You can have Entra ID, Conditional Access, Defender for Cloud, Sentinel, Azure Policy, and Key Vault in place, and still, your Microsoft Azure cloud security will break when controls do not work together. Identities not tied to assets, policies not enforced across subscriptions, findings with no owner, and alerts that sit in a queue because no one knows what system they belong to.
That is where most security risks show up. Microsoft’s Zero Trust guidance says the quiet part clearly: assume breach, verify explicitly, and use least privilege access. Microsoft also reports more than 600 million cybercriminal and nation-state attacks against its customers every day, with password-based attacks making up over 99% of daily identity attacks.
So this guide does not treat Azure cloud security best practices as generic Azure security recommendations. It combines Cloudaware expert input, real engineering pain points shared in Reddit discussions, and industry benchmarks.
The goal is to treat cloud security in Azure as an operating model that connects identity, configuration, workload posture, ownership, and response before the gaps turn into incidents.
Top Azure cloud security best practices
If you only fix a few things, start here. These are the controls that consistently reduce real risk in Azure environments, not just improve dashboards or scores.
- Structure Azure RBAC around management hierarchy
- Enforce Conditional Access based on risk
- Eliminate standing privilege with PIM and JIT
- Apply Azure Policy at the management group level
- Block public exposure by default
- Segment workloads to limit lateral movement
- Centralize secrets and keys in Azure Key Vault
- Treat data encryption as a baseline and control access paths
- Use Defender for Cloud for continuous posture management
- Assign ownership to every alert, finding, and exception
Azure cloud security as an operating system
If you’ve worked in a few Azure environments, you already know this: nothing breaks because a control doesn’t exist. It breaks because controls exist in isolation. Most Azure cloud security framework guidance stops at listing controls, so we will try to dive deeper here. Image source.
Image source.
Azure fail patterns usually show up at the system level, when identity isn’t connected to assets, assets aren’t mapped to applications, applications aren’t tied to business context, and alerts aren’t routed to owners. That is the gap most Azure cloud security guidance still doesn’t address.
The shared responsibility model doesn’t explain where things go wrong
The Azure Shared responsibility model (SRM) is useful, but only to a point. Microsoft secures the physical infrastructure, host OS, and core platform services, while the customer secures identities, configurations, workloads, and data.
That part is clear. Where teams get into trouble is everything between those layers:
- Misconfigured RBAC roles
- Exposed storage accounts
- Overly permissive network rules
- Stale or orphaned resources
Most Azure security challenges are structural
After enough audits, patterns repeat. The biggest Microsoft Azure security challenges are structural:
- Subscription sprawl. Different teams, different standards, inconsistent controls
- Policy drift. What was compliant at deployment is no longer compliant today
- Ownership gaps. No clear mapping between resources, applications, and teams
- Alert fatigue without context. Too many findings, not enough prioritization
- Tool fragmentation. Defender, Sentinel, Policy, and Entra ID are all working, but not connected
Microsoft tools may all be working, but if they do not share assets, ownership, and application context, security still depends on manual correlation.
Treat Azure security as a checklist, and these gaps will accumulate. Treat it as a system, and they become visible and manageable.
Top 3 Azure identity and access management best practices
These Azure security best practices focus on identity because most incidents start there. Not because IAM is hard to configure, but because it drifts. Access gets added faster than it gets reviewed, service principals outlive the workloads they were created for, and exceptions quietly become the default.
That is why Azure identity and access management is not about “least privilege” as a principle. Microsoft has been consistent on this point. In their Zero Trust model, identity is the primary control plane, not the network perimeter. In practice, that means every access decision should answer three questions: who, under what conditions, and for how long.
Structure Azure RBAC around management hierarchy
Azure RBAC works well when it reflects how your environment is actually organized. In most enterprise setups, that means assigning roles at the management group or subscription level, not directly on resources unless there is a clear exception.
Built-in roles like Contributor get reused because they are convenient, not because they are appropriate. Over time, that creates broad, persistent access that no one fully tracks.
A more stable pattern:
- Define roles around job function, not individual tasks
- Avoid assigning permissions directly to users where possible
- Review role assignments periodically, not just during audits
Enforce Conditional Access based on risk
Azure Conditional Access is where IAM moves from static configuration to adaptive control. Instead of allowing or denying access universally, policies define the conditions under which access is granted.
