You didn’t land here because SAM is “interesting.” You landed here because a renewal is coming, someone wants a number by EOD, your inventory disagrees with procurement, and you’re about to get blamed for the gap. Again. I’ve been in that seat with teams running SAM across messy hybrid estates, and I’ve watched what actually holds up in real programs shared by ITAM and software asset management leaders from 2024–2026, not in theory slides.
- So let’s make this useful. What does “good” look like when SaaS sprawl is normal?
- How do you stay audit-ready without living in spreadsheets?
- Which usage signals are worth trusting when vendors change metrics mid-contract?
- What’s the simplest way to reclaim spending without breaking teams?
That’s what these software asset management best practices answer.
Key insights on software asset management best practices
The lecture isn’t what you came here for. You require the resources that ensure renewals proceed smoothly, audits remain uneventful, and ownership questions are clear. Here are the core software asset management best practices we’ll unpack in this article:
- Run SAM continuously. Quarterly baselines expire fast in the cloud. Refresh discovery often enough that your “position” is still true when Procurement asks for it.
- Stop debating counts. Define trusted usage signals per vendor. Install data, logins, consumption metrics, and device assignment. Pick what you’ll defend, document it, and use it consistently.
- Treat SaaS as a primary spend leak. Track activity monthly, set an inactivity threshold, reclaim seats before renewals, and check who actually needs premium tiers.
- Make ownership non-negotiable. Every licensable title needs a real owner, an app/service tag, and an environment label. Unknowns should age like bugs, not like “later.”
- Keep an audit pack ready at all times. Entitlements, evidence, exceptions with expiry dates, and a repeatable export format. When the email arrives, you shouldn’t scramble.
- Hard-wire procurement into your rhythm. Give them a 90-day runway with reclaimed candidates and usage position so negotiation starts from facts.
- Align SAM with FinOps on purpose. They should have shared tags, a common language, and a unified calendar. We aim to establish a single reality for spending and usage, rather than having two competing dashboards.
- Measure outcomes, not activity. Reclaim rate, time-to-answer “Where is X running?”, and percent of assets with owners. Everything that doesn’t move a KPI is just data hoarding.
- Treat strategic ITAM as the 2026 lever. Vendor prices rise faster than budgets. Your leverage is visibility + lifecycle decisions, not spreadsheet heroics.
Next, we’ll go one by one and make each practice executable.
Run SAM as a continuous practice, not “true-up season”
If your SAM program only “wakes up” when a vendor email lands, you’re doing emergency response. Ed Cartier’s point on xAssets is simple:
“The estate changes every day, so the truth has an expiry date. Treat SAM like hygiene, not a holiday.”
In real life “continuous” actually means that you’re trying to keep your risk surface and spend surface current enough that renewals stop being a surprise.
- Weekly: refresh discovery, flag “new titles,” spotlight top-growth vendors, and chase down unknown owners while the trail is still warm.
- Monthly: reconcile entitlements vs. what you’re seeing, review reclaim candidates, validate exceptions, and lock a baseline snapshot.
- Always capture “last seen” and change history so you can answer “when did this appear?” without archaeology.
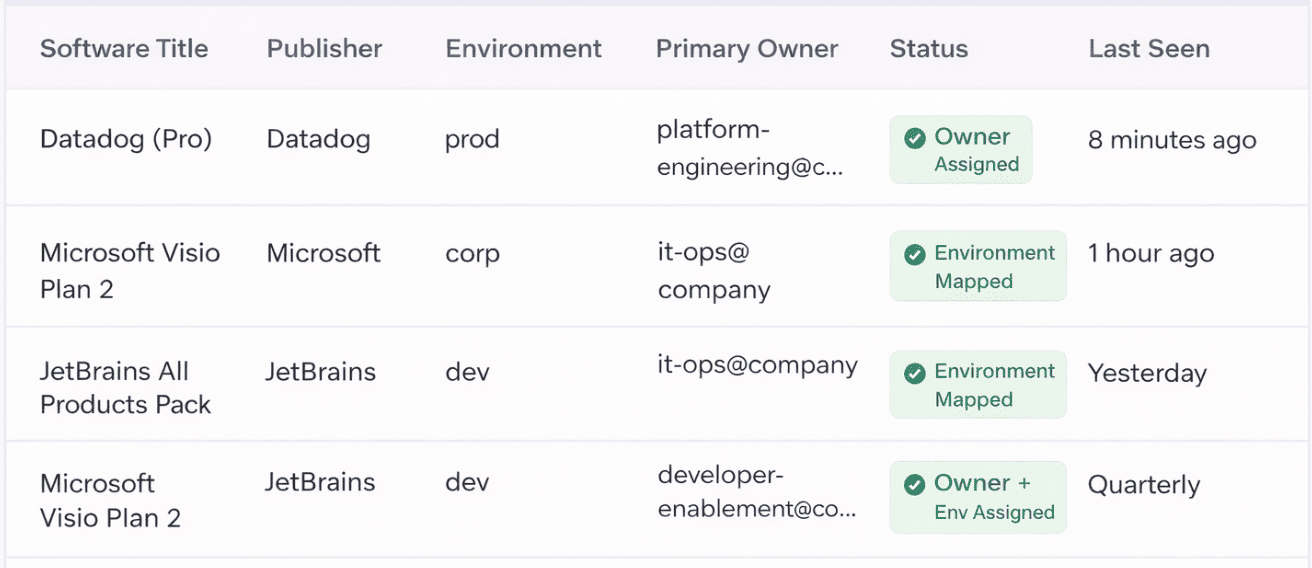
The piece most teams skip and then get blamed for is ownership. Not “someone in IT.” A real owner you can route questions to! Continuous SAM only works when every asset can be tied to a team, an app/service, and an environment boundary.
