Automating PCI DSS Level 1 Case Study
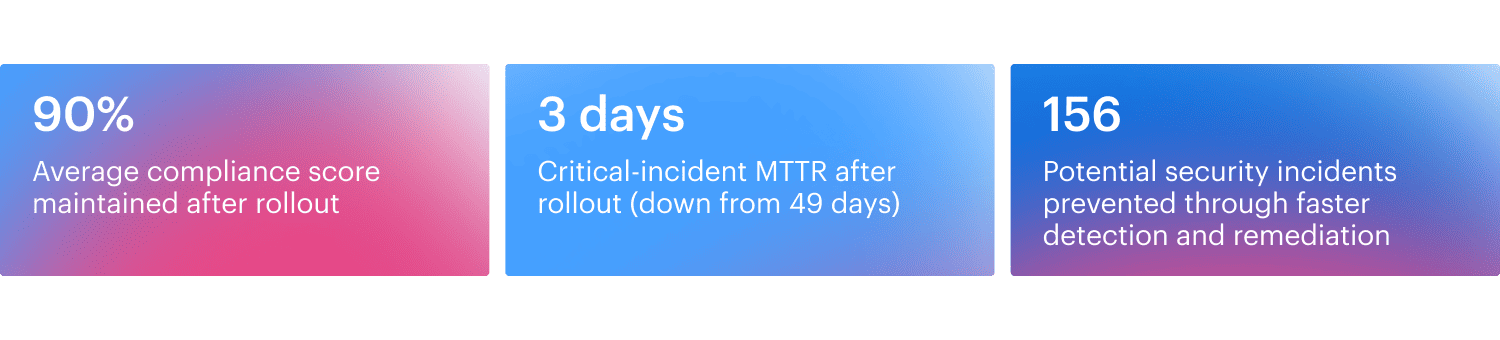
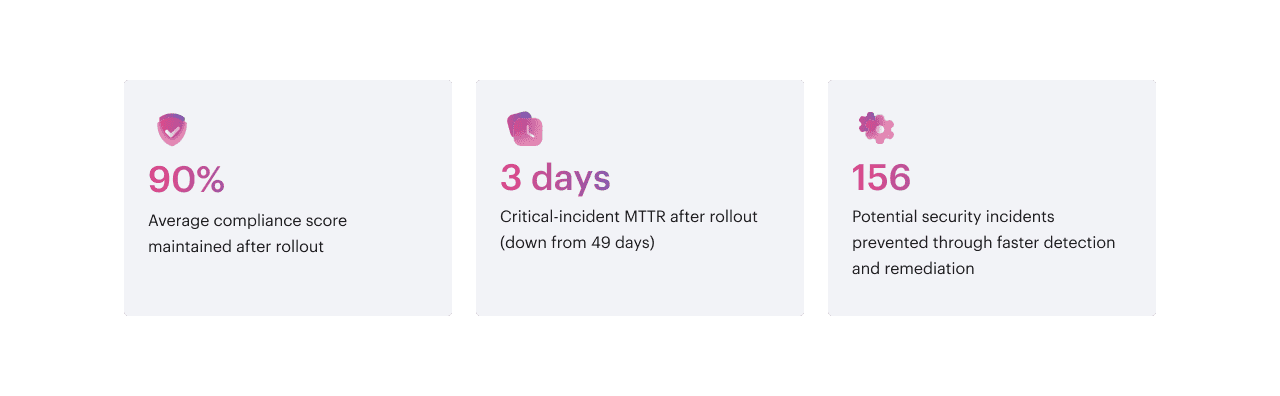
How Cloudaware Compliance Engine automated PCI DSS Level 1, kept 90% compliance, cut MTTR from 49 to 3 days, and prevented 156 incidents.
About
Company A is a financial services organization that processes payment data across multiple regions. Its cloud estate includes more than 200 AWS accounts supporting production workloads. As the footprint expanded, PCI DSS Level 1 stopped being a quarterly exercise and became a daily operations problem.
Challenges
The compliance program was getting blocked by basic execution gaps:
- Inconsistent security baselines. Accounts drifted from one another, so controls like encryption, IAM password policy, and logging were not applied the same way everywhere.