The common failure pattern is treating Conditional Access as a one-time setup. Policies get created, but they are not aligned with real risk signals. Features like impossible travel or risky sign-ins exist, but they are not enforced through policy.
A more stable pattern is to enforce access dynamically: increase controls as risk rises, rather than applying maximum friction to every login.
Kristina, Senior Technical Account Manager at Clodaware:
“A practical example: instead of enforcing multi-factor authentication (MFA) everywhere equally, enforce stronger controls when risk increases. That reduces friction while still aligning with Zero Trust.”
Eliminate standing privilege with PIM and JIT
Standing admin access is still one of the easiest ways to lose control of an environment. Azure Privileged Identity Management reduces that risk by turning permanent access into time-bound access that requires activation, justification, and sometimes approval.
Just-in-time access applies the same idea to infrastructure. Instead of leaving management ports open on virtual machines, access is granted only for a defined time window and from approved sources.
Mikhail Malamud, Cloudaware GM:
“In most Azure environments we assess, identity is broken because no one owns the lifecycle.
Once every role, identity, and exception has a clear owner and a defined review process, IAM stops drifting and starts behaving like a controlled system.”
Read also: Cloud Security Best Practices. Strategy, Checklist, Monitoring, and Automation
Azure governance and policy enforcement best practices
Most Azure security issues come from controls that are applied in the wrong place or not applied consistently.
If IAM defines who can act, then Azure policy and governance define what is allowed to exist in your environment. And that only works if you understand the hierarchy you are operating in.
Apply Azure Policy at the management group level
Azure hierarchy is the backbone of Azure governance. Management groups define global guardrails, subscriptions isolate workloads, and resource groups group assets with shared lifecycle.
Iurii Khokhriakov, Technical Account Manager at Cloudaware:
“The common failure pattern is treating these layers as labels. Policies get applied at the subscription level only, then new subscriptions appear outside the structure, and each environment starts behaving differently.
A more stable pattern is to treat the hierarchy as an enforcement model. Apply baseline policies at the management group level so new subscriptions inherit guardrails automatically.”
Use RBAC and Policy together
RBAC and Policy are often confused, but they solve different problems.
| RBAC | Azure Policy |
|---|---|
| Controls who can do something | Controls what can be done |
Stop relying on RBAC alone. Teams assume restricted access is enough, but users with valid permissions can still deploy insecure configurations, such as public storage or open network paths.
Daria, Сloud Security Expert at Cloudaware:
“In most Azure environments we assess, governance breaks at the edges. That is where policy gaps, inconsistent configurations, and unmanaged resources accumulate.”
The biggest improvement usually comes from pulling those environments back into a single hierarchy and enforcing policies consistently across all subscriptions. Once that happens, governance stops being reactive and starts behaving like a system.
Read also: Cloud Security Assessment. Methodology, Checklist, Best Practices, and Remediation
Azure network security and zero trust segmentation best practices
Many Azure incidents become worse because once something is inside, it can move too freely. That’s the difference between having Azure network security controls and actually using them as part of a Zero Trust model.
In Azure, network design is less about building a perimeter and more about controlling lateral movement and exposure between services.
Block public exposure by default
In Azure, the fastest way to create unnecessary risk is to leave storage accounts, databases, Kubernetes APIs, or management endpoints reachable from the internet long after the original setup is finished.
This usually happens during deployment. A team opens public access temporarily for testing, migration, or vendor integration. Months later, the endpoint is still exposed because nobody owns the exception anymore.
Microsoft has repeatedly highlighted publicly exposed storage and identity misconfigurations as one of the most common cloud incident patterns. In practice, most teams do not discover these exposures during deployment. They discover them during audits or after Defender for Cloud starts generating alerts.
What actually holds up in production:
- Private endpoints by default
- Explicit approval for internet exposure
- Expiration date for every exception
- Continuous review of externally reachable assets
Segment workloads to limit lateral movement
A pattern we see constantly in Microsoft Azure security assessments: teams separate dev from prod, but inside production, almost everything can still talk to everything else. Frontend services reach databases directly, management ports stay open between subnets, and broad NSG rules quietly accumulate over time because nobody wants to break application traffic.
