowed sources
- Review conditions for higher-risk changes
- Ownership of remediation
Security signals at this stage remain developer-controlled. Secrets, unsafe defaults, and high-risk dependencies are identified before they become build failures or release blockers, which reduces noise later in the pipeline.
What “done” means in the code phase
- Ownership remains clear as code moves across repositories
- High-risk patterns are caught before CI
- Decisions made in code do not require reinterpretation later
Cloudaware insight: Code-level findings only become actionable if they retain service and ownership context downstream. Cloudaware preserves this context through CMDB relationships, so issues discovered later in build or runtime can still be traced back to the correct service and team instead of turning into generic findings.
Phase 3. Build: CI as the first enforceable security gate
The build phase is where security decisions become non-negotiable. Once a change enters CI, outcomes must be deterministic, so a build either produces a compliant artifact or fails.
At this stage, teams define:
- Mandatory checks for every build
- Blocking conditions for artifact creation
- Required evidence for audit and traceability
- Criteria for artifact promotion
Two control layers must both hold:
| Build-time validation | Supply chain integrity |
|---|---|
| Static analysis, dependency checks, and configuration rules validate what can be assessed deterministically | Artifacts are scanned, signed, and stored in controlled registries, ensuring that the artifact tested is the artifact released |
| The SBOM generated here provides a fixed reference of what the artifact contains, so later findings can be traced precisely |
What “done” means in the build phase
- Required checks run automatically and block on failure
- Only compliant artifacts are produced
- Build outcomes can be audited without reconstructing CI history
Cloudaware insight: Cloudaware maintains traceable records of build outcomes and policy evaluations, allowing teams to link artifacts to decisions without relying on fragmented CI logs.
Read also: The Cloud Log Fragmentation Problem - Why Enterprises Can't Track Where Their Logs Go
Phase 4. Test: security testing that drives release decisions
The test phase exists to answer a single question: should this version be allowed to move forward. Anything that does not influence that decision introduces noise and weakens enforcement.
At this point, teams define:
- Which security failures block a release
- Which results are advisory
- Which environments produce release-grade signals
- Who can override a failed test and why
Security testing becomes a unified decision surface. Dynamic testing, API testing, and other methods contribute to a single outcome rather than separate reports.
What “done” means in the test phase
- Results are tied to a specific release candidate
- Blocking conditions are explicit and consistently enforced
- Overrides are intentional, justified, and recorded
Cloudaware insight: Cloudaware links test results to services, environments, and approved changes, making it possible to reconstruct release decisions without manual investigation.
Phase 5. Release and deploy: policy-driven approvals instead of manual control
This phase controls how approved artifacts move into environments, where risk changes and enforcement must remain consistent. If promotion rules are unclear, teams fall back to ad hoc approvals, which slows delivery and breaks auditability.
At this stage, teams define:
- Which changes require explicit approval
- How rules differ across environments
- Which risks can be accepted automatically
- Who can override a gate
Release decisions must be repeatable and context-aware. An approval represents a policy decision evaluated against artifact state, environment conditions, and current risk, not a manual checkpoint.