- Manual compliance checks. Validation depended on ad hoc reviews and periodic audits, which meant issues were found late and fixed under deadline pressure.
- No continuous enforcement. Findings could be identified, but there was no consistent mechanism to enforce controls and keep drift from coming back.
- Unclear ownership. Without application-level tagging, teams could not quickly tell who owned a resource, so remediation stalled.
What Cloudaware changed
Inventory and account structure kept current
Company A used CMDB as the system of record for AWS accounts and resources. Cloudaware connected the AWS Organizations management account through a CloudFormation stack that created an IAM role with an External ID, then used a StackSet to deploy the role across organizational units. CMDB stayed in sync as accounts and OUs changed, and new accounts were added by redeploying the StackSet to the right OUs. 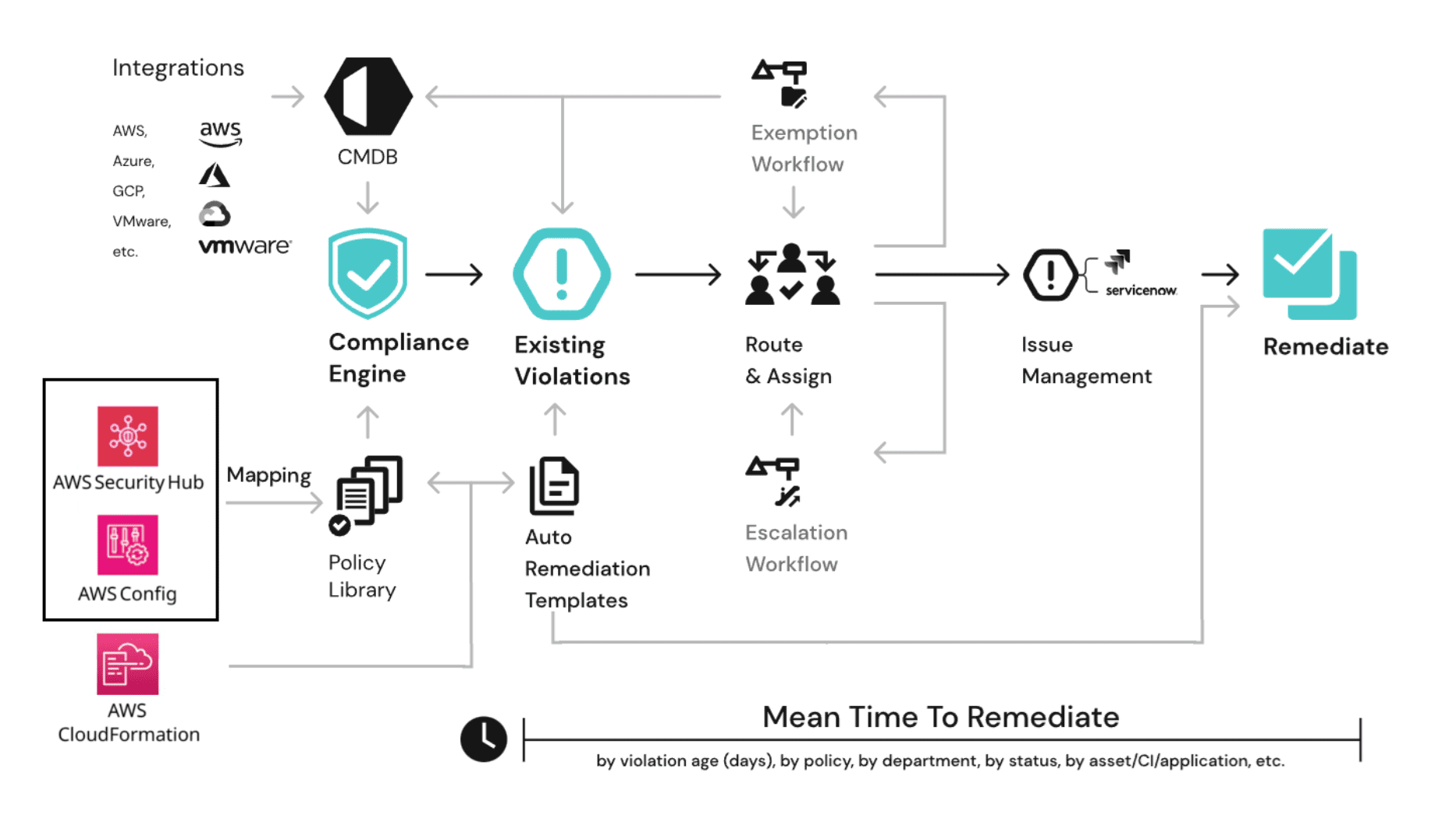
PCI DSS controls enforced continuously
Company A used IT compliance to start enforcing policy-based controls immediately, using 300+ prebuilt rules, then added custom policies for internal governance.