Microsoft’s Zero Trust guidance assumes breach for exactly this reason. Once an attacker lands inside a workload, overly permissive east-west traffic becomes the fastest path to privilege escalation and lateral movement across the environment.
What usually holds up better in production:
- Separate frontend, application, and data tiers
- Isolate regulated or internet-facing workloads into dedicated segments
- Keep NSG rules explicit and minimal
- Validate segmentation against actual traffic patterns and flow logs
- Review peering relationships regularly, especially after migrations or acquisitions
Read also: How to Conduct a Cloud Security Assessment (A Step-by-Step Guide)
Azure data security and key management best practices
Good Azure data security depends on how consistently teams manage keys, secrets, and access paths. Azure enables data encryption at rest and in transit by default for many services, but that can create a false sense of coverage. That creates a false sense of coverage. The control exists, but the way keys, secrets, and access are handled still determines whether data is actually protected.
Centralize secrets and keys in Azure Key Vault
Azure Key Vault should be the only place where applications retrieve credentials, API keys, certificates, and encryption material. Access should go through managed identities and RBAC, not embedded credentials or copied secrets.
Kristina, Senior Technical Account Manager at Clodaware:
“This sounds obvious until you audit a few environments. Secrets usually leak into the estate through convenience: an app setting added during deployment, a CI/CD variable created for a release, a local config file used for testing, a certificate copied between teams because rotation would “take too long.” None of it looks dangerous on day one. Six months later, nobody knows which copy is active.”
What holds up better:
- Use Azure Key Vault as the source of truth for secrets, keys, and certificates
- Authenticate workloads with managed identities where possible
- Remove secrets from app settings, repos, pipelines, and local files
- Define rotation owners and expiration rules
- Alert on stale, unused, or broadly accessible secrets
Read also: The Future of AI in Cloud Security - Trends & Benefits for 2026
Treat encryption as a baseline and control access paths
Azure encryption at rest is enabled by default for most services, and encryption in transit typically relies on TLS for supported Azure services and application traffic. That is good baseline hygiene, but it is not the same as data security.
The mistake is assuming that encrypted means protected. An encrypted storage account with public access enabled is still exposed. An encrypted database with broad identity permissions is still reachable. An encrypted backup copied into the wrong subscription still creates risk.
What matters is the access path around the data: who can reach it, from where, through which identity, and whether that access is still justified.
Daria, Сloud Security Expert at Cloudaware:
“A lot of Azure reviews start the same way. Defender is on, Key Vault exists, NSGs are configured, and encryption is enabled. Then we start following the path a real issue would take.
A storage account is still public because someone opened it during a migration. A database is encrypted, but half the app team can still reach it through broad permissions. A subnet is labeled ‘prod,’ but every tier inside it can talk to every other tier. The environment just kept moving, and the security model did not keep up.”
The teams that avoid this usually have one thing in common: every exception has an owner, every exposed path is reviewed, and every control is checked against how the workload actually runs, not how the diagram said it should run six months ago.”
Read also: Hybrid Cloud Security Architecture. Reference Architecture, Diagram, and Best Practices
Azure CSPM, detection, and response best practices
Many Azure environments remain exposed because posture, detection, and response are not connected. Defender for Cloud, Microsoft Secure Score, Sentinel, Azure Policy, and logs all provide useful signals. The hard part is turning those signals into prioritized work.
Use Defender for Cloud for continuous posture management
Microsoft Defender for Cloud is useful because it keeps evaluating the environment after deployment. It continuously checks Azure resources for exposure, configuration drift, and compliance gaps, then turns those checks into Azure security recommendations and Microsoft Secure Score signals.
Iurii Khokhriakov, Technical Account Manager at Cloudaware:
“A pattern we see often: a storage account gets flagged for public exposure, Defender generates the recommendation, Secure Score drops slightly, and the finding stays open for months because nobody knows which application team owns it. During audits, teams suddenly discover dozens of the same unresolved issues across multiple subscriptions.”
Mature teams treat Defender findings like incidents or engineering tasks. The useful question is not “What is our Secure Score?” The useful question is “Which exposed resource creates the highest operational risk right now, and who is responsible for fixing it?”
