An IT asset management policy defines how your organization acquires, tracks, governs, secures, and retires technology assets across their full lifecycle. In a hybrid environment, it includes cloud resources, SaaS applications, virtual machines, containers, databases, identities, and the configuration items tied to the services your business actually runs.
Without a clear policy, asset tracking breaks down fast. Ownership becomes unclear, lifecycle states drift from reality, cost allocation gets noisy, and the CMDB starts filling with records nobody fully trusts.
A good asset management policy prevents that. It gives teams one operating model for scope, classification, ownership, lifecycle control, inventory accuracy, compliance, and review. It also makes the policy enforceable in real environments, where cloud resources are created through IaC, changed through pipelines, and discovered across multiple providers.
TL;DR
- An IT asset management policy defines how technology assets are managed from acquisition through retirement.
- A complete policy should cover hardware, software, SaaS, cloud resources, and supporting configuration items.
- The strongest policies connect lifecycle rules, ownership, asset tracking, and compliance requirements in one place.
- In hybrid environments, the policy only works if discovery, CMDB updates, and governance are tied to actual operational workflows.
What is an IT asset management policy?
An IT asset management policy is a formal document that defines how an organization manages technology assets across acquisition, deployment, use, maintenance, reassignment, and retirement. It establishes the rules, responsibilities, and controls required to keep asset data accurate, costs visible, services supportable, and compliance evidence available when needed.
In practice, the policy should answer a simple set of questions.
- What counts as an asset?
- Who owns it?
- How is it classified?
- How is it discovered and tracked?
- What lifecycle state is it in?
- What controls apply to it?
- What happens when it is no longer needed?
If the document cannot answer those questions clearly, it is not doing enough.
IT assets vs. general assets: key differences
While a general asset management policy focuses on ownership, depreciation, and physical inventory, an IT asset management policy has to govern assets that are dynamic, interconnected, and often short-lived.
The table below shows why IT assets need a different policy model:
| Area | General assets | IT assets |
|---|---|---|
| Primary focus | Ownership, depreciation, and physical inventory | Lifecycle control, technical context, and governance |
| Asset behavior | Usually static and long-lived | Dynamic, interconnected, and frequently changing |
| Examples | Furniture, vehicles, facilities equipment | Cloud resources, SaaS applications, virtual machines, containers, databases |
| Tracking method | Manual registers or fixed asset systems | CMDB, ITAM platform, automated discovery, and reconciliation workflows |
| Compliance impact | Mostly financial and procurement-related | Financial, operational, security, privacy, and audit-related |
That is why an ITAM policy needs lifecycle rules, technical classification, system-of-record definitions, discovery requirements, software and SaaS coverage, and links to security and compliance controls.
Why your organization needs an IT asset management policy
The value of a policy is in the operating discipline that the document creates.
When teams use different naming patterns, inconsistent tags, or separate tracking methods across on-prem and cloud environments, the organization loses the ability to answer basic questions quickly.
A strong policy closes those gaps by standardizing how assets are recorded and governed, regardless of where they run.
Regulatory and compliance benefits
From an audit perspective, the policy gives your organization a repeatable way to show control over technology assets. It supports evidence collection for standards and frameworks such as ISO 27001, ISO 19770-1, SOX, GDPR, and internal governance requirements. It also helps teams prove that assets are classified, reviewed, secured, and retired according to a documented process.
Without that structure, audits turn into manual reconstruction. Teams spend time chasing owners, validating spreadsheets, and trying to explain why live assets never made it into the asset register or why retired systems still appear active.
Financial and cost control benefits
The policy also matters financially. Asset records drive procurement, refresh planning, software license control, and cloud cost accountability. When lifecycle states are inaccurate or ownership fields are missing, spend analysis becomes unreliable, and optimization efforts lose context.
A mature asset management policy helps teams tie assets to business services, cost centers, and lifecycle stages so waste is easier to find, and budget planning becomes more grounded in operational reality.
Key components of an IT asset management policy
This section is the core of the page because it defines what a complete asset management policy should actually contain.
1. Policy scope and objectives
The policy scope defines which asset types, teams, environments, and business units are covered. It should explicitly include:
- Hardware
- Software
- SaaS
- Cloud resources
- Any related CIs that support business services
Without a clear scope, different teams will apply different assumptions, which leads to blind spots and uneven governance. The objectives should also be explicit, such as full asset discoverability, ownership assignment, lifecycle traceability, and audit-ready records.
