A cloud security assessment is a structured review of a cloud environment that evaluates infrastructure, identity, data protection, network exposure, and security controls. Effective cloud security assessments combine technical validation, risk analysis, and remediation planning.
Cloud risk grows faster than most teams can review it. New services, identity changes, third-party integrations, and configuration drift can weaken cloud security posture long before anyone notices, especially in multi-account and multi-cloud environments.
This guide explains how to conduct a cloud security assessment in six practical steps, from scope definition and asset inventory to IAM review, vulnerability validation, and remediation planning. It also shows how mature teams turn one-time cloud security assessments into a repeatable, continuous program.
TL;DR
- What is included in a cloud security assessment? Infrastructure, IAM, data protection, network exposure, logging, vulnerability findings, and remediation priorities.
- How often should cloud security assessments be done? Deep assessments should run on a defined cycle, while high-risk environments also need continuous monitoring for drift and new exposure.
- A cloud security assessment creates value only when findings are assigned, tracked, and verified to closure through a remediation workflow.
- Mature teams turn cloud security assessments into a continuous program with ongoing discovery, policy evaluation, cloud security analysis, and owner-based remediation.
What is a cloud security assessment?
A cloud security assessment is a structured, evidence-based review of a cloud environment that evaluates infrastructure, identity, data protection, network exposure, and security controls. It identifies misconfigurations, vulnerabilities, and compliance gaps before they turn into incidents or cost leakage.
In practice, it answers two questions: what is exposed right now, and what will it cost if it stays that way.
In AWS, that means more than checking S3 public access. It also means tracing IAM roles, STS assumptions, and cross-account trusts that can indirectly expose data. In Azure, the issue is often how Entra ID roles and service principals propagate access. In GCP, inherited IAM bindings at the project and folder levels can create exposure that teams do not see in dashboards.
A cloud security assessment is broader than a scan because it captures relationships: identity paths, implicit trust, and real attack surfaces. This is where cloud security analysis matters. The assessment gathers evidence, and the analysis turns it into decisions based on business impact.
Annual-only reviews no longer work. Cloud environments change daily, and drift accumulates faster than periodic reviews can catch it. A good assessment surfaces both security risk and cost inefficiency, including over-provisioned access, orphaned assets, and uncontrolled spend.
Assessment vs. audit vs. Cloud security analysis
A security assessment is forward-looking. An audit is compliance-driven and backward-looking. Cloud security analysis is where you decide what to fix first based on exposure, data sensitivity, and business impact. This is the layer that connects engineering work to financial risk.
| Aspect | Security Assessment | Security Audit | Cloud Security Analysis |
|---|---|---|---|
| Goal | Identify real risk and exposure across cloud environments | Prove compliance with frameworks | Prioritize risk for action |
| Scope | IAM, vulnerabilities, network exposure, data protection, configurations | Control adherence (SOC 2, ISO 27001, PCI DSS) | Business impact of findings |
| Focus | Current state of cloud security and attack surface | Whether required controls exist | What to fix first and why |
| Output | Findings across identity, vulnerabilities, exposure, and misconfigurations | Audit report and evidence | Remediation priorities and risk decisions |
| Timeframe | Continuous or periodic | Periodic | Ongoing |
Types of cloud security assessments
- Cloud infrastructure security assessments review compute, storage, networking, and account configurations across platforms such as AWS, Azure, and GCP, as well as other environments like Oracle Cloud or Alibaba Cloud, to determine what is deployed and how it is exposed.
- Infrastructure security assessment extends this to hybrid environments, focusing on trust boundaries between on-prem and cloud, including VPNs, identity federation, and segmentation gaps.
- Cloud vulnerability assessment focuses on identifying CVEs, unpatched workloads, and insecure configurations. This is the most standards-aligned assessment type, grounded in NIST technical security testing guidance.
- Cloud identity security assessment examines IAM roles, service accounts, federation, and privilege escalation paths, reflecting NIST guidance on cloud access control.