Read also: 9 AWS Cloud Security Best Practices - A Practitioner’s Guide to Securing Your Cloud
Prioritize findings based on exposure and context
A missing tag, an unencrypted test disk, and a publicly exposed storage account should not land in the same queue with the same urgency.
If you understand this, you understand why CSPM programs fall apart. Defender for Cloud can surface the issue, but it cannot always tell you what the issue means to the business. Is the resource public? Does it hold regulated data? Is it tied to a production workload? Does a privileged identity have access to it?
Mikhail Malamud, Cloudaware GM:
“A practical example: two storage accounts have the same security recommendation. One belongs to a sandbox subscription with no sensitive data. The other supports a customer-facing production application and is reachable from the internet. Same recommendation, very different risk.”
Assign ownership to every alert and finding
Azure threat detection only works if alerts can move into response. Logs, Sentinel alerts, and Defender findings are useful only when someone knows who owns the affected resource.
The common failure pattern is routing everything to a shared queue. Alerts are generated, but no one knows whether the affected asset supports a test app, a customer-facing workload, or regulated data.
A more stable pattern is to connect every alert and finding to the asset owner, application, environment, and escalation path.
Kristina, Senior Technical Account Manager at Clodaware:
“In most Azure environments we assess, CSPM and detection are present but not operational. The biggest improvement comes from connecting posture data and alerts to ownership. Once every finding is tied to a resource, application, and team, remediation starts happening consistently.”
Read also: Cloud Security Architecture. A Comprehensive Guide to Protecting Your Cloud Infrastructure
Azure security checklist and implementation priorities
This Azure security checklist focuses on controls that reduce risk quickly and are realistic to implement. Use it as a practical rollout plan instead of trying to fix everything at once.
First 30 days
Start with the controls that reduce the most risk quickly:
- Review RBAC assignments and remove unnecessary Contributor access
- Enforce MFA and Conditional Access for privileged users
- Enable or review PIM for high-impact roles
- Apply baseline Azure Policy at the management group level
- Identify public storage, databases, and management endpoints
- Confirm Defender for Cloud coverage
- Define a logging baseline for identity, activity, and resource logs
Next 90 days
Move from baseline controls to operating model:
- Standardize subscription and management group structure
