Security engineers, DevOps leads, and CISOs throw AppSec and DevSecOps into the same conversation all the time, often meaning entirely unique things. Vendors worsen it by packaging both under one shiny promise, so teams buy a tool, assume they covered the problem, and only spot the gap after a breach, a failed audit, or a risky release that slips through CI/CD.
That is the real stake behind AppSec vs DevSecOps.
By the end of this article, you’ll know exactly where each one fits, where they overlap, and how to use both without slowing delivery or weakening your security posture. We’ll explain:
- What changes when DevSecOps AppSec decisions are made in the same pipeline but owned by different teams?
- How far does shift-left security really get you before runtime risk, cloud drift, and broken approvals start telling a different story?
- Why do some teams move fast with confidence while others ship just as fast and quietly accumulate risk they can’t trace back later?
- And when a release looks clean on paper, what actually proves it was safe to push?
Key insights on AppSec vs DevSecOps
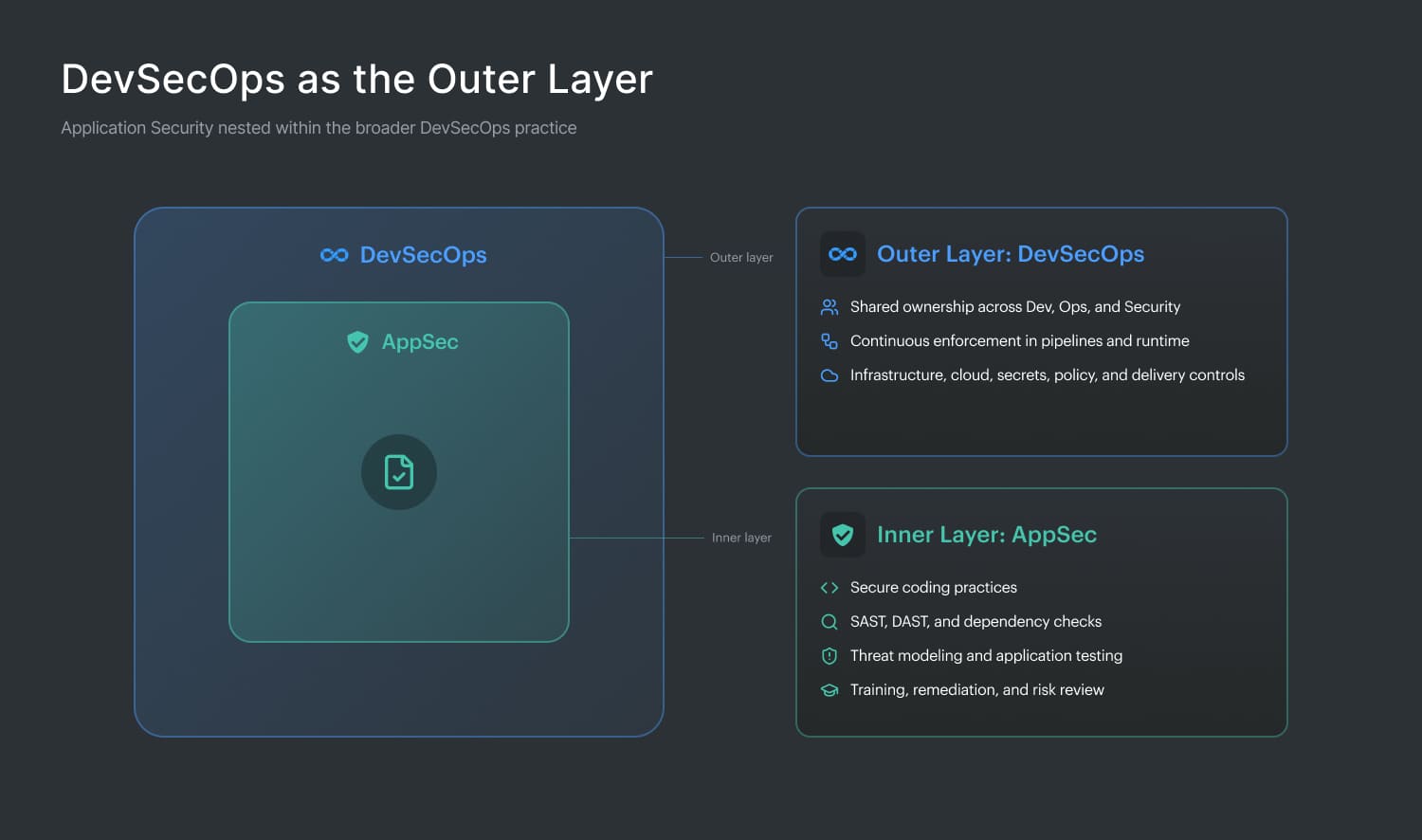
- Teams get confused because AppSec and DevSecOps often share tools, but they do not own the same problem. AppSec goes deep on the application itself: code, dependencies, APIs, and runtime behavior. DevSecOps looks at the whole delivery path, from commit to pipeline to cloud runtime.
- AppSec is the practice layer. DevSecOps is the operating model. That framing clears up a lot of bad decisions fast, especially when a team is trying to figure out who owns testing, approvals, remediation, and release controls.
- Scope is where the gap shows up first. A service can pass SAST, DAST, and dependency scans and still be risky in production because the IAM role is too broad, the bucket is public, or the container is deployed with weak network rules. Secure code does not automatically mean secure delivery.
- Ownership changes the outcome just as much as tooling. Traditional AppSec can stay concentrated with security specialists. DevSecOps only works when developers, platform teams, and security share responsibility in the flow of work. Otherwise, you get faster handoffs, not a stronger model.
- Timing matters more than most teams admit. Periodic reviews catch issues eventually. Continuous checks catch them while the developer still remembers the change. That is usually the difference between a quick fix and a backlog item that sits around for 30, 45, or 60 days.
- Tooling is another place teams fool themselves. Automating a few AppSec scans in CI/CD does not mean you now “do DevSecOps.” You have one ingredient in place. The full model also needs policy enforcement, pipeline controls, infrastructure checks, and cloud context.
- Metrics tell you what each model is optimizing for. AppSec usually cares about backlog health: critical findings, fix rate, MTTR, and coverage. DevSecOps cares about delivery health: gate pass rate, remediation velocity, build friction, and how many issues still escape into production.
- Mature teams do not really choose one over the other. They build solid AppSec fundamentals, embed them into DevSecOps workflows, and then add cloud visibility so findings can be prioritized by real exposure, not just scanner severity.
What is AppSec (application security)?
AppSec is the discipline of protecting software applications from security threats across the full lifecycle: design, development, testing, deployment, and ongoing maintenance. The core question is simple, but the work behind it is not: Is this application secure? That means looking at the application layer itself, the code, the logic, the dependencies, the APIs, the way data moves through the system, and the places attackers usually probe first.
In practice, AppSec is where teams work to reduce software vulnerabilities before they turn into production risk.
This discipline existed long before DevOps became the default operating model. A lot of AppSec grew out of waterfall-era security reviews, manual vulnerability assessments, and scheduled penetration testing late in the release cycle.