Additionally, organizations use a Cloud Security Alliance self-assessment (CSA STAR / CAIQ) to benchmark controls against the Cloud Controls Matrix and demonstrate security maturity.
Read also: Hybrid Cloud Security Architecture - Reference Architecture, Diagram, and Best Practices
Why cloud security assessments matter
A cloud security assessment matters because your attack surface grows faster than your review cycle. Every new microservice, IAM role, API integration, or third-party SaaS connection expands what can be reached, often without a corresponding update to security controls.
In multi-cloud environments, this fragmentation is worse: AWS, Azure, GCP, and other cloud platforms each introduce their own identity models, logging defaults, and network abstractions, and gaps appear exactly at those boundaries.
What it usually reveals: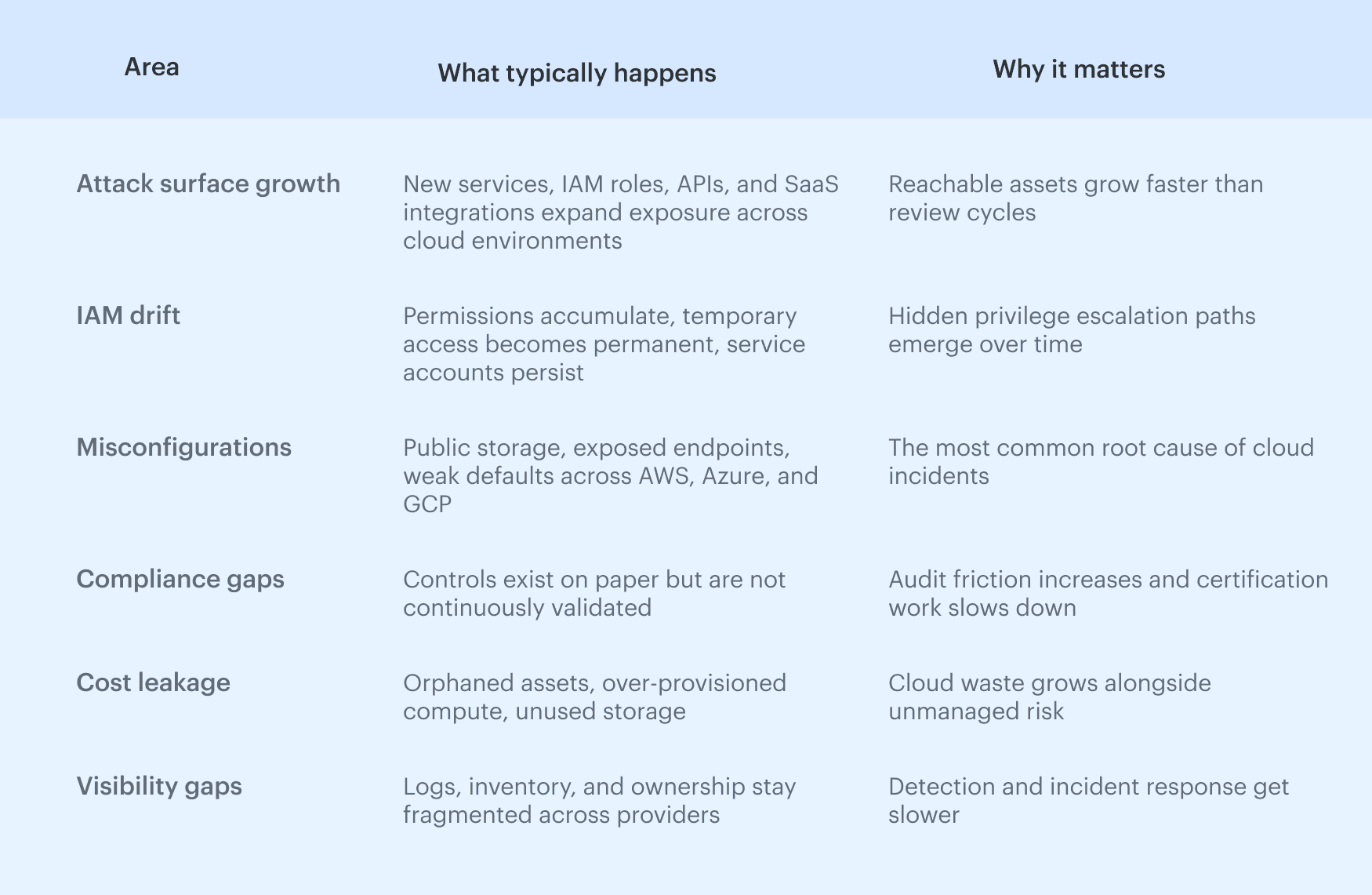 The most consistent pattern across environments is not zero-day exploits, but misconfigurations and IAM drift. Permissions accumulate, temporary access becomes permanent, and service accounts outlive their purpose.