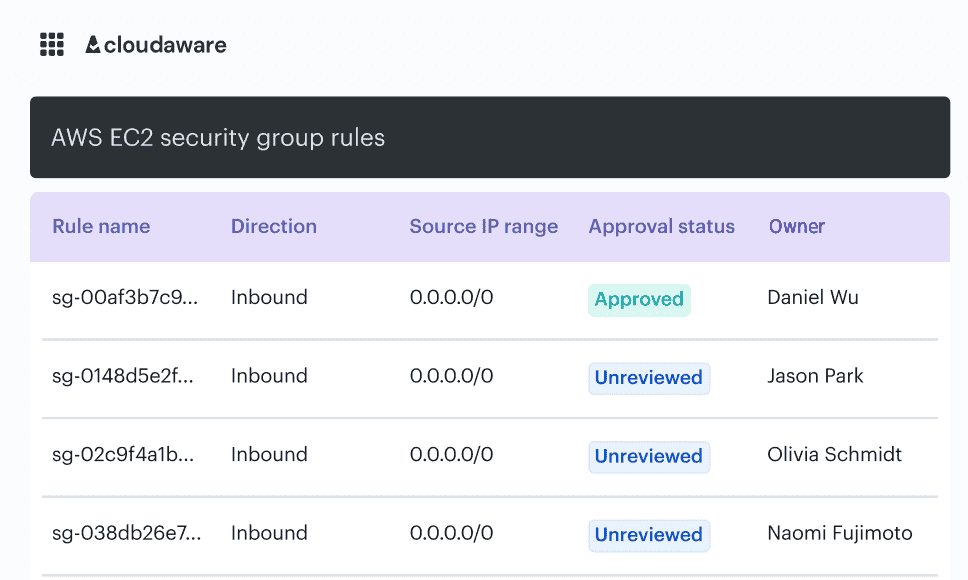
Here is an example of how it looks in a Cloudaware DevSecOps report:
Once you run SAM continuously, one question starts to matter more than “how many installs?” Which usage signals do you trust enough to stake your renewal position on?
Stop arguing about license counts. Start measuring license usage signals you trust
Phil Perfetti’s point hits because it’s the thing that turns SAM into a never-ending courtroom scene: “One number from procurement, another from discovery, a third from security tooling, and suddenly you’re litigating spreadsheets instead of managing risk.” ”.
His 2025 takeaway is basically “stop trying to win the count debate. Pick usage signals you can defend, then run the program on those.”
This is one of those answers to what are the leading SAM practices that sounds simple until you try it: define, upfront, what “truth” means for each major publisher. Not one universal metric. Vendors don’t work that way. Your job is to define a trusted evidence chain per product family.
What “usage signals you trust” looks like:
You build a small matrix and stop improvising during renewals:
- Signal type: install, execution/launch, login/activity, consumption, device/user assignment.
- Source: tool telemetry, directory/IdP, SaaS admin console, cloud billing, publisher-defined measurement.
- Quality rules: coverage %, freshness, deduping rules, identity mapping rules.
- Fallback: what you use when the “ideal” signal isn’t available.