2. Asset classification and categories
Asset classification defines how assets are grouped and labeled so they can be governed consistently. This usually includes categories such as:
- Hardware asset management
- Software asset management policy coverage
- Cloud resources
- Mobile assets
- SaaS tools
- Edge or on-prem infrastructure
The point is not taxonomy for its own sake. Good classification supports access control, cost allocation, lifecycle rules, service mapping, and reporting. Your policy should also define mandatory metadata such as environment, owner, business service, cost center, and data classification where relevant.
3. Roles and responsibilities
Every asset needs an accountable owner, and the policy needs named roles for governance, execution, review, and escalation. Ownership typically sits with IT leadership or an ITAM function, while day-to-day responsibilities may be distributed across platform, cloud, security, procurement, and department leads.
If this section is vague, incident response slows down, exceptions pile up, and policy enforcement becomes optional. A practical policy should define who owns the policy, who manages asset records, who approves exceptions, and who is responsible for compliance within each team.
4. Asset acquisition and procurement process
The policy should define how new assets enter the environment, including approval thresholds, procurement workflows, required metadata, and the conditions for adding an asset to the inventory or CMDB. This applies to:
- Hardware purchases
- Software subscriptions
- SaaS tools
- Cloud resources provisioned through approved workflows
A clean acquisition process prevents shadow purchases and incomplete records at the start of the lifecycle. It is much easier to maintain a trustworthy IT asset inventory when the asset is classified and assigned correctly before it goes live.
5. Asset tracking and inventory management
Asset tracking defines how the organization keeps an up-to-date record of every managed asset. That includes:
- The system of record
- Discovery sources
- Reconciliation rules
- Required fields
- The frequency of data reviews
Without a defined tracking process, the inventory drifts into partial truth. Assets appear in finance tools but not in the CMDB, or they remain in the CMDB long after they were terminated.
Your policy should specify whether a CMDB, dedicated ITAM platform, or another asset register is authoritative, and how discovery data is reconciled against it.
6. Software license management
A complete policy should address software asset management policy requirements, including how licenses are approved, tracked, renewed, reassigned, and audited. This section should also cover prohibited software, overdeployment risk, and the handling of unused entitlements.
Many organizations focus too heavily on hardware and leave software governance fragmented. That creates compliance risk and unnecessary spend. The policy should define how license ownership is tracked, how exceptions are handled, and which tool or process is used for reconciliation.
7. Asset maintenance and support
Assets do not become governance-free once they are deployed. The policy should define maintenance standards, patching expectations, support ownership, warranty or contract tracking, and service review requirements throughout the active lifecycle.
This matters because unsupported or neglected assets tend to create both operational and security issues. A useful policy links maintenance to asset criticality and lifecycle state rather than treating everything the same.
8. Asset disposal policy and retirement policy
This section defines how assets reach end of life and how retirement is documented. It should cover approval for disposal, data wiping standards, vendor requirements, revocation of access, record closure, and retention of evidence.
The policy should also clarify how the end-of-life policy applies to hardware, software, SaaS, and cloud resources that are no longer needed.
This is one of the most overlooked parts of any policy, especially for cloud and SaaS assets that seem easy to delete. In reality, disposal must be traceable. The policy should state how assets are archived, removed from active inventory, and validated as retired so the CMDB does not retain false active records.
9. Security and access control rules
An ITAM policy should align with security by defining what security metadata must exist on each asset, what access controls apply, and how sensitive or regulated assets are identified. This may include control owner fields, data classification, compliance scope, baseline configurations, and exceptions management.
When security data is disconnected from asset data, teams lose the ability to assess exposure quickly. A strong policy keeps asset tracking, ownership, and control context in the same operating model.
10. Policy review and update cycle
A policy that is never reviewed becomes a source of drift instead of a control. This section should define how often the policy is reviewed, who approves updates, what events trigger interim reviews, and how changes are communicated.
Best practice is at least an annual review, plus updates after major architecture changes, acquisitions, control failures, or regulatory changes. The review cycle should also rely on metrics, not opinion alone.
How to write an IT asset management policy
A strong IT asset management policy is not created by filling out a template in isolation. It works when the document reflects how assets are actually provisioned, discovered, classified, reviewed, and retired across your environment.