The most consistent pattern across environments is not zero-day exploits, but misconfigurations and IAM drift. Permissions accumulate, temporary access becomes permanent, and service accounts outlive their purpose.
Over time, this creates invisible privilege paths:
- In AWS, that might be a role with iam:PassRole combined with Lambda execution
- In Azure, a service principal with broad contributor rights
- In GCP, inherited IAM bindings at the folder level are not revisited
A cloud infrastructure security assessment surfaces these paths before they are exploited.
There is also a hard compliance dimension. Frameworks like SOC 2, ISO 27001, PCI DSS, and GDPR require evidence that those controls are evaluated and enforced. A structured assessment produces evidence in a form auditors accept, reducing audit friction and shortening certification cycles.
Read also: Multi-Cloud Security Architecture. Reference Model and Best Practices
The risks a cloud security assessment is designed to surface
These risks rarely exist in isolation. A typical incident chain combines them: excessive access, public exposure, and missing logs. The role of a cloud security assessment is to surface these combinations early, before they converge into a material security event.
| Risk area | What it looks like in practice | Why it matters |
|---|---|---|
| Excessive access | Over-permissioned IAM roles, unused admin accounts | Enables privilege escalation and lateral movement |
| Public exposure | Open S3 buckets, public endpoints, exposed admin interfaces | Direct external attack surface |
| Weak encryption | Missing encryption at rest or outdated TLS | Sensitive data can be intercepted or leaked |
| Logging gaps | Disabled CloudTrail, missing audit logs, partial coverage | No visibility during incident response |
| Unmanaged changes | Drift from IaC, manual console changes | Breaks assumed security controls |
| Compliance drift | Controls defined but not enforced at runtime | Fails audits and increases regulatory risk |
| Network misconfiguration | Overly permissive rules, flat segmentation | Expands blast radius across the network |
For security teams, the value is not just risk reduction. It is control over change, measurable compliance, and the ability to tie technical findings directly to business impact.
Read also: Cloud Security Architecture. A Comprehensive Guide to Protecting Your Cloud Infrastructure
Cloud security assessment methodology
Without a repeatable cloud security assessment methodology, every cycle becomes a different exercise, findings can’t be compared over time, and improvement is impossible to measure.
What you need is the exact method that produces the same type of output regardless of whether you run it in AWS, Azure, or GCP.
A strong methodology does two things:
- Standardizes how you collect and interpret evidence across environments.
- Connects technical findings to decisions through cloud security analysis, so you are not just listing issues but actively prioritizing risk.
This is what allows you to evaluate your organization’s security posture consistently over time.
A repeatable cloud security assessment methodology
Every effective assessment follows five phases. You can change tools, but not these steps:
| Phase | What you do | Example (AWS / Azure / GCP) |
|---|---|---|
| Scoping | Define accounts, workloads, and objectives | AWS Organizations accounts, Azure subscriptions, GCP projects |
| Asset discovery | Build a complete inventory of resources and identities | AWS Config, Azure Resource Graph, GCP Asset Inventory |
| Control evaluation | Check configurations against expected controls | CIS benchmarks, custom policies, encryption, IAM |
| Risk analysis | Interpret findings using the business context | Public S3 with PII vs internal dev bucket |
| Remediation planning | Assign owners, timelines, and fixes | Jira tickets, ServiceNow workflows |
The real value comes from risk analysis. This is where evaluating technical findings turns into prioritization. A medium-severity issue on a production system processing customer data may be more critical than a high-severity issue in an isolated dev environment. This is the core of cloud security analysis.