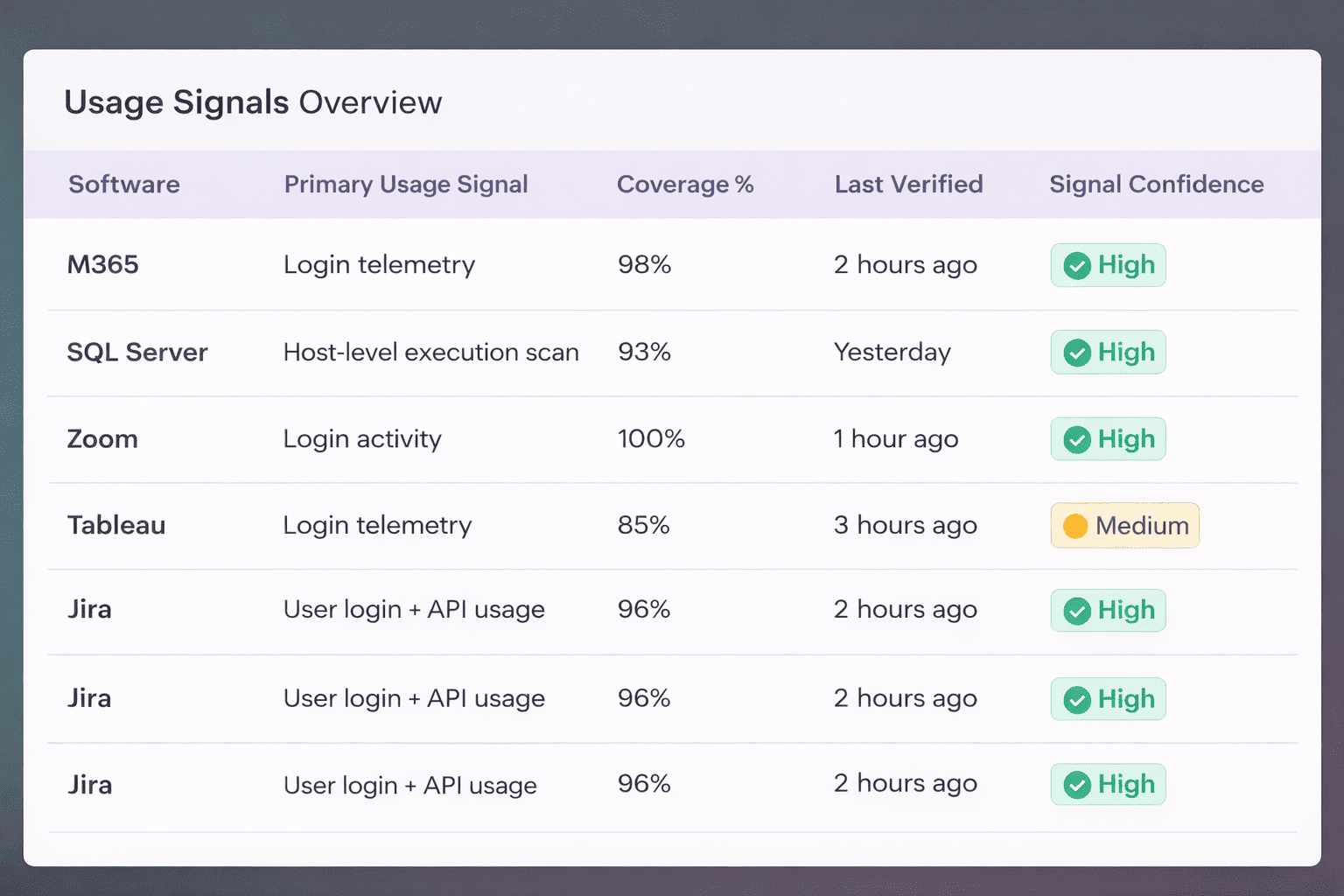
A software license usage dashboard example:
Perfection isn’t as important as consistency here. You should adhere to the same rules this month, next quarter, and when the audit letter arrives. That’s how you stop being the “license police” who are also blamed for “bad data.”
A tiny sanity test I like: If someone asks, “Why is this number different from last month?” you should be able to answer in two minutes:
- New assets appeared
- Ownership changed
- Usage dropped
- Measurement rules changed (and if they did, you document it)
If you can’t explain deltas, your counts will always be questioned.
Read also: 15 Software Asset Management Tools
Once you stop fighting over counts, the next trap shows up immediately. SaaS. Because even perfect counting doesn’t save you when licenses keep getting bought, forgotten, and renewed on autopilot 👇
Monitor SaaS usage to control spend
SaaS is where good SAM goes to die quietly. Nobody “installs” anything. People swipe a card, get a login, and six months later, you’re renewing 300 seats for a tool that 40 people touched last week. That’s why in this roundup of best software asset management practices in SAM, we push usage monitoring as a first-class control.