Policies were aligned out of the box to AWS Security Hub controls and mapped to broader frameworks that the organization already tracked, including CIS AWS Foundations, AWS FSBP, FedRAMP, NIST SP 800-53, SOC 2, and NIST CSF. This let the team run PCI DSS coverage inside one control framework instead of treating PCI as a separate reporting lane.
Change history and audit-ready evidence
AWS Config was integrated so the team could see when a resource became non-compliant, not just that it was non-compliant today. Config data filled coverage gaps for attributes not available through direct API calls, and it provided a clear trail for audits and investigations by tying violations to specific configuration changes. 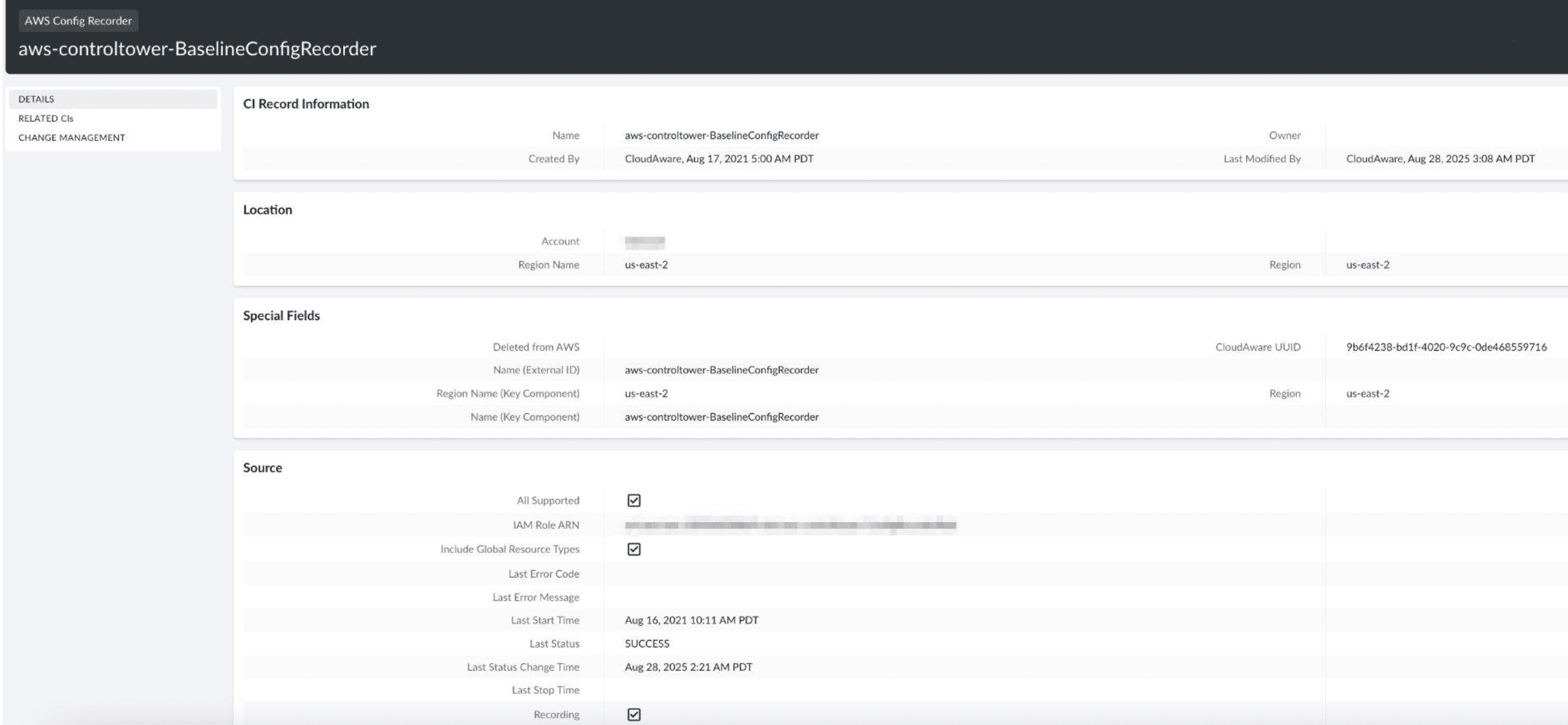
Ownership-based routing
Application Tags were enforced so every resource carried an owning application. That made accountability explicit and removed the “who owns this?” loop that slows down remediation. 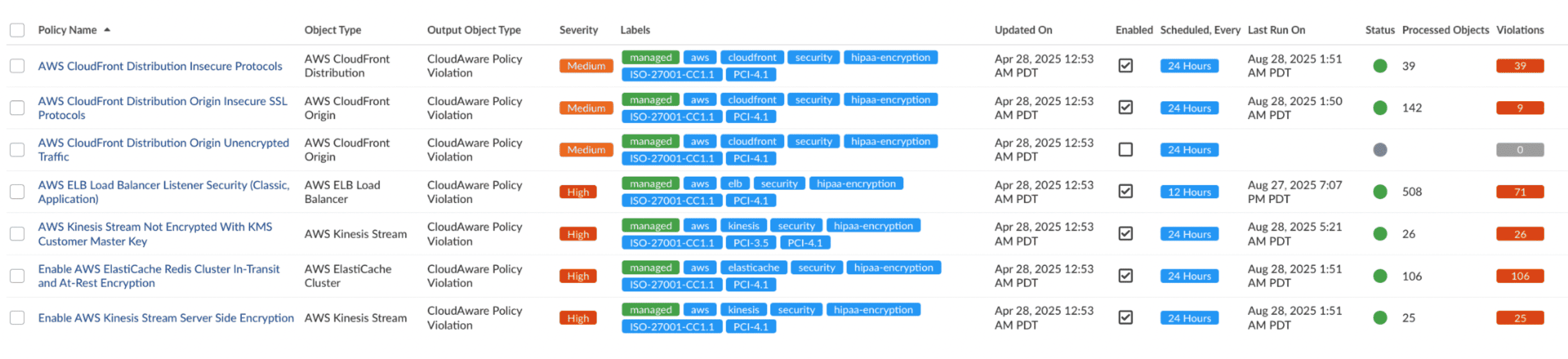
Violations turned into tracked work