The tooling is broader now, but the goal is familiar: find weaknesses early, understand the real exploit path, and fix them before they become expensive. That is why mature programs combine
- Secure coding standards with threat modeling
- SAST for static analysis
- DAST for dynamic analysis
- IAST
- Software composition analysis
- Code review
- WAF controls
- Targeted tests against issues mapped to the OWASP Top 10
In real organizations, AppSec is both a practice and a job function. You see it in AppSec engineers, security architects, product security teams, red teams, and bug bounty programs. It also connects directly to compliance work, especially in regulated environments where PCI DSS, ISO 27001, or NIST SSDF requirements shape release processes and evidence collection.
So when a team talks about application security, AppSec usually owns the depth: how the app is tested, how risk is validated, and how findings are prioritized. AppSec is the practice of application security. DevSecOps is the how and when.
What Is DevSecOps?
DevSecOps is the operating model for building security into software delivery from the first commit onward. Where AppSec focuses on whether the application itself is secure, DevSecOps looks at how security shows up across the full delivery path:
- CI/CD pipeline,
- release controls,
- secrets management,
- build integrity,
- deployment workflows,
- and the environment the app runs in.
Checks occur continuously, rather than during a late review when the code is already packed into a release, making rework costly.
That broader scope is what makes the comparison matter. In a DevSecOps AppSec model, AppSec tools are still essential, but they sit inside a larger system of security automation, shared ownership, and rapid feedback. A scanner alone does not create secure delivery. Teams still need real developer security habits, clear policies, and a working security culture.
In cloud environments, the scope expands again. Now, infrastructure as code, container security, policy as code, and cloud drift are also part of the security conversation. DevSecOps is the operating model. AppSec is one of its critical inputs.
Your uploaded style file also appears to have expired, so if you want me to re-check its exact phrasing and match it even closer, re-upload it and I’ll tune this further.
Read also: 5 DevSecOps Roles and Responsibilities: Teams Structure
What is the difference between AppSec vs DevSecOps
To shape this section, I pressure-tested the argument with two Cloudaware DevSecOps experts, Valentin Kel and Igor K., because this topic gets fuzzy the second people leave the glossary and step into a real pipeline.
Definitions usually are not what trips teams up.
The mess starts in practice, when ownership blurs, tools get stacked without a plan, and nobody can fully explain why release friction is growing while risk is still slipping through.
That is the heart of AppSec vs DevSecOps. One team is tracking software risk at the application layer. Another is trying to protect the whole delivery system, from commit to cloud runtime. On paper, those sound adjacent. In production, they create different workflows, different bottlenecks, and very different blind spots.
| Dimension | AppSec | DevSecOps |
|---|---|---|
| Scope | Application layer, code, dependencies, runtime app behavior | Full SDLC, infrastructure, cloud environment, pipeline integrity |
| Primary question | Is this application secure? | Is security embedded in how we build and ship? |
| Ownership | AppSec team, security engineers, sometimes QA | Shared across Dev, Ops, and Security |
| Timing | Often at testing gates, pre-release, periodic audits | Continuous across every commit, build, and deployment |
| Core tooling | SAST, DAST, IAST, SCA, WAF, pen testing | All AppSec tools plus IaC scanners, CSPM, secrets detection, container scanning, |
| Cultural model | Security as a function, often separate from engineering | Security as a shared engineering responsibility |
| Success metrics | Vulnerability count, CVSS scores, fix rate, MTTR | Pipeline gate pass rate, remediation velocity, MTTD, security-to-shipping ratio |
| Cloud relevance | Focused on application-layer risks | Extends to cloud misconfigurations, IAM drift, infrastructure policy violations |
| Failure mode | Security becomes a release bottleneck, findings pile up | Fast pipelines ship code that passes gates but fails in cloud context |
Let’s break those down one by one, with the cloud reality and the security silos, most teams are still fighting.
Difference #1. Scope: application layer vs the entire delivery system
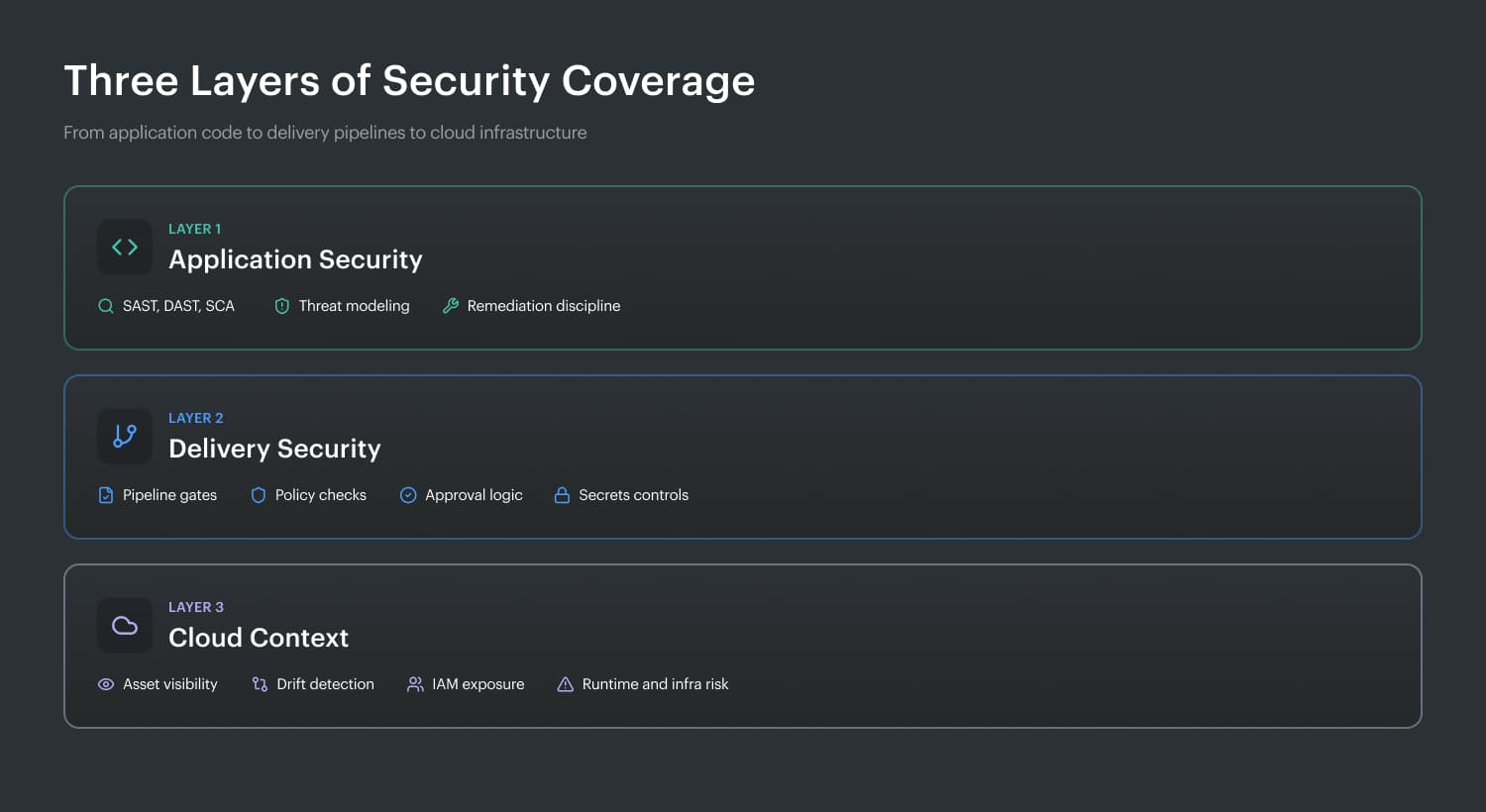
This is where DevSecOps vs AppSec starts affecting real risk. AppSec has a defined boundary: the application itself. That includes the code, the libraries it depends on, the API endpoints it exposes, and the way it handles data at runtime.