To make this section more practical, we asked Daria, an ITAM engineer at Cloudaware, how she approaches policy design with real teams. Her advice is consistent: start with the operational pain, write for the environment you actually run, and make the policy enforceable through tooling rather than manual reminders.
Step 1: Gather requirements
Daria starts with the people who deal with asset data every day, not with a blank document. That means short working sessions with DevOps, cloud architects, SecOps, GRC, and other stakeholders who depend on accurate asset records to do their jobs.
The goal is to find where the current model breaks down. In some environments, tagging requirements block infrastructure delivery because teams do not control the right metadata. In others, discovery tools find the asset but not the business context, which makes cost reporting, ownership mapping, and compliance reviews much harder than they should be.
A useful way to begin is with a short intake form or interview guide. Ask where asset tracking is failing now, what the CMDB or asset register should answer automatically, and which controls are routinely bypassed or worked around. Those answers will tell you what the policy needs to solve first.
Step 2: Define scope and objectives
Once the operational issues are clear, define the scope of the policy in explicit terms. List the asset types it covers, such as hardware, software, SaaS applications, cloud resources, Kubernetes infrastructure, serverless services, virtual machines, and supporting configuration items. Just as important, state what is excluded.
Daria recommends writing the objectives in a direct, operational way. The document should not just say “improve governance.” It should define outcomes teams can measure, such as ensuring deployed assets are discoverable within a set time window, linking each asset to a service owner and cost center, and enforcing classification standards in provisioning workflows.
That level of clarity helps later when teams need to decide whether the policy is working or whether the scope needs to change.
Step 3: Draft the policy sections around real processes
According to Daria, the best draft structure follows the way work actually happens. That usually means sections for acquisition, discovery, classification, ownership, lifecycle management, asset tracking, software licensing, compliance alignment, maintenance, and retirement.
Each section should answer four questions clearly:
- What is the standard?
- Who enforces it?
- Which tools or systems support it?
- What happens when the standard is not met?
For example, the ownership section may define that every deployed compute resource must include owner, team, and business_unit metadata, with values validated against approved identity or team sources. If those fields are missing, the resource should not move forward without exception handling. That is much stronger than simply saying ownership “should be documented.”
Step 4: Review and iterate
Most policies go stale because they are published once and then left alone while the environment keeps changing. Daria’s recommendation is to build policy review into the team’s normal operating rhythm.
That can be a short quarterly review session with platform, security, ITAM, and compliance stakeholders. The point is to look at real friction. Which fields are missing most often? Which lifecycle states are inaccurate? Which controls are creating noise instead of useful governance? If the policy no longer reflects how infrastructure is built and managed, the answer is to revise the policy, not blame the teams.
A lightweight dashboard helps here. Useful measures include the percentage of assets discovered without classification, assets missing a control owner, and the average time from deployment to CMDB visibility. Those signals tell you whether the operating model behind the policy is holding up.
Step 5: Review and approve
Once the draft is stable, route it through the people responsible for asset governance and control. In many organizations, this includes:
- IT Director or CIO
- Cloud or platform lead
- Security leadership
- Compliance or audit stakeholders
Some teams may also run it through formal governance bodies such as a CAB, depending on internal policy and practice.
Daria’s advice is simple: make the approval trail explicit. Record who approved the policy, when it became effective, what version is current, and what triggers an interim review. That matters later because policy enforcement goes more smoothly when there is no ambiguity about who signed off on the standard.
Step 6: Implement and automate
Publication is not the finish line. The policy only matters if it changes how assets enter and move through the environment. That means enforcement should sit in the places where infrastructure decisions already happen:
- IaC modules
- CI/CD workflows
- Discovery processes
- CMDB reconciliation
- Ticketing or review paths
Daria recommends starting with a few concrete controls. Require standard metadata in Terraform or other provisioning modules. Validate those fields in delivery workflows through policy checks. Reconcile discovered assets against expected classification and ownership rules. Trigger review or ticket creation when key fields are missing or lifecycle states do not match reality.
That is how an IT asset management policy becomes a working control surface rather than a document people remember only during audits.
Step 7: Communicate and train
Even a well-written policy will fail if teams are expected to discover it on their own. Daria treats rollout as a change enablement exercise, not a publishing task. Engineers, asset owners, procurement teams, and compliance stakeholders all need to understand what changed, why it changed, and what they are expected to do differently.
