Compliance Across a Multi-Cloud Setup Case Study
How Cloudaware helped unify inventory and compliance across AWS, Google Cloud, VMware, Kubernetes, and on-prem.

About
The organization runs a mixed estate across AWS, Google Cloud, vCenter, Kubernetes, and on-prem servers. Workloads include both long-lived systems and short-lived infrastructure that appears and disappears with deployments, which made it hard to keep scope, ownership, and compliance evidence consistent.
Challenges
As the environment expanded, compliance work started to break in predictable places:
- Difficulty maintaining a centralized, real-time inventory across multi-cloud and hybrid infrastructure.
- Gaps in compliance reporting and mapping to audit requirements, especially for NIST and CIS.
- Limited automation for detecting and remediating violations across different platforms.
- Manual, time-consuming evidence collection that delayed audits and increased effort.
- Custom controls were hard to enforce and measure, such as “All apps must have observability.”
What Cloudaware changed
A single inventory that covers cloud and on-prem
The organization used CMDB to consolidate asset data from AWS Organizations, Google Cloud, vCenter environments, Kubernetes clusters, and on-prem servers into one system. Inventory stopped being a set of disconnected exports and became a working view that teams could rely on when scoping audits and investigations.
One policy layer mapped to multiple
With IT compliance, policies were mapped to external frameworks such as NIST, CIS, and ISO using Cloudaware’s Unified Compliance Framework (UCF). That gave the team one control layer to run and report against, instead of building separate checklists per platform and framework.
Firewall controls evaluated in context
The organization defined custom policies for firewall configurations, including Palo Alto, to enforce a default-deny policy and related configuration standards. Cloudaware’s multi-object evaluation allowed firewall posture to be assessed alongside the connected cloud configuration and security group context, which is where real exposure tends to hide.
NIST coverage extended to legacy on-prem systems
For on-prem and legacy infrastructure, the team used UCF mappings to translate NIST controls into enforceable checks. Policy logic ran across relationships between systems, for example, server configuration, network setup, and access controls, so posture was measured as a connected system rather than a list of isolated findings.
Custom controls made enforceable
The organization implemented custom controls such as “All apps must have observability.” Those controls were expressed as policies and evaluated continuously using CMDB data extracts, so the requirement stopped being a slide in a standard and became something measurable in daily operation.
Kubernetes hardening aligned to CIS
Cloudaware delivered CIS-aligned policies for Kubernetes clusters, enabling the team to validate cluster configuration alongside the rest of the estate. The point was not separate reporting for Kubernetes, but one posture view across containers, cloud, and on-prem systems.
Daily evaluation with trustworthy “unknown” handling
Checks ran daily across the estate, with dashboards showing findings and gaps in one place. The “undetermined” state was used when permissions or access prevented a full assessment, which prevented false confidence and avoided noisy false positives.
Violations routed as work with ownership
Compliance violations were routed into Jira as owned work items. Issues were enriched with CMDB CI context, grouped where appropriate, and assigned based on routing rules so teams could remediate in the same workflow they already used.
Implementation
The rollout focused on connecting data sources first, then turning policies into a routine.
- Connected AWS Organizations, Google Cloud, vCenter, Kubernetes, and on-prem data sources to populate CMDB.
- Mapped required frameworks into IT compliance using UCF, starting with NIST and CIS and extending to other standards where needed.
- Built and deployed custom policies for Palo Alto firewall configuration and other environment-specific controls.
- Rolled out custom controls such as “All apps must have observability” and tied them to CMDB-backed evaluation.
- Enabled Kubernetes CIS checks for native clusters and aligned results to the same compliance view.
- Turned on daily evaluation and dashboards, using “undetermined” state handling where access was partial.
- Enabled Jira integration so violations became owned work items with CI enrichment and predictable routing.
Results
The organization moved from fragmented reporting to a single operating view of posture:
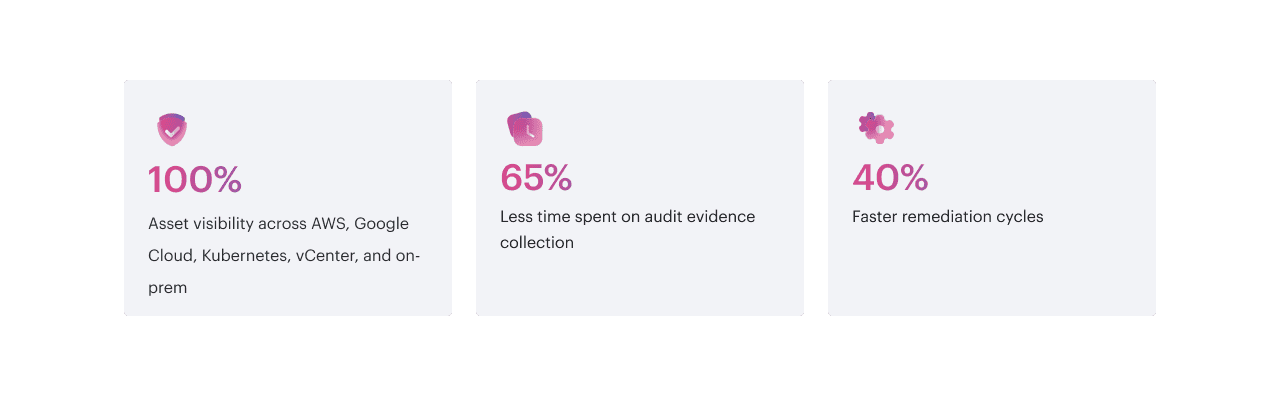
- Comprehensive coverage across AWS, Google Cloud, Kubernetes, vCenter, and on-prem systems with one inventory and one reporting layer.
- Firewall configuration checks, NIST evaluation for on-prem, Kubernetes CIS posture, and custom controls tracked in the same compliance system.
- Custom policy flexibility that allowed the team to enforce internal requirements without breaking alignment to external frameworks.
- Higher confidence in audit readiness because compliance status and evidence were available continuously, not assembled at the end.
Testimonial
“Before Cloudaware, we could run checks in each platform, but we couldn’t answer simple audit questions end to end: what exists, who owns it, and whether it meets policy right now. CMDB gave us a clean inventory across cloud and on-prem, and IT compliance turned NIST, CIS, and our own controls into something we could enforce daily. The Jira routing closed the loop, so findings stopped living in spreadsheets.”
Head of Security Compliance, Multi-cloud enterprise
Conclusion
Cloudaware CMDB and Cloudaware IT compliance gave the organization a practical way to run security posture across a mixed estate, including cloud, containers, VMware, and legacy on-prem systems. By anchoring policies to a unified inventory, mapping controls through UCF, and routing violations into Jira with the right context and ownership, the team reduced manual audit work and made compliance enforceable as part of normal operations.
Schedule a demo to see how Cloudaware can support compliance across your multi-cloud setup.
Read more case studies:
Faster Audits, Stronger Compliance Case Study
Automating PCI DSS Level 1 Case Study
Any questions? Contact sales