The governing question is clear: is this application secure? Teams answer that through testing, review, and hardening at the software layer.
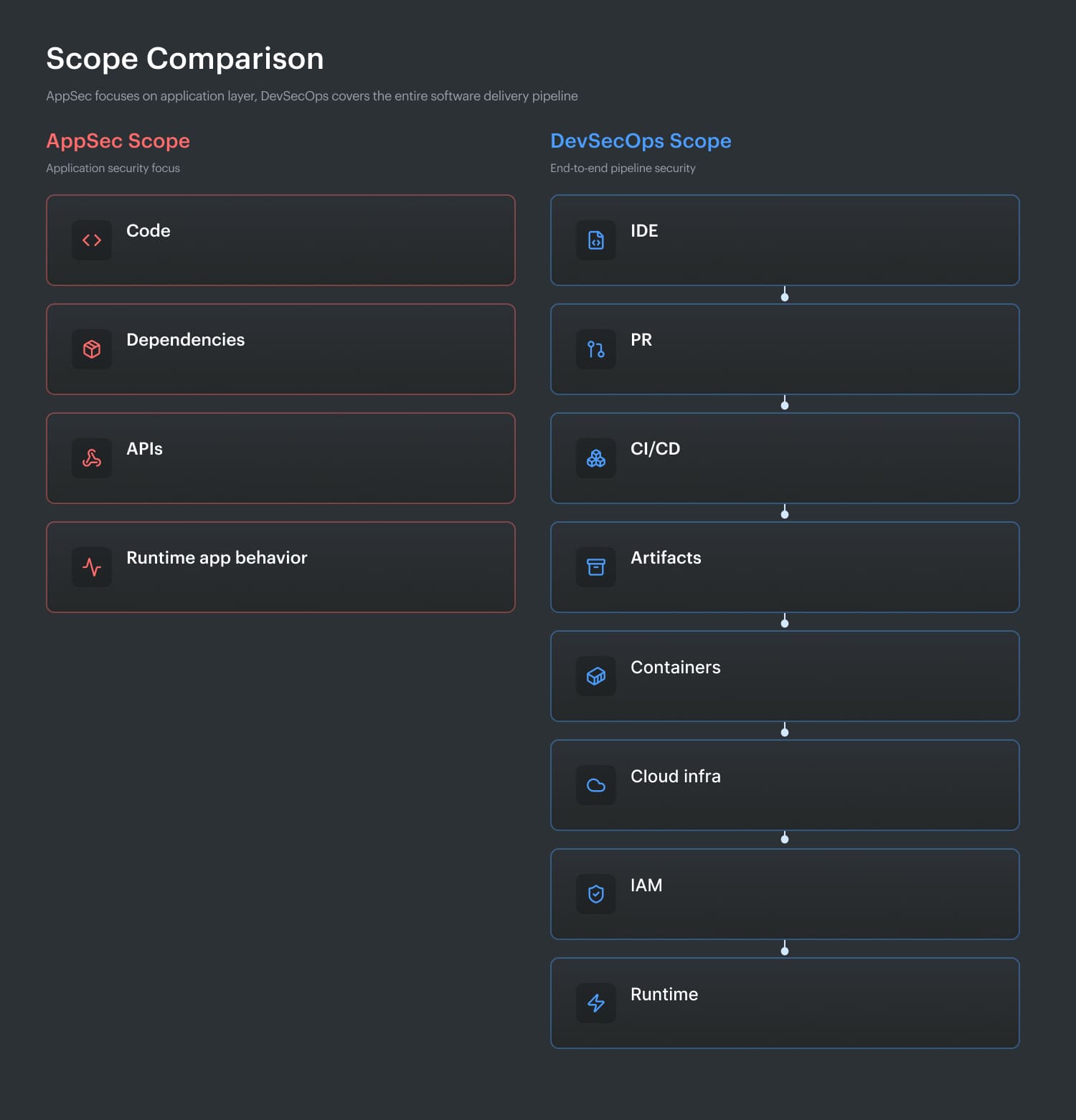
That visual matters because DevSecOps follows the workload far beyond the app boundary. It starts where code is written, continues through the build and deployment path, and keeps going into containers, cloud infrastructure, identities, policies, and runtime conditions. So a release can pass every AppSec check and still be dangerously exposed in production.
Think about a service with clean SAST results, no critical dependency findings, and strong API validation.
Looks solid.
Then you realize the S3 bucket it writes to is public, the IAM role has wildcard permissions, or the Kubernetes namespace has no network policy enforced. Nothing in that chain changes the fact that the application was well tested. It changes the fact that the system around it is still vulnerable.
| If AppSec says “pass” | DevSecOps still checks |
|---|---|
| Code has no critical findings | Was the artifact built in a trusted pipeline? |
| Dependencies are patched | Is the container image hardened? |
| API logic looks safe | Are IAM permissions too broad? |
| Runtime app behavior looks clean | Did cloud config drift after deployment? |
This is exactly where cloud-native teams get burned. They can have mature AppSec coverage, keep mean time to remediate low, and still miss the cloud misconfiguration sitting one layer below the app.
That is why scope matters so much. AppSec tells you whether the software is hardened. DevSecOps asks whether the entire delivery system is secure enough to ship without quietly accumulating risk.
Read also: DevSecOps Culture - Operating System Keeping Security Fast
Difference #2. Ownership: specialists vs shared responsibility
This is the part of DevSecOps vs AppSec that most teams underestimate. Tools can be bought in a quarter. Ownership models can take a year to fix. And when they stay fuzzy, security work slows down, findings bounce between teams, and nobody is fully accountable for the risk sitting in production.
In a traditional AppSec model, ownership is concentrated in a specialist function. AppSec engineers, security architects, or a security team define requirements, run testing, review findings, and hand remediation to developers. That structure is familiar, and in many organizations it is still necessary for depth, governance, and remediation SLA control.
The downside shows up fast. Work becomes sequential. Security reviews happen in a separate lane. Developers wait for findings, then context-switch back to fix them later. That is how security silos form, even in teams that believe they are moving fast.