Finally, remediation planning is what makes the assessment operational. Without ownership and tracking, findings decay into backlog noise.
Frameworks to use as your baseline
A methodology needs a reference point. Otherwise, “secure” becomes subjective. Most mature teams anchor their cloud security assessment to a combination of industry frameworks:
- NIST CSF (Cybersecurity Framework). Provides a high-level structure (Identify, Protect, Detect, Respond, Recover) that helps align technical findings with business risk and management reporting.
- CIS Benchmarks. These are the most practical baselines for cloud configuration. They map directly to services like AWS IAM, Azure storage, and GCP networking, making them useful for day-to-day evaluation of configurations.
- CSA Cloud Controls Matrix (CCM). A comprehensive set of cloud-specific controls that map to multiple regulatory frameworks. Useful when you need to connect technical findings to compliance requirements.
- Cloud Security Alliance Self-Assessment (CSA STAR). Often used for external validation. While less technical, it provides a standardized way to demonstrate maturity to partners and customers, especially in enterprise deals.
You use frameworks as baselines, then adapt them to your architecture, risk tolerance, and business model. A fintech platform handling regulated data will prioritize different controls than a SaaS analytics tool.
Read also: Cloud Workload Security - A Cross-Cloud Guide for 2026
How to conduct a cloud security assessment step by step
A cloud security assessment only works when it follows a clear sequence. Each step builds on the previous one, and skipping early stages breaks everything that comes after.
If your inventory is incomplete, your prioritization will be wrong. If your IAM review is shallow, your risk model will be misleading. This is how to conduct a cloud security assessment in a way that produces decisions.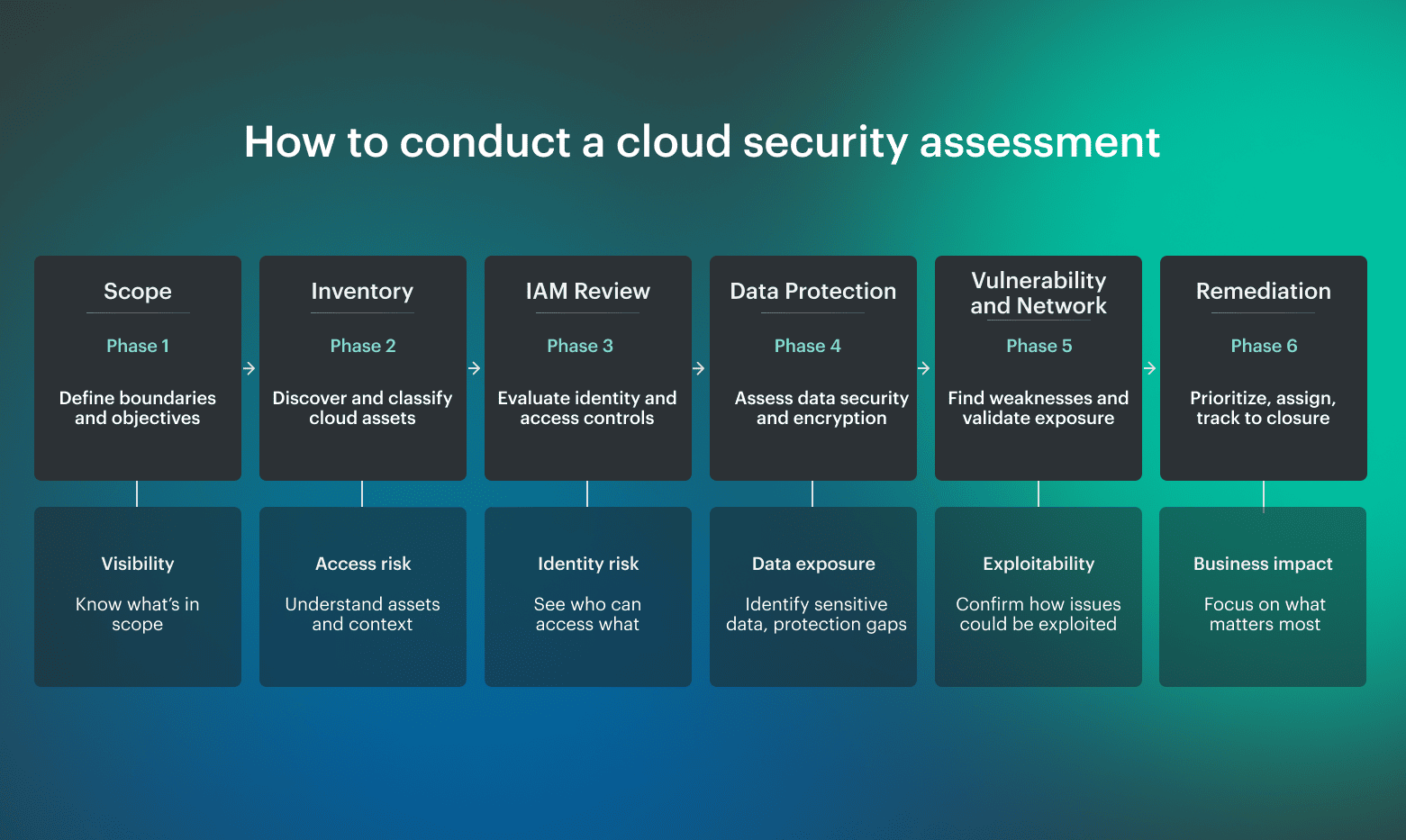
Step 1: Define scope and objectives
A cloud security assessment starts with boundaries. Before you review anything, define what is in scope and why this cycle exists.
Include:
- Cloud accounts and providers in scope (AWS Organizations, Azure subscriptions, GCP projects)
- Workload tiers (production, staging, development)
- Applicable compliance requirements
- Primary objective, such as audit readiness, post-incident review, or validation of a new deployment
Assign one owner to run the process. Without ownership, findings stall. The most common failure mode at this stage is scope creep, which turns a focused assessment into noise.
Step 2: Inventory and classify cloud assets
A cloud infrastructure assessment depends on complete visibility. Enumerate cloud assets across compute, storage, identity, and networking with cloud-native inventory sources such as AWS Config, Azure Resource Graph, and GCP Cloud Asset Inventory.
Then classify assets by:
- Data sensitivity
- Business criticality
- Environment
- Ownership
This baseline is what makes later prioritization possible. Without it, teams are identifying issues without knowing which ones matter.
Step 3: Evaluate identity and access controls
This step functions as a cloud identity security assessment inside the broader process. In real environments, identity usually defines the actual attack surface more than infrastructure settings do.
| Review | Look for |
|---|---|
| Users, roles, and service accounts | Excessive access |
| Federation paths (SAML, OIDC) | Missing MFA |
| Cross-account or cross-project trust relationships | Stale credentials |
| Privilege escalation paths | Overlapping permissions |
In AWS, focus on role chaining and STS assumptions. In Azure, review Entra ID roles and app registrations. In GCP, pay close attention to inherited IAM bindings.
Step 4: Assess data protection and encryption
This step checks whether sensitive data is actually protected, not just whether encryption exists somewhere in the stack.
Review:
- Public storage exposure
- Encryption at rest and in transit
- Key management configuration
- Backup integrity and recovery coverage
Use discovery tools such as Macie, Purview, or GCP DLP where needed. Most teams underestimate how much sensitive data exists outside the systems they actively track. In practice, weak access control around encrypted data creates more risk than missing encryption alone.