Approval logic operates as: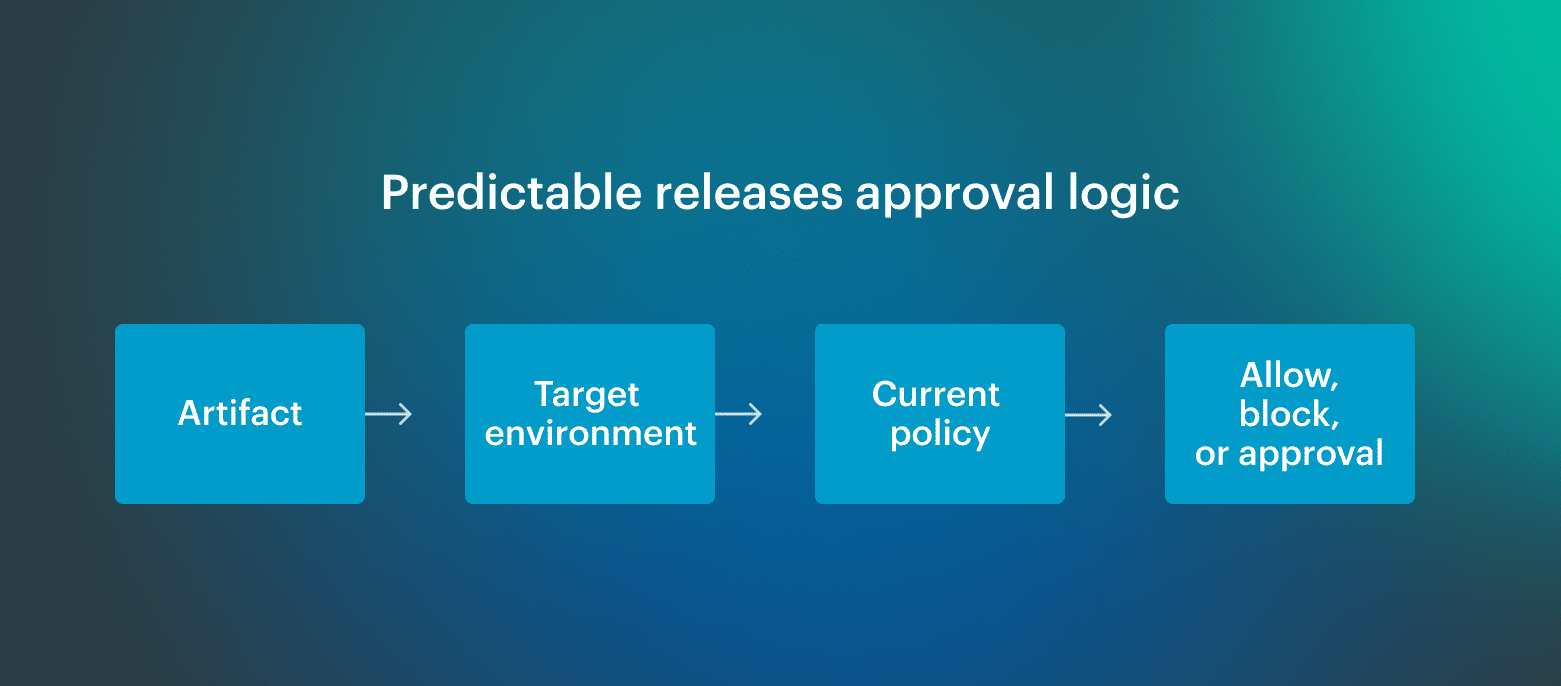 This keeps releases predictable while preventing approvals from becoming informal bottlenecks.
This keeps releases predictable while preventing approvals from becoming informal bottlenecks.
What “done” means in the release and deploy phase
- Promotion rules are explicit and enforced automatically
- Approvals are tied to policy, context, and ownership
- Every deployment decision can be explained after the fact
Cloudaware insight: Cloudaware routes approvals based on account, environment, and service group, ensuring consistent enforcement across multi-cloud environments while preserving traceable decision context.
Phase 6. Operate: DevSecOps infrastructure and runtime verification
This phase verifies that what is running still matches what was approved. After deployment, assumptions degrade due to configuration changes, platform updates, and operational fixes, so enforcement shifts from prevention to continuous verification.
Teams define:
- Which runtime conditions must always hold
- Which changes are acceptable without re-approval
- Which deviations trigger action
- Who owns runtime decisions
Runtime control is not about blocking change, but about detecting and evaluating deviation.