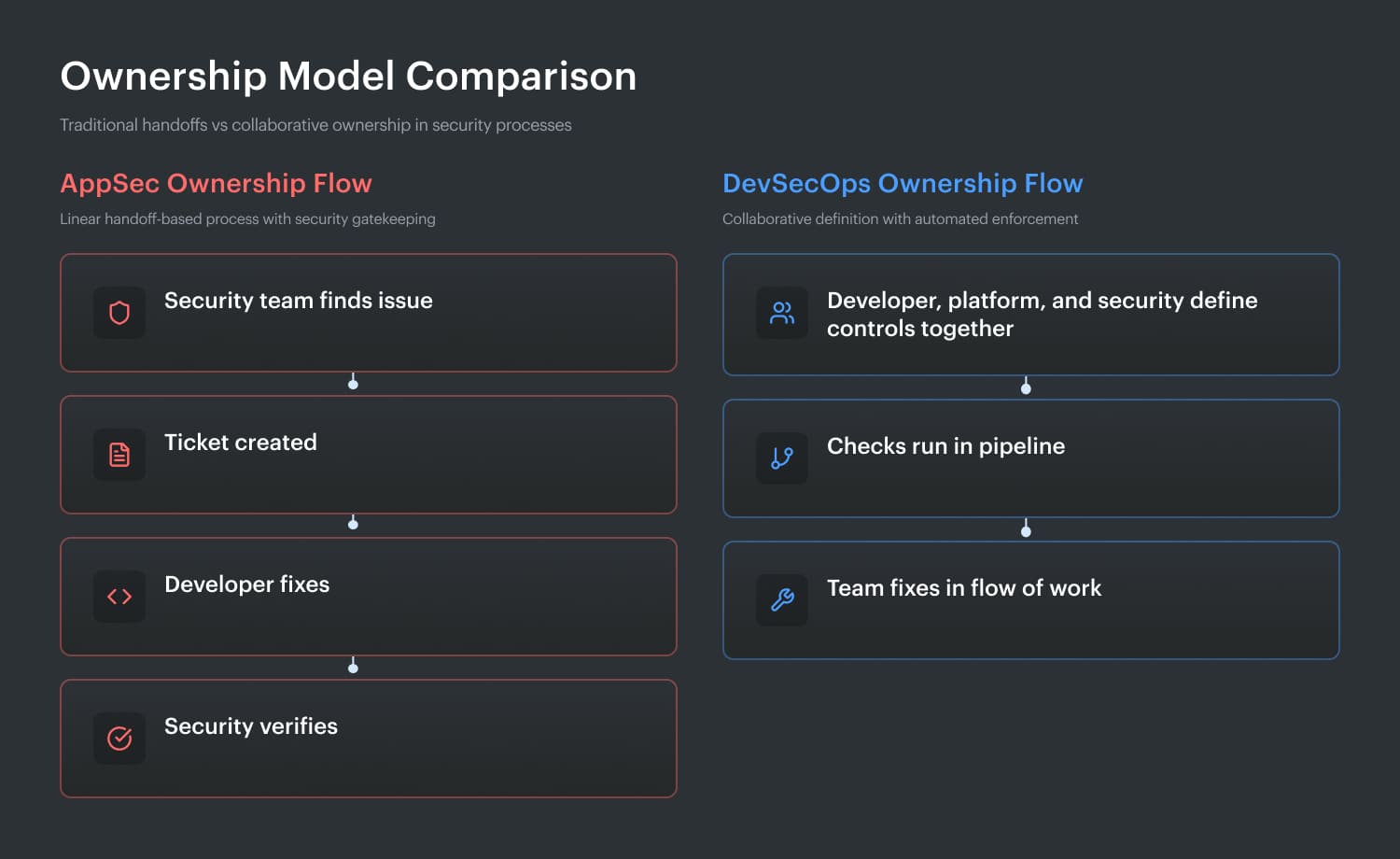
DevSecOps changes that model on purpose. Security becomes a shared engineering responsibility across development, operations, platform, and security.
- Developers are expected to write safer code because they have guardrails, usable feedback, and policy checks close to where they work.
- Platform and DevOps teams own the security of build systems, runtime configurations, identities, and infrastructure workflows.
- Security engineers stop acting like final approvers on every change and start acting like force multipliers. They build rules, tune tooling, codify policy, reduce noise, and help teams fix classes of problems earlier.
| Team | In an AppSec model | In a DevSecOps model |
|---|---|---|
| Security / AppSec | Defines rules, runs tests, triages findings | Defines guardrails, tunes tooling, enables teams |
| Developers | Fix tickets after review | Prevent and fix issues during development flow |
| Platform / Ops | Often outside AppSec scope | Owns secure pipelines, infra controls, runtime posture |
| QA | Sometimes involved in validation | Less central to ownership, more part of automated flow |
That shift matters because a DevSecOps platform alone does not create shared responsibility. If every finding still routes to the security team for triage, approval, and escalation, the operating model has not really changed. You just built a faster handoff system.
The mechanics improved. The ownership did not. And that usually means security debt keeps growing underneath the dashboard, even when the pipeline looks cleaner.
Cloud environments make this difference even sharper. Application code may be reviewed by AppSec, but the infrastructure it runs on is usually owned by platform engineering or DevOps. If ownership does not extend to that layer, risks pile up in the background: overprivileged IAM, exposed storage, weak secrets handling, policy drift.
By the time those gaps turn into incidents, the root cause is rarely “nobody had a tool.” More often, nobody clearly owned the security of the system outside the code.
In practice it means when AppSec owns findings and DevSecOps spreads ownership, the real question is who is equipped to prevent the problem before it reaches production.
Read also: A Practical 2026 Guide to DevSecOps on AWS
Difference #3. Timing and cadence: periodic gates vs continuous enforcement
This is the difference both Cloudaware DevSecOps experts, Valentin Kel and Igor K., kept coming back to: when security runs changes how expensive security becomes. A vulnerability found on the same day it was introduced is a quick fix. The same issue found six weeks later is a backlog item, a context switch, and often a much slower remediation cycle.
AppSec has traditionally worked in phases. A security review before release. A pen test every quarter. A code audit when a large customer asks for proof.
That model made sense when teams shipped monthly. It starts to crack when releases happen daily or several times a day. By the time a periodic check catches the issue, the code has already been extended, merged into other services, and pushed further down the line.