- Enforce private endpoints for sensitive services
- Segment workloads by tier and blast radius
- Centralize secrets in Azure Key Vault
- Define key rotation and expiration processes
- Prioritize Defender findings by context
- Assign owners to alerts, findings, and exceptions
Metrics that matter
Track whether security work actually moves:
- % of Azure resources with an assigned owner
- Number of unmanaged public endpoints
- Number of high-risk findings without the owner
- Average age of policy exceptions
- Mean time to route alerts
- Mean time to remediate high-risk findings
- % of subscriptions covered by baseline policies
Read also: Cloud Workload Security (A Cross-Cloud Guide for 2026)
How Cloudaware operationalizes Azure security
Azure-native tools already give you most of the controls you need. Microsoft Defender for Cloud shows posture, Microsoft Sentinel aggregates signals, Azure Policy enforces configuration, and Microsoft Entra ID handles identity.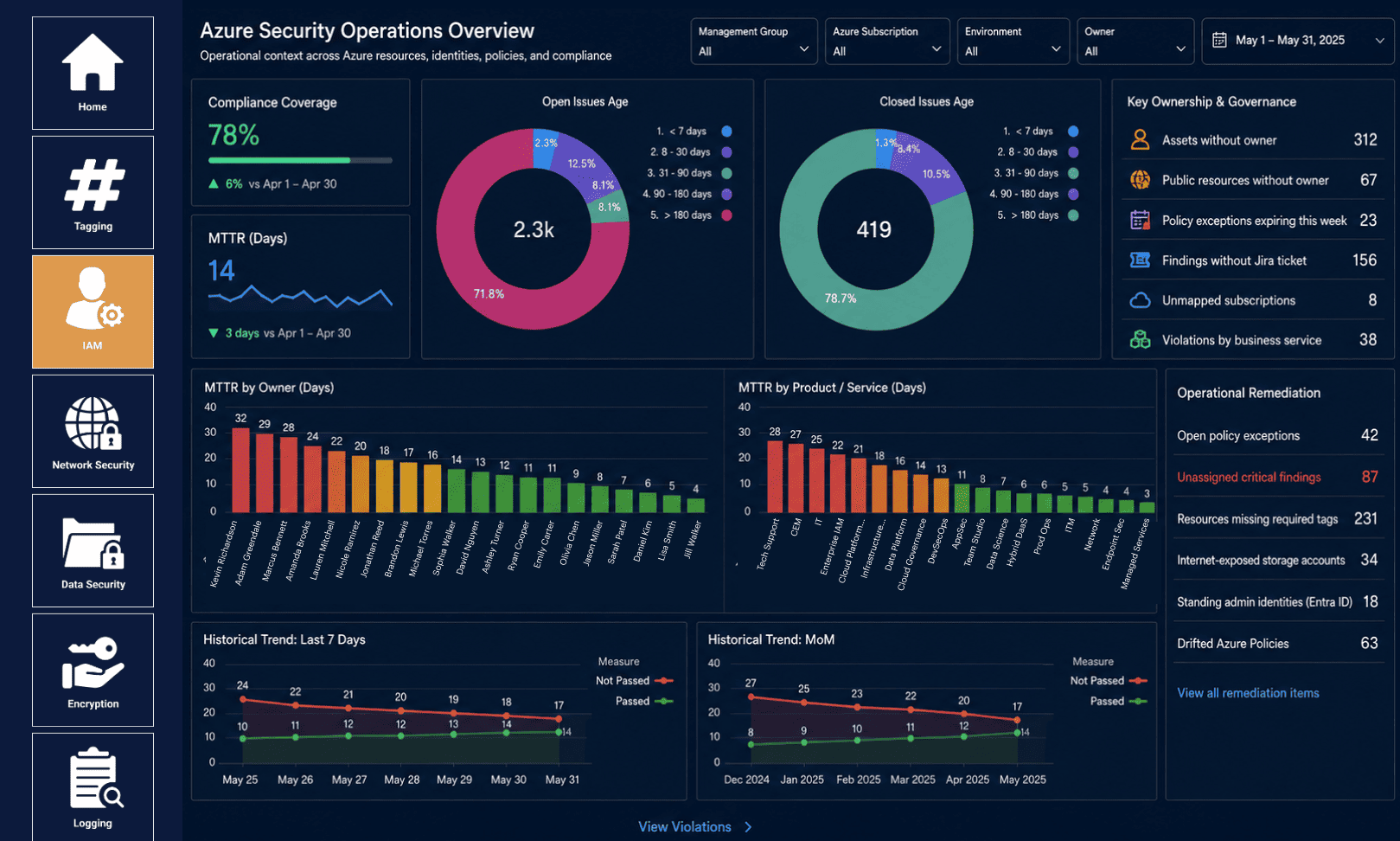 But how do those signals turn into action? That is where an Azure security management platform becomes relevant. Cloudaware provides a CMDB cloud asset inventory that maps Azure resources to ownership, applications, and environments.
But how do those signals turn into action? That is where an Azure security management platform becomes relevant. Cloudaware provides a CMDB cloud asset inventory that maps Azure resources to ownership, applications, and environments.
- Connect assets to ownership and context. Cloudaware provides a centralized asset inventory (CMDB) that discovers Azure resources and links them to owners, applications, and environments.
- Make IAM and RBAC auditable at scale. By correlating identity data with resource inventory, Cloudaware helps teams understand which identities have access to which assets across subscriptions.
- Turn findings into assigned work. Cloudaware enriches security findings with context such as resource, environment, and ownership, and integrates with ticketing systems to support remediation workflows.
- Severity alone does not reflect real risk. Cloudaware uses asset relationships and metadata (such as environment, ownership, and resource type) to help prioritize issues based on impact.
- Track IT compliance and evidence. Cloudaware maps cloud configurations to compliance frameworks and tracks changes over time, helping teams maintain continuous visibility into compliance posture and simplifying audit preparation.
- Extend Azure practices to multi-cloud environments. Cloudaware supports AWS, Azure, GCP, and hybrid environments, providing a unified model for asset visibility, security posture, and compliance.