As Ed Cartier said, “I’ve watched too many teams lose budget battles because they couldn’t show a simple, defensible usage reality.” Source.
What to monitor so the data actually holds up in renewal talks: Track signals that answer “keep, cut, downgrade, or reclaim”:
- Activity freshness: last login or last meaningful action (not just “account exists”)
- Seat-to-human mapping: who owns the seat, and are they still employed or still in that team
- Role fit: how many users need the premium tier vs the basic tier
- Duplicate overlap: two tools doing the same job in different corners of the org
The workflow that stops autopilot renewals:
- Pull usage monthly for your top SaaS vendors by spend.
- Flag inactive seats with a clear threshold (30/60/90 days, pick one and stick to it.)
- Route the list to the app owner for a yes/no decision, with a deadline.
- Reclaim, then document what you did so next quarter isn’t déjà vu.
SaaS sprawl is also audit exposure, security scope creep, and vendor leverage. Usage monitoring gives you negotiating power because you’re walking into renewals with evidence, not vibes.
Read also: 13 Cloud Cost Optimization Best Practices from Field Experts
Once you have control over SaaS usage, the next challenge arises when a vendor approaches you. Can you respond the same way every time, with evidence, entitlement context, and repeatable reporting?
Treat audit response as an operating model: evidence, entitlement context, and repeatable reporting
Containers move fast. The old SAM habit of “we’ll review it later” doesn’t survive a cluster where teams ship images daily, and namespaces multiply overnight. If you want best practices for SAM in cloud security, you need controls that operate at the same speed as the platform.
Two guardrails that actually change outcomes:
- Admission control (prevent bad stuff from landing): put a policy engine in front of the cluster so misconfigurations don’t become production reality. Think: disallow privileged pods, block public images, require resource limits, and enforce approved registries. This approach serves as a preventative measure.
- Drift scanning (catch what changed after it landed): even with good pipelines, clusters drift. Manual hotfixes happen. Helm values get tweaked. A drift scanner tells you “this running state no longer matches your intended state,” which is exactly how policies rot quietly. Wiz’s Kubernetes security guidance calls out drift detection as a must in multi-cloud setups.
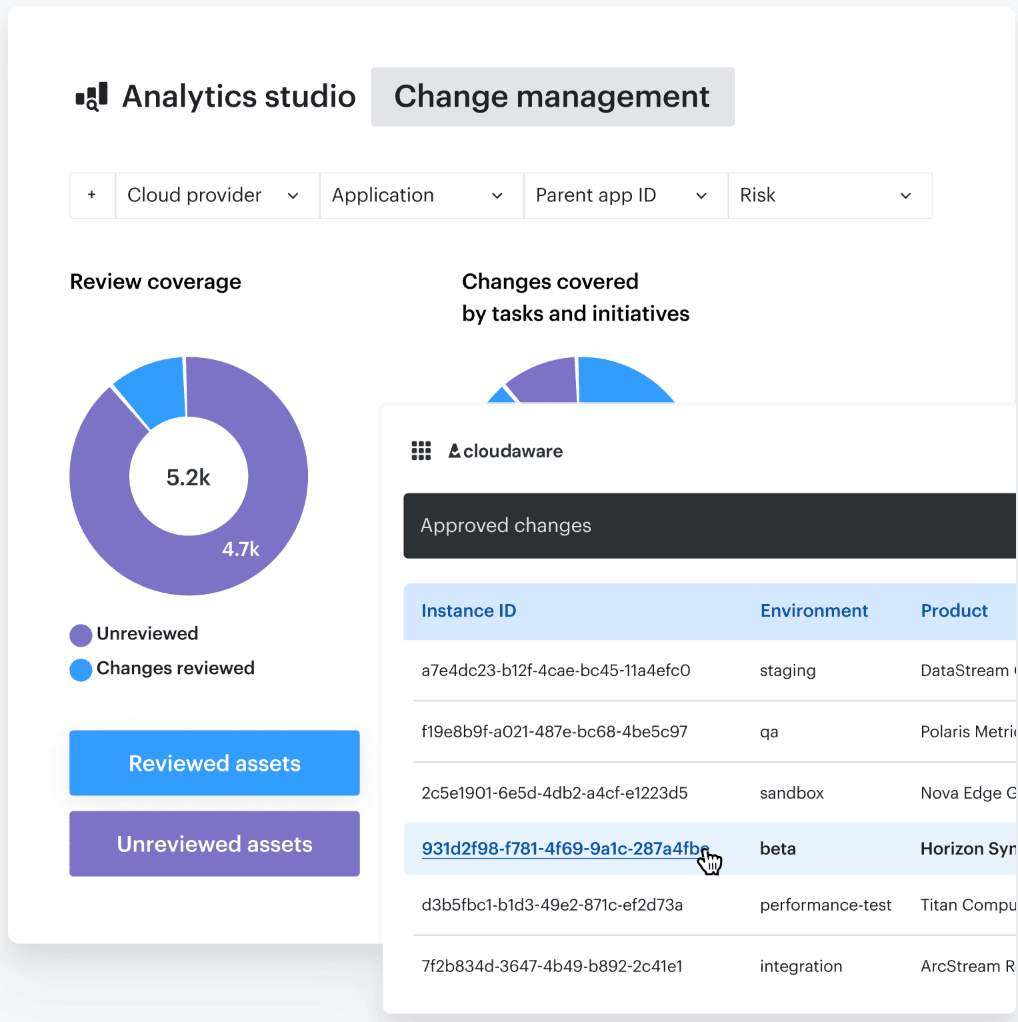
Here is an example of one of the dashboards Cloudaware users show during audit:
Treat your cluster guardrails like code you ship: version policies, review changes, tag releases, and keep a changelog that explains why a rule exists. That way, when an engineer asks “Why did my deploy get blocked?”, you’ve got a real answer that doesn’t start a war.