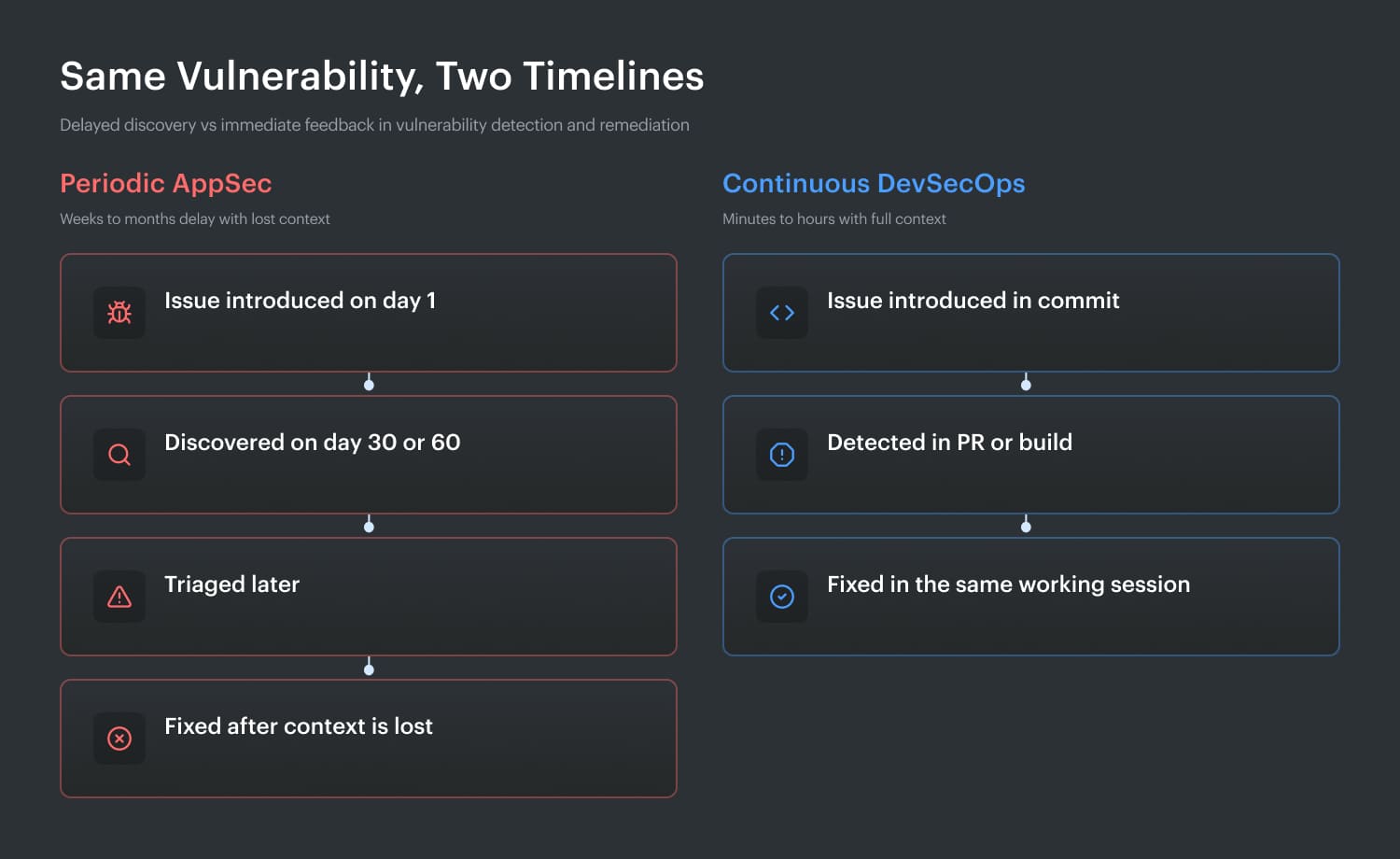
DevSecOps changes the cadence. Security runs inside the pipeline on every commit, build, and deployment. A pull request can trigger SAST, SCA, secrets detection, and IaC scanning at once. Developers receive feedback while they still remember what they changed. Critical findings stop the build. Lower-risk issues are routed with context, not dumped into a spreadsheet.
| Timing model | What usually happens |
|---|---|
| Periodic gates | Findings age, queues grow, fixes cost more |
| Continuous enforcement | Findings stay current, fixes are faster, and the backlog grows more slowly |
That is the real cadence gap. AppSec often checks whether software is ready to move. DevSecOps keeps checking while the software is moving.
Some older uploaded files have expired on my side, so if you want me to match a second style sample line by line, re-upload it and I’ll tune the voice even tighter.
Difference #4. Tooling philosophy: point solutions vs an integrated security system
The tools may look familiar. The difference is in how much context travels with the finding, how little human chasing it needs, and whether the alert can explain real risk instead of just reporting a defect.
AppSec tooling is built to answer narrow, important questions about a specific artifact.
- Does this code contain a known weakness?
- Can this running app be broken with attack inputs?
- Is this dependency tied to a known CVE?
Those are good questions. They are just bounded ones. An SAST result, a DAST result, or a pen test report usually lands as a findings list that a human still has to interpret, route, and prioritize.
That connective layer is the real divide.
| Same issue | AppSec tells you | DevSecOps tells you |
|---|---|---|
| Vulnerable library | CVE exists in dependency runs in a public container, | CVE exists, is deployed in prod, and sits behind weak IAM |
| Exposed secret | Secret detected in code pipeline, environment | Secret detected, linked to repo, and likely blast radius |
| Risky config | Misconfiguration flagged | Misconfiguration traced to the IaC change that introduced it |
That gap gets wider in cloud environments. AppSec tools do not naturally see whether storage is encrypted, whether network exposure drifted, or whether runtime permissions changed after deployment. You need a cloud layer for that, usually CSPM or CNAPP, sitting between the app view and the delivery view.
Otherwise, you end up with solid point solutions and a very fragmented risk picture.
Difference #5. Success metrics: what "good" looks like
Valentin Kel and Igor K. both made the same point when we discussed this section: teams often improve the system, then judge it with the wrong scoreboard. That is how good DevSecOps work ends up looking like bad news in quarterly reporting.
AppSec and DevSecOps do not chase the same proof of success. AppSec usually measures the health of risk reduction: critical findings, fix rate, coverage, SLA performance, mean time to remediate. Those numbers tell you how well the team is finding and closing known weaknesses in the application portfolio.
DevSecOps looks at flow. Are security checks keeping up with delivery? How many builds pass gates without manual review? How much time does security add to the path to production? How quickly are issues detected and routed? How many problems still escape into runtime?
A simple visual works well here:
If your KPI is backlog health, you’re mostly measuring AppSec.
If your KPI is secure delivery speed, you’re measuring DevSecOps.
That distinction matters because the first months of a DevSecOps rollout often look worse on paper. Vulnerability counts go up. Why? Because the pipeline is finally finding things continuously instead of periodically.
So the real question is about whether security is now finding risk earlier, fixing it faster, and slowing delivery less.
Read also: DevSecOps Velocity - Ship Faster Without Growing Security Debt
Difference #6. How cloud changes the equation for both
This is the part most competitor articles skip, and honestly, it is where the whole debate gets more real. When I pressure-tested this section against feedback from Cloudaware DevSecOps experts Valentin Kel and Igor K, the same pattern kept coming up: cloud changes the boundary so much that DevSecOps vs AppSec becomes less about categories and more about visibility.
In older on-prem setups, the line was cleaner. AppSec focused on the application. Operations teams handled the infrastructure underneath it. Those were connected concerns, but still separate enough to manage in different lanes.
Cloud broke that separation.
Now the same developer can change application code, update a Terraform module, modify a Kubernetes manifest, and trigger deployment through the same pipeline in the same pull request. That changes the risk model fast. A bad query can expose data. So can an overprivileged IAM role. A vulnerable dependency matters.