Step 5: Conduct a cloud vulnerability assessment and network review
A cloud vulnerability assessment identifies technical weaknesses across workloads, but it must be combined with network analysis to be meaningful.
| Review area | What to check |
|---|---|
| Workload scanning | VMs, containers, serverless workloads, operating system packages and dependencies, known CVEs |
| Exposure validation | Open management ports, flat network segmentation, public admin interfaces |
Correlate vulnerabilities with context. A critical CVE on an internal system is not equal to one on a public-facing API handling data. Most breaches follow this chain: vulnerability, exposure, identity misuse. This step connects those layers and informs response prioritization.
Step 6: Build a cloud security assessment and remediation plan
A cloud security assessment & remediation process creates value only when findings are turned into tracked work.
| Part | What it should include |
|---|---|
| Finding record | Affected resource and evidence, severity and exploitability, data sensitivity, business impact |
| Remediation workflow | Assigned owner, remediation date, tracking in Jira or ServiceNow, closure verification |
A cloud security assessment is complete only when findings are fixed and validated. A report on its own changes nothing.
3 сloud security assessment best practices
Run enough cloud security assessments, and a pattern shows up: execution is the main stall point. Teams know how to scan environments and review configurations, but struggle to make results repeatable and enforceable.
This section builds on guidance from NIST, CIS, and practitioners like Guy Podjarny and Rich Mogull, combined with observed failure patterns in real cloud environments.
These cloud security assessment best practices turn a one-time assessment into an operating model.
Move from point-in-time reviews to continuous monitoring
A periodic assessment gives you a snapshot, but cloud environments do not behave in snapshots. IAM changes, new deployments, and configuration drift continuously reshape your cloud security posture.
“Organizations should continuously monitor information system security controls.” — NIST, SP 800-137
Focus on high-impact security controls to reduce time-to-detect and incident response cost:
- Public exposure (storage, endpoints)
- IAM changes and privilege escalation paths
- Logging gaps
- Configuration drift
Shift cloud security analysis left into IaC and delivery workflows
The cheapest fix is the one that never ships. Push cloud security analysis into Terraform/CloudFormation and CI/CD so policy violations fail before deploy.
“The only way to scale is to build security into the surroundings of developers.” — Guy Podjarny, co-founder of Snyk
Enforce pre-deploy checks to shrink downstream assessment volume and stabilize cloud security across multi-cloud:
- Block public storage
- Require encryption defaults
- Validate IAM permissions
- Flag risky network rules
Map findings to controls and owners
Findings without ownership are backlog noise. Each item should map to a control, an owner, and an SLA.
“You build it, you run it.” — Werner Vogels, Amazon CTO
To make remediation work:
- Map each finding to a specific control (CIS, NIST, CCM)
- Assign a clear owner in engineering, not just security
- Define response expectations through SLAs
- Track closure as part of normal delivery workflows
Use CCM to tie issues to compliance while assigning owners in engineering. For example: critical findings should have a named owner and a 7-day remediation target, high issues should be closed within 30 days, and medium findings should be tracked or explicitly accepted as risk.
Read also: Cloud Security Best Practices. Strategy, Checklist, Monitoring, and Automation
How Cloudaware helps turn assessments into a continuous program
A well-executed cloud security assessment gives you a snapshot. The problem is keeping that snapshot up to date as your cloud environment changes.