Two control perspectives apply:
| Baseline comparison | Drift evaluation |
|---|---|
| Live configuration is continuously compared to approved baselines across identity, network, compute, and platform layers. | When drift appears, the decision is not who changed what, but whether the change is acceptable under current policy. |
What “done” means in the operate phase
- Runtime state matches approved intent or deviations are explained
- Drift is continuously detected and recorded
- Ownership of runtime decisions is clear and stable
Cloudaware insight: Cloudaware continuously compares live configurations to approved baselines across AWS, Azure, and GCP, making drift visible in near real time without relying on periodic audits.
Phase 7. Monitor and feedback: closing the DevSecOps lifecycle
This phase ensures that runtime findings change future behavior instead of remaining isolated events. Monitoring is not an endpoint, but the mechanism that updates planning, build, release, and policy decisions.
Teams define:
- Which events require action
- Which findings change future controls
- Which fixes are permanent versus situational
- How quickly policies must adapt
Incidents expose gaps between intent and reality. Fixes resolve the immediate issue, but the lifecycle only improves when controls are updated so the same condition cannot pass again.
What “done” means in the monitor and feedback phase
- Incidents result in concrete changes to controls and policies
- Feedback reaches earlier stages without manual handoffs
- The same issue cannot reappear under identical conditions
Cloudaware insight: Cloudaware preserves change history, drift events, and compliance evidence over time, allowing teams to trace incidents back to decisions and update policies so future changes are evaluated with the same context.
Roles, ownership, and responsibility across the DevSecOps lifecycle
What teams need is not shared responsibility, but clear decision boundaries. Each stage in the lifecycle introduces moments where something can be allowed, blocked, or escalated. Someone must own that call, and that ownership must remain stable even as teams and systems change. This section clarifies the DevSecOps role across the software development lifecycle:
Who owns decisions at each stage
- Plan: architecture and security define constraints; engineering commits to scope
- Code and build: engineering owns fixes; security sets enforcement rules