So does a public bucket, weak network segmentation, or encryption turned off in the environment that app depends on.
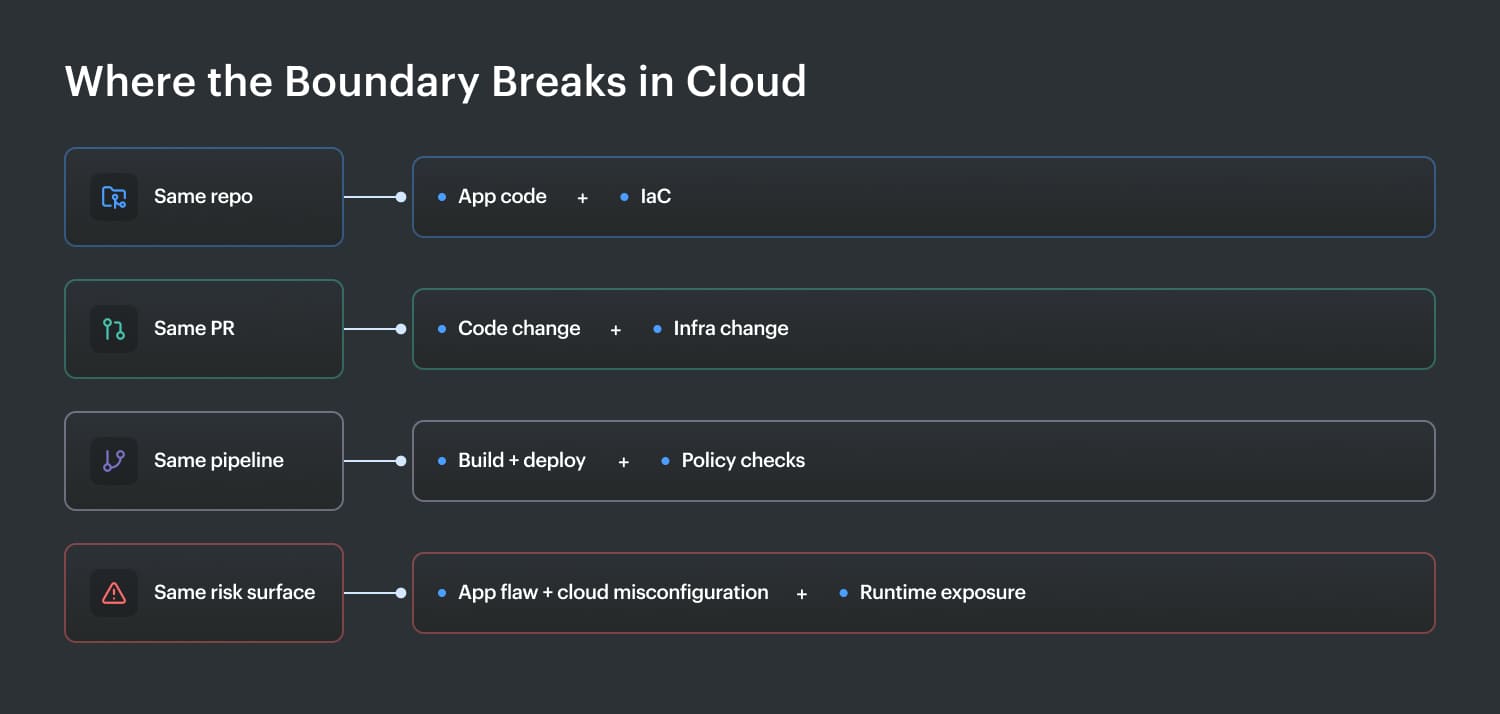
That is why cloud-native teams struggle to keep AppSec and DevSecOps neatly separated.
| In a traditional model | In a cloud model |
|---|---|
| App risk and infra risk can be reviewed separately | App risk and infra risk are often created together |
| Different teams own different layers | The same workflow touches both layers |
| Findings live in separate tools and reports | Risk needs shared context across code, pipeline, and cloud |
This convergence is exactly why CNAPP exists. It tries to connect AppSec findings, pipeline controls, CSPM signals, and runtime posture into one view. Most teams are not there yet. They still run AppSec on code, DevSecOps in pipelines, and cloud security in a separate dashboard. That leaves them with coverage, but not a unified risk picture.
That is the real shift. In the cloud, AppSec and DevSecOps still matter as disciplines, but the environment forces them into the same story.
Read also: DevSecOps vs SRE: What's Different and How to Run Both
Where AppSec and DevSecOps overlap
After looking at the differences in scope, ownership, timing, tooling, metrics, and cloud context, the picture gets clearer. AppSec and DevSecOps are not the same thing, but they absolutely share ground. That shared ground is exactly where teams get confused. They automate a few controls, wire scanners into builds, and assume the whole operating model changed.
It usually didn’t.
DevSecOps includes AppSec and extends it. It builds on the same security logic, then carries it across delivery, enforcement, and day-to-day engineering work.
You can see that overlap first in SAST and DAST. Those are classic AppSec controls. They exist to find weaknesses in code and application behavior. Once they run inside the automated testing pipeline, though, they also become part of a DevSecOps workflow.
Same tools. New context.
Findings appear during pull requests and builds, while the developer still remembers what changed and can fix it without losing a day to back-and-forth.
The same pattern shows up in software composition analysis.
- At the AppSec level, it helps teams manage open-source risk in dependencies.
- In DevSecOps, that check runs in every build, feeds policy decisions, and helps block risky packages before they move downstream.
Developer education works the same way. AppSec defines the need for secure development habits. DevSecOps reinforces them through developer-first security, practical guardrails, and security champions inside engineering teams.
Then there is vulnerability triage. Both disciplines need it because not every alert deserves the same response. Mature teams prioritize by exploitability, exposure, and business impact. That is why speed alone does not equal DevSecOps. Automating AppSec checks is one ingredient. The bigger recipe includes shared ownership, policy enforcement, and feedback loops that actually change how software gets shipped.
Which approach does your organization actually need?
After all the difference-and-overlap talk, this is the part most teams actually care about: what do we do next? The answer depends less on labels and more on where your workflows break today. That is the better signal of security program maturity. Look at how security shows up before release, inside delivery, and in the cloud environments your applications depend on.
Scenario 1: “We ship software, but security is still mostly manual before release.”
You already have AppSec habits. The problem is cadence.
Maybe the team runs reviews before major releases. Maybe pen tests happen on a schedule. Maybe findings arrive as tickets after the code has already moved on. That setup can work for slower delivery.
It starts hurting once engineering ships weekly, daily, or several times a day. Security becomes a queue. Developers lose context. Vulnerabilities slip through between review windows, and fix rates rarely keep pace with release velocity.
The smartest next move is not a giant platform rollout.
- Start smaller and make it stick.
- Take the AppSec controls you already trust, usually SAST and SCA first,
- and move them into the pipeline as automated security testing.
That gives you earlier feedback without forcing the team to relearn everything at once.
In practical terms, this is the first real step from AppSec DevSecOps thinking into a delivery model that scales.