This is where Cloudaware shifts the model from periodic reviews to a continuous system that aligns directly with how modern infrastructure operates.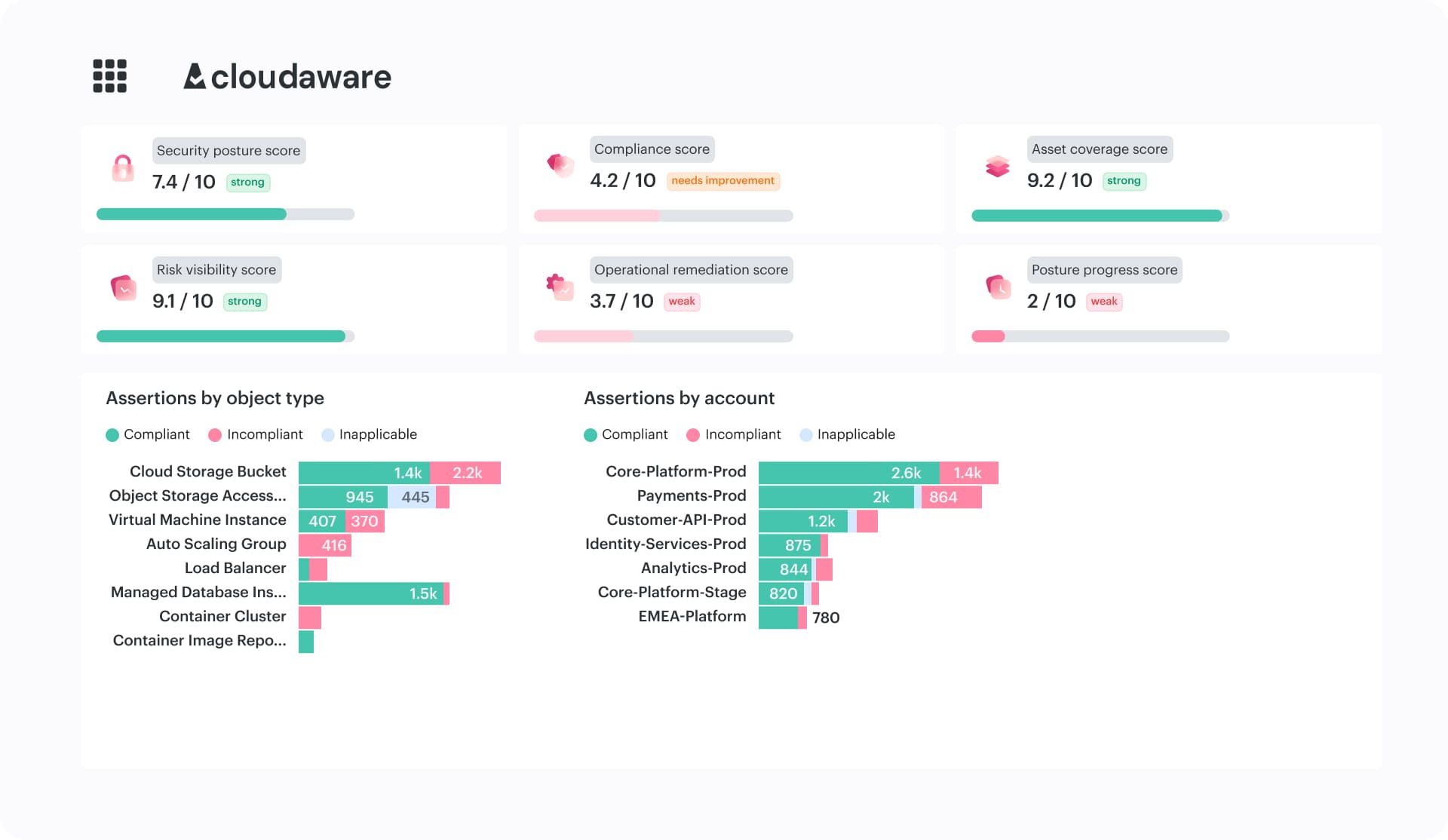
- Continuous asset discovery across AWS, Azure, GCP, and other cloud platforms, as well as VMware and on-prem environments. Maintains a near real-time CMDB, so teams do not have to rebuild inventory for every assessment.
- Continuous posture evaluation through the Compliance Engine. Evaluates the environment against 700+ policies mapped to CIS, NIST, PCI DSS, SOC 2, and GDPR.
- Custom policies for real operating conditions. Let teams adapt checks to their own tagging rules, approved exceptions, and architecture patterns instead of generating noise.
- Multi-layer cloud security analysis. Automates IAM review, configuration validation, and checks associated with cloud identity security assessment and cloud vulnerability assessment.
- Remediation workflows based on CMDB context. Breaks findings down by application, owner, environment, team, or severity so work reaches the people who can fix it.
- Centralized logging and IDS visibility. Combines cross-cloud log aggregation through Conflux with Wazuh-based IDS to reduce fragmentation and improve security visibility.