- Test and release: platform enforces gates; leadership accepts residual risk
- Operate and monitor: platform owns runtime state; security updates controls
A practical RACI model for DevSecOps teams
A useful RACI assigns one accountable owner per decision, limits approvals to risk changes, and ensures outcomes are recorded. This is what keeps the DevSecOps lifecycle predictable instead of negotiable.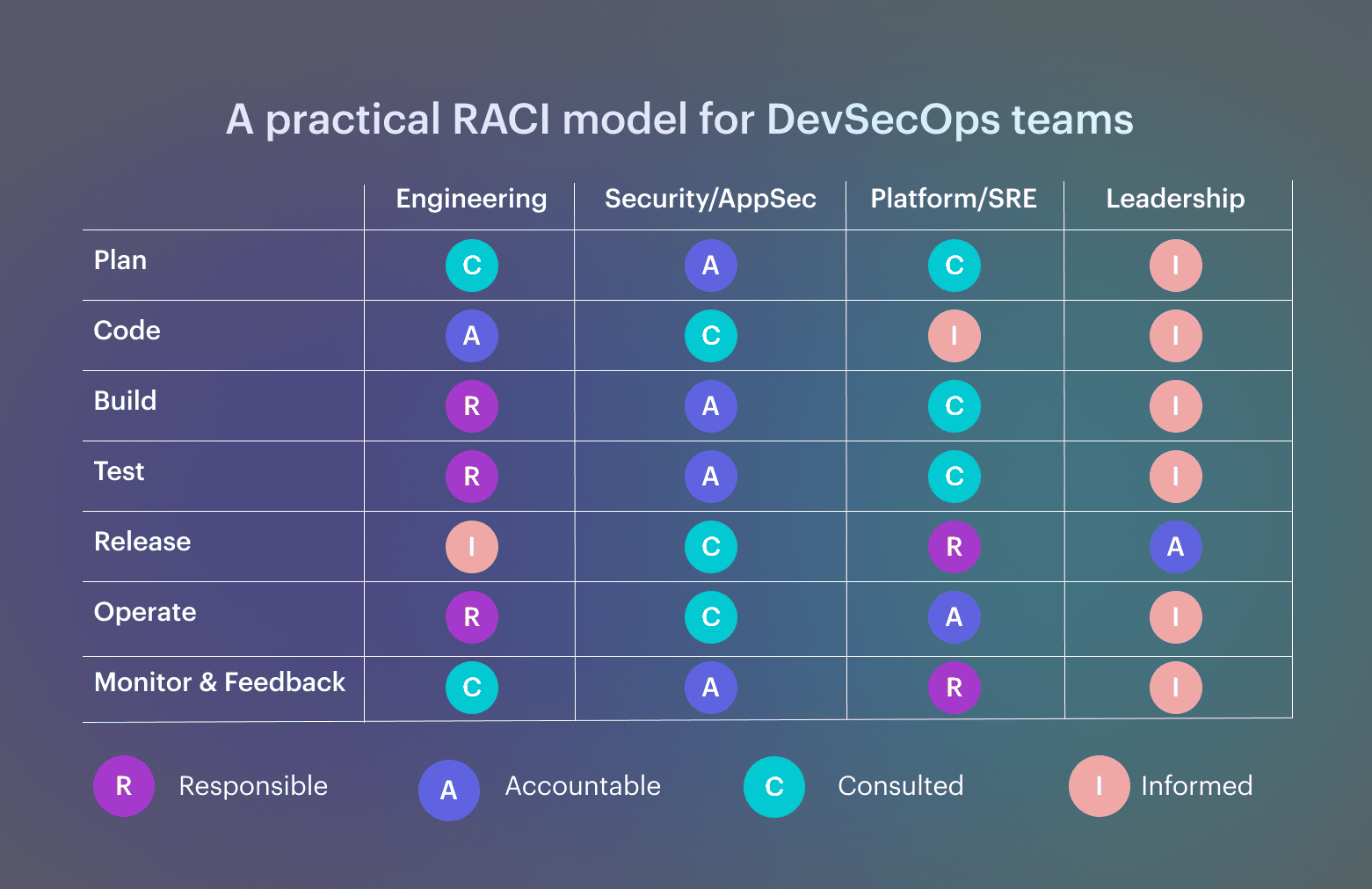 Note: One accountable owner per decision. Approvals only where risk changes. Evidence recorded automatically.
Note: One accountable owner per decision. Approvals only where risk changes. Evidence recorded automatically.
Evidence and measurement: how DevSecOps proves it works
Evidence answers “what happened and why.” Metrics show whether controls improve delivery or quietly slow it down. Without both, DevSecOps becomes opinion instead of an operating model.
Evidence you should be able to produce at each stage
Teams should be able to show, on demand:
- Plan: scope and ownership
- Build: checks and artifacts
- Release: approval logic
- Operate: drift handling
- Monitor: control updates
If evidence cannot be reconstructed without manual work, the lifecycle is fragile
Metrics that show DevSecOps maturity
Not all metrics are equal. Output metrics (number of scans, findings, tools) say little about control quality. Mature DevSecOps programs rely on outcome metrics drawn from established frameworks.
In security programs aligned with CIS benchmarks, teams usually track:
- Configuration drift rate, to see how often runtime settings diverge from approved baselines
- Mean time to detect misconfiguration (MTTD), which shows how quickly drift is noticed
- Mean time to remediate misconfiguration (MTTR), which reflects how effective the correction really is
These metrics indicate whether controls continue to hold after deployment, not just whether a release passed initial checks.
When FinOps practices are applied to DevSecOps, teams tend to measure:
- Change failure rate, including rollbacks caused by security or policy violations
- Cost of incidents and rework, as a practical signal of control quality
- Ratio of automated to manual approvals, which exposes how predictable and scalable the process is
Taken together, these metrics show whether the DevSecOps lifecycle produces stable outcomes, remains observable, and improves over time.