Once you’ve got guardrails that prevent chaos at runtime, the next fight is organizational
Align SAM with FinOps on purpose [shared language & governance]
SAM and FinOps used to live in different buildings. Now they’re in the same Slack channel, arguing over the same line items. Marketplace subscriptions, SaaS renewals, “committed” cloud spend that behaves like licensing, and vendor audits that suddenly ask for cloud usage context. If you don’t align them deliberately, you get duplicate reporting, mismatched numbers, and you, the SAM manager, become the translator and the scapegoat.
What alignment looks like when it’s not just a slogan:
Start with shared definitions. Then lock them into governance so they don’t drift.
- One vocabulary: “entitlement,” “consumption,” “allocation,” “owner,” “environment,” “scope.” Same meaning across SAM and FinOps, written down, used in reports
- One decision calendar: renewals, true-ups, reserved capacity reviews, and SaaS renewals. One pipeline, not two surprise meetings
- One exception process: a single place to log “we’re over because X,” with an expiry date and an owner who signs their name
That’s the core of best practices for implementing SAM in 2024–2026. Not more tools. Fewer contradictions.
You need a shared system of record that can answer both questions:
- SAM asks: “What do we own and are we compliant?”
- FinOps asks: “What did we spend and why did it move?”
Move from point-in-time SAM to near-real-time ITAM data
A quarterly baseline used to be “good enough.” Then cloud showed up and shortened the shelf life of an asset to hours, sometimes minutes. In the Anglepoint episode, Kris Johnson and Ron Brill call out that ITAM started as a point-in-time response to audits and renewals, but that pace doesn’t match modern environments anymore.
*As Ron Brill said, “*If a workload can spin up, scale, and disappear before your next inventory run, your numbers aren’t just stale. They’re misleading. That’s how teams end up doing the right work and still getting blamed for the wrong “truth.”
What “near-real-time” looks like in practice:
This isn’t about chasing perfection. It’s about shrinking the gap between “something changed” and “SAM knows.”
- Higher-frequency refresh for high-churn scopes: cloud accounts, Kubernetes clusters, ephemeral compute, marketplace purchases.
- Last-seen + change history as default fields: so you can explain deltas without guesswork.
- Ownership and environment boundaries attached early: the minute you detect a thing, you should know who to ask about it.
That’s where best practices for SAM in cloud security start paying off, because security teams care about what’s running right now, not what existed at quarter end.
If you’re using Cloudaware as your ITAM backbone, the win is speed-to-context. Discovery feeds an inventory that already understands environment, owner, and scope.
Then your SAM conversations stop being “is this real?” and become “is this allowed, is it used, is it worth paying for?” That’s the difference between reactive cleanup and SAM security best practices that actually scale.
Once you’ve got fresher data, the uncomfortable question shows up fast. Are your SAM tools effectively driving outcomes, or are they primarily gathering data that may lead to future discussions?
Get ROI from your SAM tools by focusing on the outcomes they should drive
If your SAM tool’s main output is a prettier inventory, you didn’t buy a program. You bought a database. Ron Brill’s point in the Anglepoint “IT Asset Management 2025 priorities” conversation is that ITAM leaders have to stop measuring effort and start measuring outcomes that the business actually feels. Otherwise, the tools look “busy” while costs and risk keep climbing.
Now, speaking as Ron for a minute, here’s the filter I use.