That does not require heavy training. A short internal guide, a small number of demos, and practical examples often work better than long documentation. The most helpful materials usually show where the required metadata lives, how asset ownership is assigned, which views or dashboards people should use, and what happens when the policy is not followed.
Step 8: Track metrics and refine
Daria’s final point is that the policy needs measurable feedback. Without metrics, teams cannot tell whether the document improved control or simply added wording. The most useful KPIs are the ones that expose friction and data quality.
Examples include the percentage of assets with complete metadata, the time from deployment to registration in the CMDB or asset register, the number of policy violations resolved automatically, and the number of drift events found before they affected production or audit readiness.
When those numbers improve, the policy is doing its job. When they slip, the organization has a signal to refine controls, improve workflows, or tighten the connection between the document and the systems enforcing it.
IT asset management policy template
Below is a practical inline template you can adapt for your own environment.
| Policy section | What to include |
|---|---|
| Purpose and scope | State the goal of the policy and list which assets, departments, and locations it covers. |
| Policy owner | Name the accountable role, review owner, and escalation contacts. |
| Asset classification | Define categories for hardware, software, SaaS, cloud, mobile, and peripheral assets. |
| Acquisition process | Explain approval workflows, budget thresholds, and approved procurement paths. |
| Asset tagging and tracking | Define mandatory metadata, tagging method, and the system of record. |
| Deployment rules | Specify baseline requirements before assets go live. |
| Maintenance schedule | State patching, support, review, and warranty expectations. |
| Software licensing | Define license tracking, renewals, exceptions, and prohibited software rules. |
| Disposal and retirement | Include approved disposal methods, data wiping requirements, and record closure steps. |
| Review cycle | Define annual review date, approver, and version history requirements. |
IT asset management policy best practices
A solid IT asset management policy works only if it reflects how assets actually move through your environment. These best practices focus on keeping the policy enforceable, connected to real systems, and resilient as your hybrid setup changes.
Keep the policy living, not static
Review the policy annually at a minimum, and revisit it after major operational or organizational changes. The document should reflect how assets are really managed, not how governance looked two years ago.
Integrate with your CMDB from day one
If the policy is disconnected from the CMDB or asset register, record quality will depend on manual effort. A stronger approach is to define the system of record, discovery feeds, reconciliation rules, and ownership logic directly in the policy.
Align lifecycle stages with procurement and finance workflows
Procurement, deployment, active use, reassignment, and retirement should not sit in separate silos. When lifecycle stages line up with purchasing and budget processes, the organization gets better control over utilization, refresh planning, and spend visibility.
Include shadow IT discovery in scope
A modern asset management policy should not assume all assets arrive through official channels. It should define how the organization identifies unmanaged SaaS, unapproved software, and cloud resources that bypass the preferred workflow.
Define a clear chain of custody for high-value assets
High-value or regulated assets need stronger transfer and reassignment controls. The policy should state how ownership changes are approved and documented, especially when assets move between teams, environments, or business functions.
Automate license compliance alerts
Software governance works better when overuse, underuse, and renewal risk are surfaced automatically. The policy should encourage tooling and reporting that reduce manual reconciliation work.
Common mistakes to avoid
Even a well-structured policy can fall short if key areas are overlooked. The following mistakes are common across organizations and often lead to poor asset visibility, weak governance, and audit challenges.
- Writing a policy without assigning owners. A policy without ownership is a document with no operating model behind it. It may look complete on paper, but it will not hold up during audits, incidents, or lifecycle reviews.
- Not covering cloud and SaaS assets. Many policies still read like hardware-only documents. That leaves major gaps in environments where cloud resources and SaaS subscriptions now represent a large share of operational and financial risk.
- Treating it as a one-time document. An IT asset management policy should evolve with architecture, tooling, and regulation. If the review cycle is weak, the policy becomes outdated faster than teams realize.
- Focusing only on hardware. Software licensing, SaaS sprawl, and cloud resource governance are just as important as physical inventory. A policy that ignores them will miss some of the highest-risk and highest-cost parts of the estate.