We treated every policy hit as operational work, not a dashboard metric. Each violation became an incident with an owner pulled from Application Tags, and it stayed open until someone closed it with the right evidence. Those incidents were pushed into Jira, so teams worked them in the same queues they use for day-to-day fixes, instead of chasing findings across separate tools.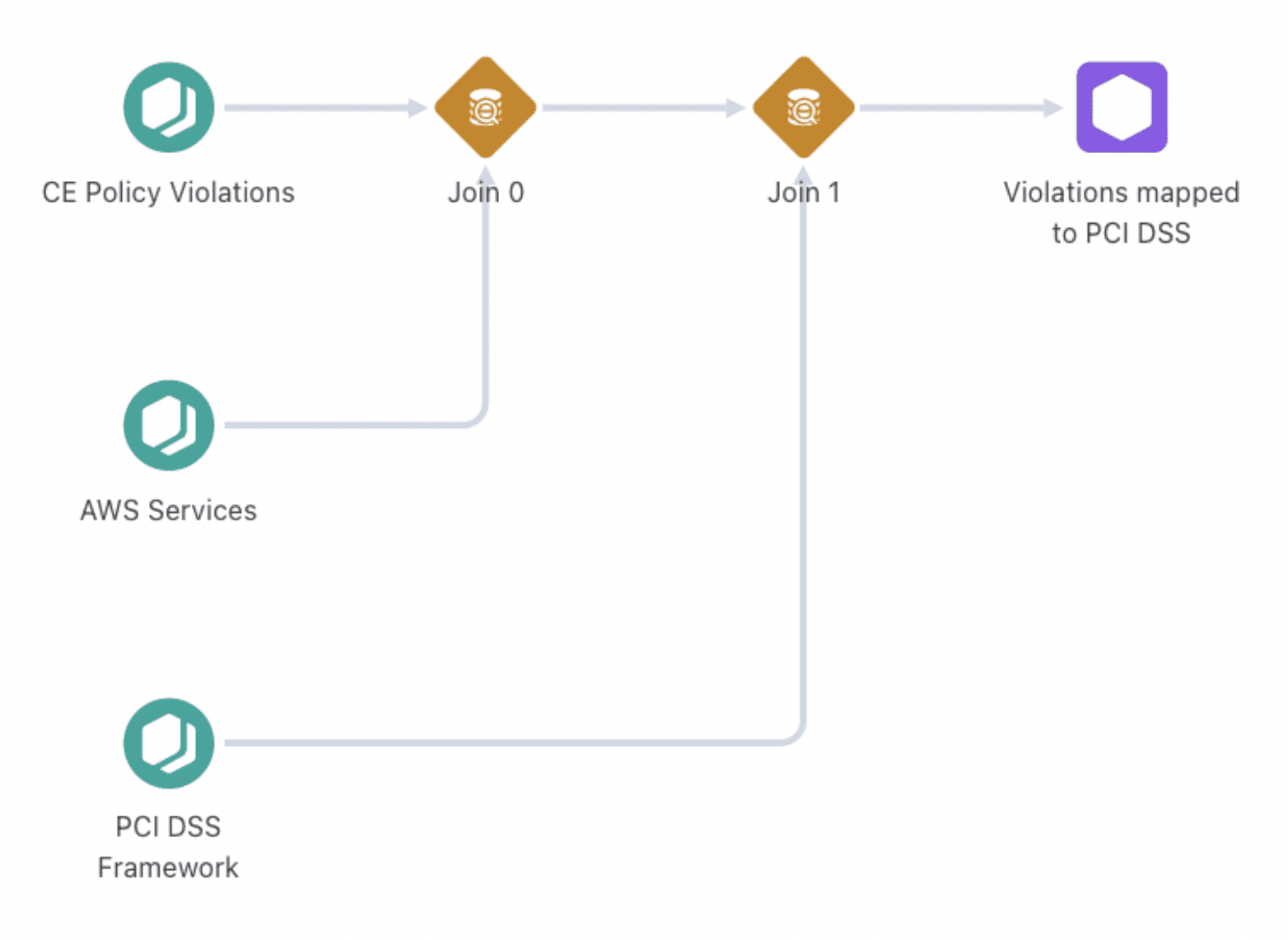
Implementation
The rollout was staged so coverage did not fall apart halfway through.
-
Connected AWS Organizations and deployed the cross-account role through CloudFormation and StackSets to get consistent access and populate the CMDB across accounts and OUs.
-
Wired in AWS Config, Security Hub, CloudTrail, GuardDuty, and Inspector so the compliance engine had the full picture: current configuration, configuration history, security findings, and the audit trail needed for investigations and reviews.
-
Enabled PCI DSS Level 1 policies in IT compliance using prebuilt controls, then added custom logic where needed.
-
Enforced Application Tags for ownership, environment, and sensitivity classification.
-
Enabled incident automation and Jira routing so violations were assigned and tracked.
-
Scheduled daily scans and near real-time alerts for critical and high-priority violations, supported by dashboards for trend and MTTR tracking.
Results
Testimonial
“Cloudaware’s Security Compliance Engine moved us from reactive checks to continuous enforcement. We now maintain 90% compliance and reduced incident response time by 85%.”
Chief Information Security Officer, Financial Organization
Conclusion
Company A used Cloudaware Compliance Engine to keep PCI DSS Level 1 controls enforceable across 200+ AWS accounts, with ownership and remediation wired into the workflow. CMDB defined scope, IT compliance enforced policies mapped to AWS controls, Application Tags fixed accountability, and incidents routed work into Jira until closure.
Schedule a demo to see how Cloudaware can support PCI DSS readiness in your AWS environment.
Read more case studies:
Faster Audits, Stronger Compliance Case Study
Automating PCI DSS Level 1 Case Study
Compliance Across a Multi-Cloud Setup Case Study
Any questions? Contact sales