1️⃣ First, decide what the tool must change
Pick outcomes that map directly to money, audit exposure, and security posture. Three is enough.
- Spend outcome: reclaimed licenses before renewal, avoided purchases, downgraded tiers that weren’t used
- Risk outcome: faster audit response time, fewer unknown assets, clean evidence trail
- Security outcome: clearer scope for controls and exceptions, fewer “who owns this?” escalations. That’s where best practices for SAM in cloud security stop being a poster and start being a number
2️⃣ Then, turn those outcomes into boring, trackable KPIs
This is where most teams get relief because the conversation stops being emotional.
- Time to answer “where is Product X running?”
- Percent of licensable titles with a real owner
- Number of inactive SaaS seats reclaimed per month
- Delta between discovered usage and paid entitlements for top vendors
- Audit pack readiness time, from request to export
Those are SAM security best practices in disguise. They force accountability and keep your data usable.
Hard-wire Procurement + ITAM collaboration because licensing models and costs are changing fast
When Procurement and ITAM run on separate tracks, you can predict the ending. Procurement negotiates based on what was bought. ITAM reports based on what’s actually used. The renewal lands and the numbers don’t match, so everyone looks at SAM like it’s a data quality issue. It’s not. It’s a governance issue.
Ron Brill talks about these shifting priorities in the “IT Asset Management 2025” episode, and this is one of the most practical takeaways you can steal for your own program.
The collaboration model that works when the org is moving fast:
- One renewal runway. 90 days out, ITAM provides the usage position and reclaim candidates. 60 days out, Procurement opens vendor conversations with that reality, not last year’s purchase order.
- One “buy” gate. No new software purchase or seat expansion without an owner, environment scope, and a plan for deprovisioning. This is where SAM implementation best practices stop being aspirational and start being enforceable.
- One set of renewal artifacts. Procurement gets the same pack every cycle: current inventory, deltas since last snapshot, usage signals, exception list with expiry, and an approved baseline position. If you change the pack each time, you’re training vendors to poke holes.
Why this matters even more in the best SAM practices for cloud environments:
Cloud marketplaces and SaaS bundles blur the line between “cloud spend” and “software contract.” A subscription can show up in Azure billing, renew like a SaaS contract, and still behave like a license audit risk. If Procurement doesn’t see the usage context, you overbuy. If ITAM doesn’t see the commercial terms, you can’t defend your position.
Treat ‘FinOps + ITAM’ as one practice to reduce waste and audit exposure
Once you’ve wired Procurement and ITAM together, the next leak shows up somewhere else. Cloud spend is being optimized in one dashboard. SaaS renewals live in a spreadsheet. Licensing risk gets chased in email threads. Data center contracts sit in a folder nobody opens. AI spend sneaks in as “experimentation.”
Same company, five versions of reality.
That’s why treating FinOps and ITAM as one practice isn’t a buzzword. It’s the only way you stop paying twice for the same value.
Build one operating model that answers two questions with the same data:
- What are we running, and who owns it?
- What are we paying for, and what changed?
When those answers come from separate systems, you get blind spots. Blind spots become waste. Waste becomes audit exposure because nobody can prove scope, ownership, or usage fast.
What this looks like on the ground
Instead of merging teams overnight you’re aligning on three shared control points:
- One inventory backbone. Every scope feeds the same asset record with owner, environment, lifecycle status, and “last seen.” That’s the spine for SAM security best practices because it lets security and audit teams scope controls based on real context, not guesses.
- One set of tags that means something. Cost center, app/service, environment, data sensitivity. If tags are optional, reports become fiction. If tags are enforced, you can trace spend and risk to the team that can actually fix it.
- One monthly “waste + exposure” review. Not a meeting marathon. A short review of: unused licenses, idle cloud resources, duplicate tools, expiring exceptions, and new spend categories like AI. This is where best practices for securing SAM pipeline suddenly become practical, because you can gate new spend with ownership and policy expectations before it scales.
Make strategic ITAM your cost-optimization lever in 2026
Budgets aren’t stretching, vendors are. So “cut 10%” can’t be the strategy anymore. Strategic ITAM becomes the lever because it’s the only function that can connect what you’re paying for to what’s actually being used and who can turn the knob.
As Trent Allgood’ said, “If you can’t trace spend to ownership and lifecycle decisions, every renewal becomes a gamble. Strategic ITAM flips that. It turns renewals into a managed pipeline where savings fund the next wave of modernization, instead of begging for a new budget.”
The “strategic” shift:
- Stop optimizing line items. Start optimizing decisions. Pick a short list of high-impact publishers and marketplaces, then manage them like products: usage position, entitlement position, owners, renewal dates, and a reclaim plan.