Scenario 2: “We have security gates in CI/CD, but they mostly scan code.”
This is where a lot of teams think they are done, and they are not.
You probably have decent DevOps security integration already. Scanners run in pull requests or builds. Policies may even block critical findings. That is progress. Still, if those controls stop at source code and dependencies, your blind spot is probably the environment around the app.
What tends to be missing here:
- IaC security checks
- container misconfiguration visibility
- secrets exposure outside code
- cloud policy drift after deployment
- runtime context for prioritizing findings
That gap matters because a clean build does not guarantee a safe release. A service with no critical code issues can still be deployed with weak IAM, public storage, or broken network boundaries. So your next step is to expand from code security into cloud security posture. Add infrastructure and deployment context to the checks you already run well.
Read also: DevSecOps Compliance: CI/CD Controls, Evidence, and SOC 2
Scenario 3: “We’re cloud-native, fast-moving, and spread across teams or clouds.”
At this stage, partial coverage usually creates more confusion than comfort.
When multiple teams ship quickly across several environments, the model has to connect application findings, pipeline enforcement, and infrastructure visibility in one story. You need AppSec controls embedded in DevSecOps workflows, plus a cloud layer such as CSPM or CNAPP that keeps watch over what is actually running.
This is where cloud-native security stops being a nice idea and becomes operationally necessary. A code vulnerability means something very different when you can see that it sits on an internet-facing workload with broad permissions.
That is why mature teams with real multi-cloud security needs do not choose AppSec or DevSecOps in isolation. They combine both, then add cloud context so prioritization reflects actual exposure, not just scanner output.
Read also: 9 DevSecOps Benefits for Security Leaders [With Proof]
Why choosing one over the other is the wrong question
After walking through the differences and the overlap, the bigger point comes into focus. Mature teams do not sit in meetings arguing AppSec or DevSecOps like they are two competing products. They treat AppSec as the depth layer inside the security program, and DevSecOps as the delivery model that decides whether that depth actually shows up when code is built, reviewed, approved, and shipped.
So the useful question is tougher: are your AppSec fundamentals strong enough to survive automation without flooding engineers with junk findings, weak policies, and expensive rework?
One failure mode is simple to spot. The team has decent reviews, decent testing, decent remediation habits, and terrible speed. Security shows up late, queues build, context disappears, and every release starts dragging slightly more than the last one.
That is a security bottleneck, and it usually signals low security maturity, not strong control.
The second failure mode looks healthier in dashboards. Scans run in the pipeline. Checks fire automatically. Builds move fast. Then vulnerable code still lands in production because the underlying AppSec depth is shallow. From a CISO strategy perspective, that is weak security ROI. You bought acceleration without enough judgment behind it.
Cloud adds the third trap. Teams can get both motions mostly right at the application layer and still miss the risk living in infrastructure, IAM, and runtime drift. That is why the conversation keeps moving toward CNAPP and broader cloud-native application protection. Once code, pipeline, and cloud are part of the same release story, “which one do we choose?” stops being the serious question.
3 Common mistakes teams make when combining AppSec and DevSecOps
Once teams understand the difference between AppSec and DevSecOps, the next trap is implementation. This is where good intentions turn into security theater. Controls exist. Dashboards look busy. People say the right words in status meetings. Meanwhile, risky changes still reach production, developers still complain about noise, and nobody feels fully confident that the system is actually improving.
Running AppSec scans manually and calling it DevSecOps
This usually looks harmless at first. A team runs SAST or dependency checks near the end of a sprint, reviews the report before release, opens a few tickets, and says security is now part of delivery. It is not enough.
What is really happening is that AppSec is still operating as a late checkpoint. The scan may be useful, but the timing turns every finding into a slower, more expensive fix. By then, the code has already been merged, extended, tested by others, and mentally abandoned by the developer who wrote it. Context is gone. Remediation drags. Findings age. That is how security debt grows quietly even when scan coverage looks decent on paper.
The practical clue is simple: if security feedback arrives after the work is basically done, you are still in a manual AppSec model. DevSecOps changes the cadence. Checks have to run in the flow of work, inside pull requests, builds, and deployment decisions, while teams still have the power to fix issues cheaply.
Buying a DevSecOps platform but only turning on the SAST scanner
This one is incredibly common because it feels like progress is fast. A company invests in a DevSecOps platform, plugs in source code scanning, maybe adds severity thresholds, and assumes the platform rollout is now complete. In reality, the team has bought a broad system and is using it like a point tool.
The risk here is false confidence. Security leaders assume that the new platform logo in the architecture diagram covers end-to-end delivery. Developers assume that the build checks catch all the important risks. But if the only active control is SAST, then infrastructure drift, secrets exposure, container misconfiguration, policy failures, and runtime context are still outside the picture. That is AppSec with nicer packaging.
This is also where tool sprawl sneaks in. One team owns the DevSecOps platform. Another still runs separate container scans. A third monitors cloud posture in another console. No one has a unified view of how those findings connect, so the same issue gets triaged three times or ignored three different ways.
Measuring DevSecOps success with AppSec metrics
A lot of teams get the implementation mostly right and still tell the wrong story upstairs.
If leadership keeps judging DevSecOps through backlog counts alone, the rollout can look worse before it looks better. Open vulnerabilities may go up in the first quarter because the pipeline is finally surfacing issues continuously instead of once a month. That is visibility arriving on schedule.
The mistake is using AppSec-style outcome metrics as the only scoreboard for a delivery model. Vulnerability count, CVSS totals, and remediation backlog absolutely matter. They just do not tell you whether security is keeping pace with engineering. For that, you need process metrics: gate pass rate, time added to builds, finding age before assignment, escape rate to production, and how fast teams resolve blocking issues in the pipeline.
Miss this, and you create the wrong incentives. Teams start tuning scans to make dashboards look calmer instead of improving signal quality. Findings get suppressed. Thresholds get loosened. Everybody protects the metric. Nobody protects the system.
Teams usually do not fail because they lack scanners, policies, or dashboards. They fail because the signal stays fragmented. AppSec finds the issue in code. DevSecOps tracks the control in the pipeline. Meanwhile, the cloud environment where that application actually runs often sits in a separate system, with separate context, separate owners, and separate risk signals. That is the gap mature teams have to close next.
Once you can connect application findings, delivery controls, and live cloud posture in one view, AppSec and DevSecOps stop competing for definition and start working as one operational model. That is exactly where Cloudaware comes in.
How Cloudaware connects AppSec and DevSecOps at cloud scale
Most teams do not have a tooling problem. They have a context problem.
An AppSec scanner can tell you the code is vulnerable. A DevSecOps pipeline can tell you when that finding appeared, whether the build passed, and who needs to fix it. Useful, yes. Still, one question shows up right after that: where is this code running right now, what cloud assets does it touch, and how bad does this get if someone exploits it?
That is the part many teams still cannot answer fast. They can see the flaw. They can see the workflow. They cannot see the full blast radius.
That is where Cloudaware changes the picture. It gives teams continuous cloud asset inventory and live configuration visibility across cloud environments, which means the infrastructure layer stops sitting outside the security story.