How Cloudaware supports policy execution
With Cloudaware, teams can maintain a more accurate view of assets across cloud and on-prem environments, enrich records with business context, and use that data to support operational decisions around compliance, lifecycle, and cost control.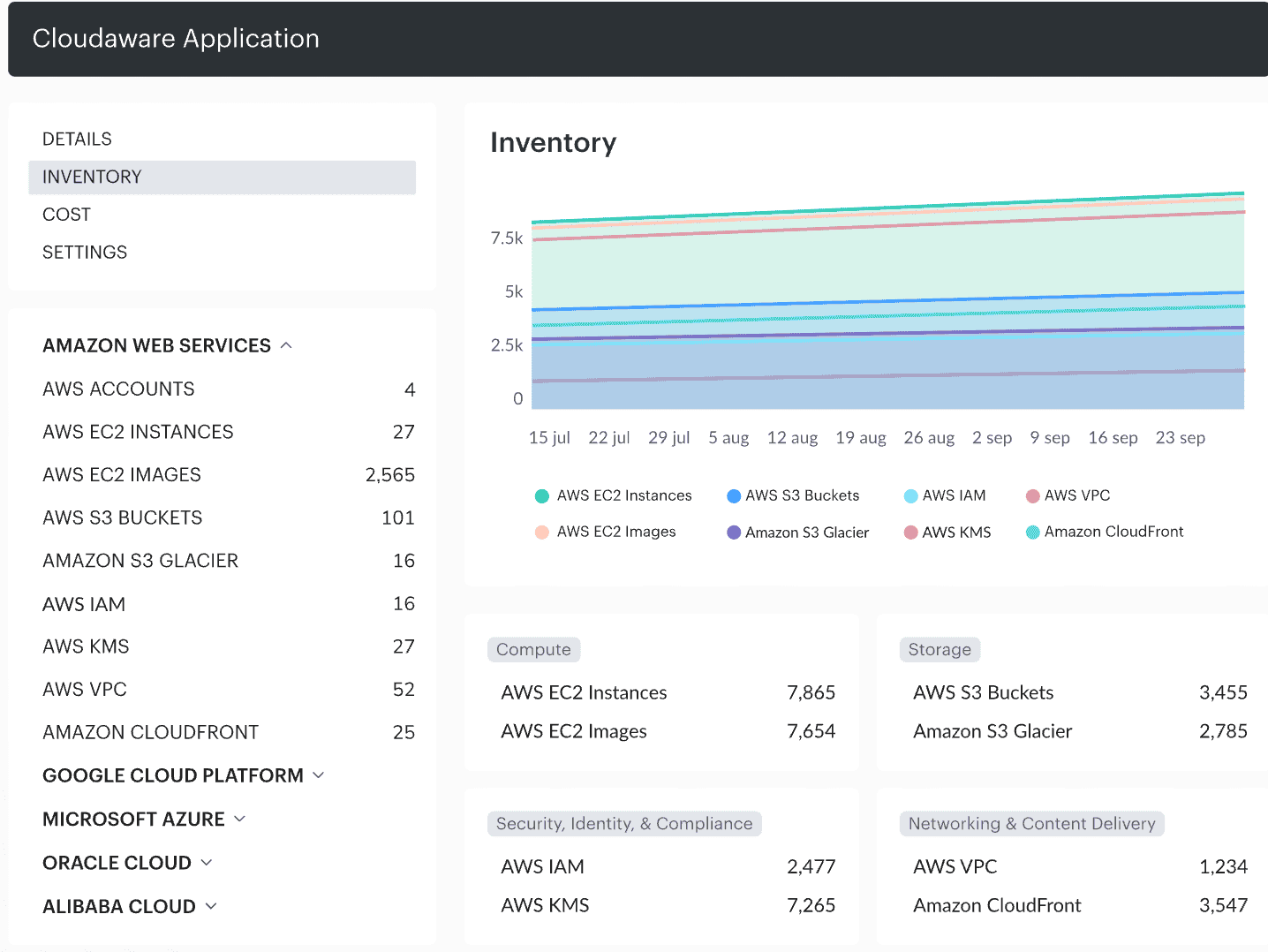 Organizations, including Coca-Cola, use Cloudaware to gain full visibility into asset states, reduce audit chaos, and enforce lifecycle policies without manual chasing.
Organizations, including Coca-Cola, use Cloudaware to gain full visibility into asset states, reduce audit chaos, and enforce lifecycle policies without manual chasing.
Key capabilities:
- Continuous multi-cloud asset discovery
- CMDB mapping across related items and services
- Lifecycle visibility and drift detection
- Context-rich asset tracking
- Compliance reporting and audit support
- Stronger cost visibility tied to asset and service data