- Make lifecycle visible and enforceable. If an app is sunsetting, the licenses don’t get a “quiet renewal.” If a team is piloting AI tooling, it gets tagged as pilot with an end date, not left to grow roots.
- Operationalize evidence, not opinions. This is where SAM security best practices quietly become a cost practice too. When you can prove scope and ownership, you can confidently cut or re-negotiate without triggering risk panic.
Pro tip: Apply SAM version control best practices for your rules. Normalize titles, document the measurement approach, track changes to logic. When the number moves, you can explain why in two minutes.
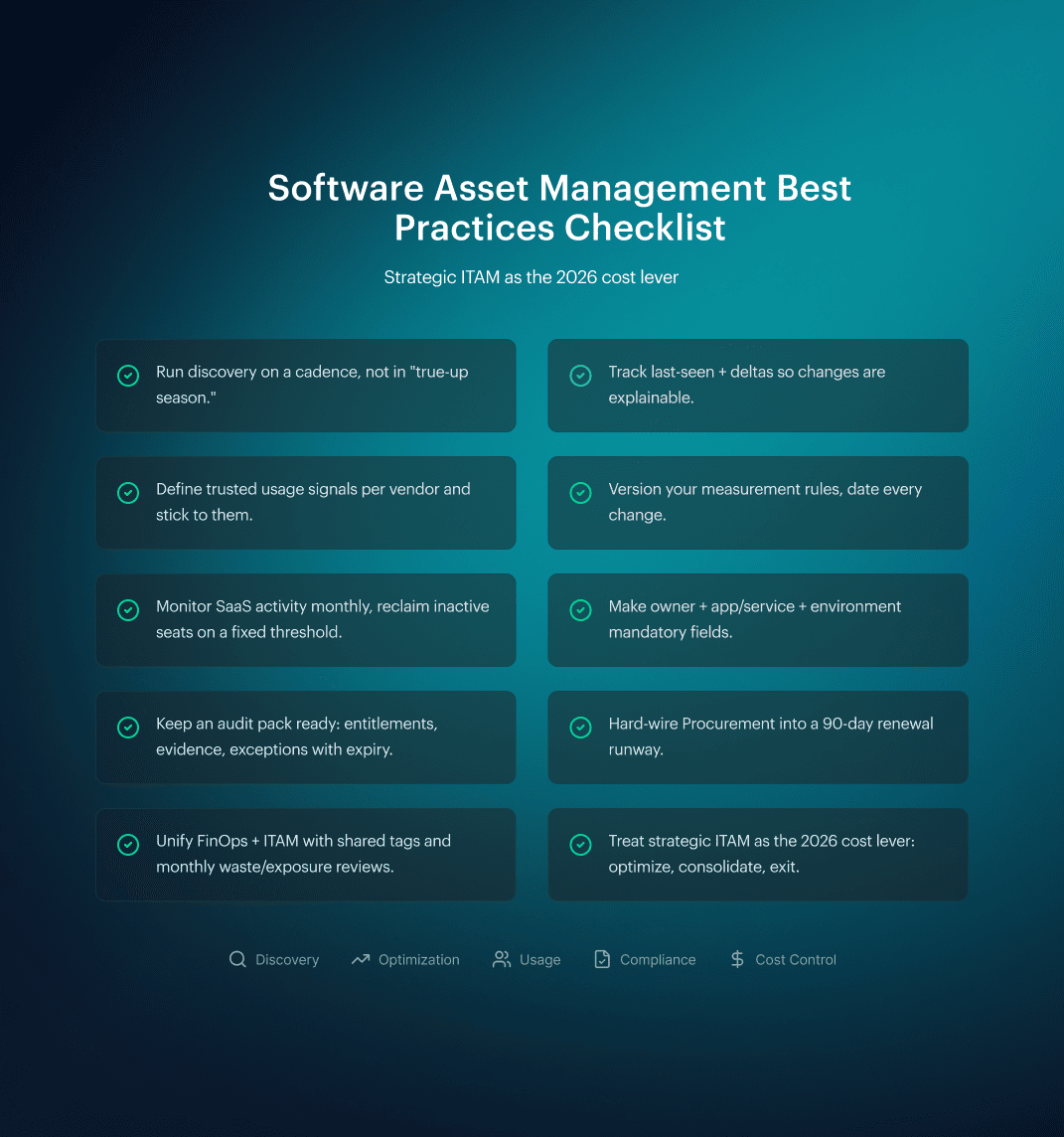
Alright, now that the “why” is locked, let’s make this executable. Here’s the software asset management best practices checklist you can run monthly without becoming the villain in every renewal thread.