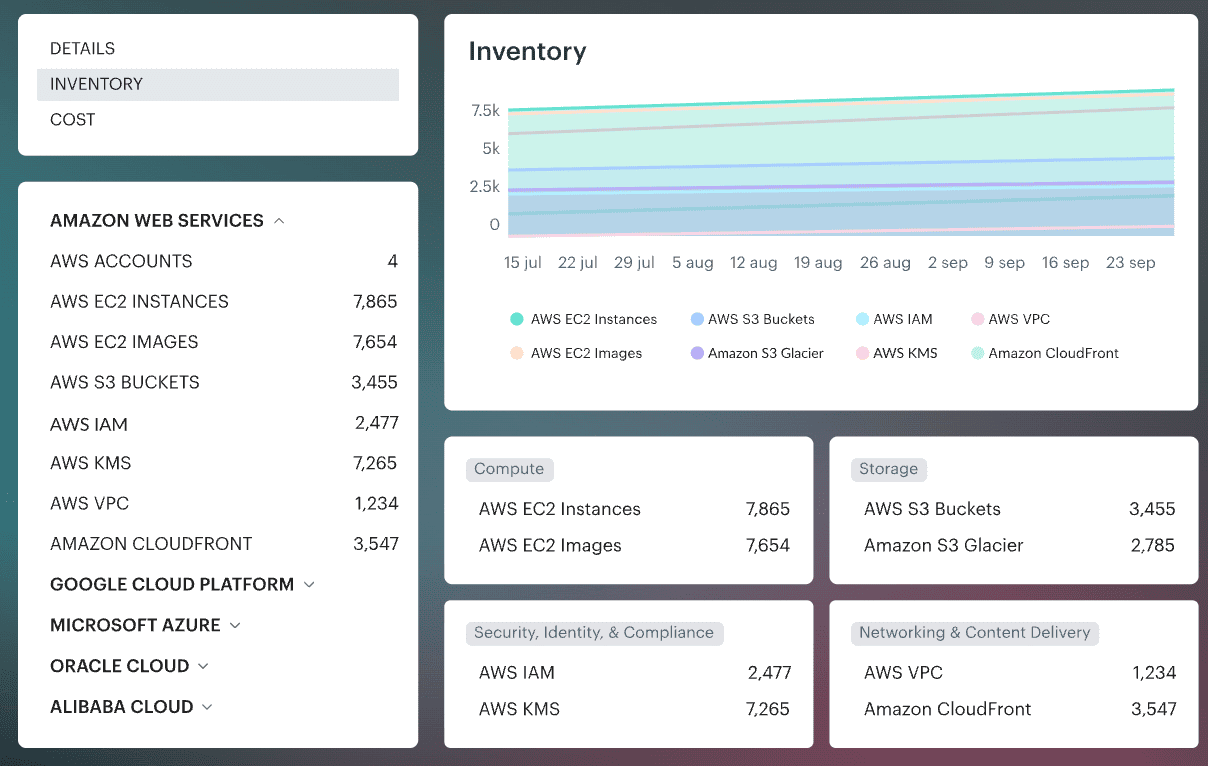
When an application issue is found, Cloudaware helps connect that finding to the compute, storage, network paths, and IAM security around it. Suddenly the conversation gets sharper. You are no longer looking at “this code is vulnerable.” You are looking at “this code is vulnerable, it is running on an internet-facing workload, and the role attached to it has more access than it should.”
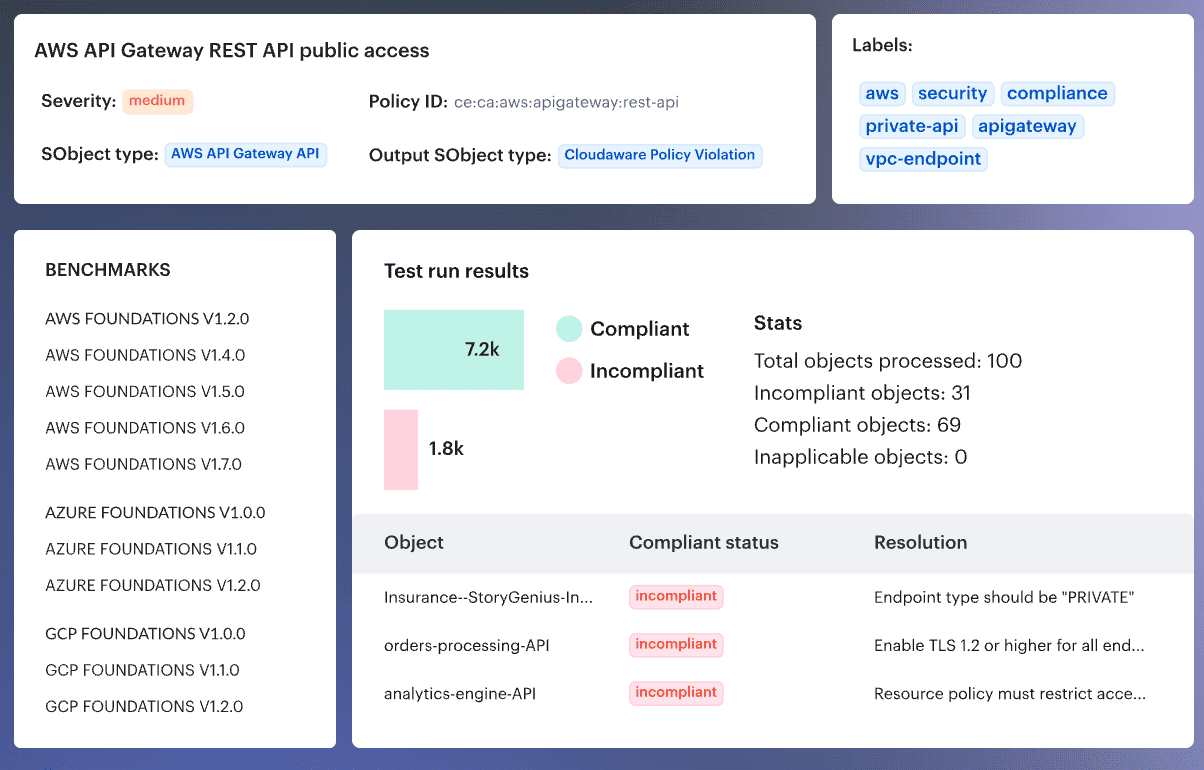
That matters for both sides of the house. AppSec teams get the cloud context that helps them prioritize findings based on exposure, not just severity. DevSecOps teams get continuous checks on what is actually running, including drift between what the pipeline deployed and what the environment looks like now.
That closes the gap CI/CD tools and scanners usually miss. It also helps surface the issues that sit between AppSec and pipeline controls, especially misconfiguration detection problems a SAST scanner will never see and a gate in the build may never revisit.
Cloudaware connects application findings, delivery controls, and cloud infrastructure security in one working view. That is the missing layer between AppSec, CSPM, and broader CNAPP thinking. It gives teams the cloud visibility to move faster and make better decisions with less guessing.