Software asset management best practices checklist
You’ve done the hard part already. You’ve moved SAM out of “true-up season,” stopped the counting fights, pulled SaaS into scope, and got Procurement/FinOps speaking the same language. Now you need something you can run like a rhythm. Not a manifesto. A set of checks that keeps you audit-ready and cost-aware even when the estate changes daily.
This is the software asset management best practices checklist I’d put on the wall for any team:
How Cloudaware helps you actually do Software Asset Management
If your SAM reality is still “inventory export → pivot table → argument,” Breeze is the part that changes the game.
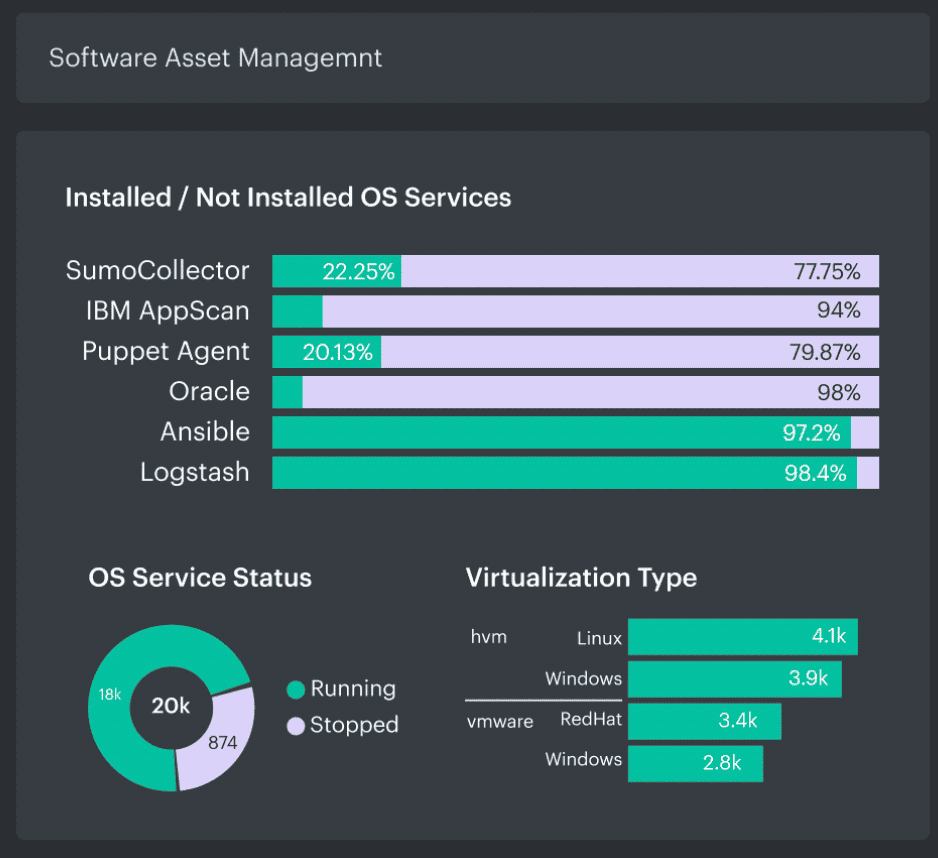
Breeze is Cloudaware’s discovery + config management agent that streams OS-level facts into the CMDB (users, services, mount points, etc.), and it also lights up modules like Vulnerability Scanning, Patch Management, CIS Benchmarking, and Event Monitoring.
What Breeze gives a SAM Manager:
- Installed software evidence you can defend. Breeze ships with discovery plugins including Software Asset Management, OS packages, upgradeable packages, OS services, and more. That’s how you stop relying on “we think it’s installed” and start working from host-level truth.
- A deployment story that doesn’t wreck your week. Breeze needs outbound TCP 443 only, no inbound connections, and it’s designed to run in private networks with no public IPs.
You can deploy it via Kubernetes, AWS Systems Manager, or Microsoft Intune. - Less babysitting after rollout. Breeze v3 is built to be self-updating and self-healing, so you’re not running an “agent upgrade program” as your side hustle.
- The SAM conversation shifts from counts to decisions. Once the CMDB has OS-level software signals flowing in, your reviews stop being “is the inventory wrong?” and turn into:
- Is it installed where it shouldn’t be?
- Is it upgradeable but lagging?
- Is it present but not needed?
And because it’s Cloudaware, that same record can sit next to cost, security, compliance, and ownership context, instead of living in five different tools.
