A cloud security framework is the operating system for cloud risk: standards, ownership, controls, evidence, and enforcement working across AWS, Azure, GCP, and on-prem. The best cloud security frameworks do not live in PDFs. They show up in IAM decisions, policy checks, audit trails, remediation queues, and architecture reviews.
You’ll learn to turn governance from “we have controls” to “we can prove what changed, who owns it, and why it matters.”
This guide is built from the freshest field insights we hear inside Cloudaware, including Valentin Kel and Igor K., and from the enterprise security teams we work with every day: cloud security leaders, architects, DevSecOps leads, platform engineers, and compliance owners running AWS, Azure, GCP, and on-prem at real scale.
So here’s the case file:
- Which standards actually matter when one workload crosses four environments?
- Where does governance break first: identity, ownership, evidence, or drift?
- Why do audits still hurt when tools already collect the data?
- What makes multi-cloud implementation fail quietly before anyone sees risk?
Key insights
- A cloud security framework is not a PDF your team dusts off before an audit. It is the operating model that connects controls to real assets, owners, environments, exceptions, remediation paths, and evidence across AWS, Azure, GCP, SaaS, Kubernetes, and on-prem.
- The best framework depends on the pressure point. NIST CSF 2.0 gives you the governance spine. CSA CCM is strongest for cloud-native control mapping. CIS Controls and Benchmarks help platform teams harden real configurations. SOC 2, ISO 27017, PCI DSS, HIPAA, and FedRAMP matter when customers or regulators can block the business.
- A cloud security governance framework answers the question tools usually cannot: who decides, who fixes, who accepts risk, and who proves the control worked? Without that ownership layer, even good findings turn into forwarded tickets and slow remediation.
- Multi-cloud breaks lazy control mapping. “Encrypt sensitive data” becomes AWS KMS, Azure Key Vault, Google Cloud KMS, storage policies, database settings, backup rules, IAM boundaries, and audit evidence. The control intent stays the same. The implementation does not.
- SaaS needs its own framework lens because risk hides in OAuth grants, SCIM gaps, dormant admins, local users bypassing SSO, external sharing, and vendor-side audit logs. HR SaaS deserves extra scrutiny because Workday, BambooHR, Rippling, and similar tools often hold the densest PII stack in the company.
- The metrics that matter are not vanity counts. Track guardrail coverage, MTTR for critical misconfigurations, percentage of controls with automated evidence, and framework coverage gaps. Those four numbers show whether governance is actually moving risk or just reporting it.
- Frameworks become useful only when they touch the cloud estate. A failed control should show the asset, provider, owner, environment, mapped standard, related change, exception status, remediation ticket, and proof. That is the difference between “we follow NIST” and “we can prove this production workload is governed.”
What is a cloud security framework?
A cloud security framework is the operating model that tells your cloud teams how security should work in real environments: what must be protected, which controls apply, who owns each risk, how violations get found, and what evidence proves the issue was handled.
Here is a common case: In AWS accounts, there are 400 forgotten security groups. In Azure subscriptions, one team owns the app while another team owns the network. In GCP projects spun up for analytics, then quietly promoted into business-critical workflows.
The framework is what keeps all of that from becoming “we think someone checked this.”
A cloud security governance framework goes one layer deeper. It defines the rules of responsibility:
- Who approves exceptions
- Who signs off on policy breaches
- How fast production risk must be remediated
- Where audit evidence lives when compliance asks for proof six months later
That is the whole point.
A framework turns cloud security from scattered good intentions into an accountable system.
What a cloud security framework includes
Think of it as seven moving parts, not seven static documents:
| Element | What it answers in real cloud work |
|---|---|
| Asset scope | Which AWS accounts, Azure subscriptions, GCP projects, Kubernetes clusters, SaaS apps, and on-prem systems are actually covered? |
| Control baseline | Which requirements matter here: CIS, NIST, ISO 27001, CSA CCM, PCI DSS, SOC 2, HIPAA, DORA, internal architecture rules? |
| Ownership map | Who owns the workload, data, identity, network path, exception, and remediation? |
| Preventive guardrails | What gets blocked before it becomes a finding: public storage, risky regions, weak encryption, broad IAM, unapproved images? |
| Continuous detection | What catches drift after deployment: disabled logging, open ports, missing tags, exposed services, policy breaches? |
| Remediation workflow | How does a failed control become action, not noise? Ticket, owner, SLA, approval, verification. |
| Evidence trail | Can the team prove what failed, when it changed, who fixed it, and which control it maps to? |

Cloud security framework vs. cloud security standard vs. policy
| Term | Definition | Example | Owner |
|---|---|---|---|
| Framework | The full operating model for governing, enforcing, monitoring, remediating, and proving cloud security controls. | Enterprise cloud security framework mapped across AWS, Azure, GCP, Kubernetes, and on-prem systems. | CISO, cloud security leadership, GRC, cloud platform leaders. |
| Standard | A recognized control set or benchmark used to define secure and compliant behavior. | CIS AWS Foundations Benchmark, NIST 800-53, CSA CCM, ISO 27001, PCI DSS 4.0. | Security architecture, compliance, audit, risk teams. |
| Policy | An internal rule that says what is allowed, required, blocked, or escalated. | “Production storage must block public access, enable logging, and use approved encryption.” | Control owner, platform engineering, DevSecOps, application owner. |
Here’s the clean mental model:
👉 The framework is the system.
👉The standard is the reference.
👉The policy is the rule your cloud actually has to follow.
In a single-cloud setup, teams can sometimes blur those lines and survive. Multi-cloud is less forgiving. One “encrypt data at rest” requirement turns into S3 bucket settings, Azure Storage configurations, GCP Cloud Storage controls, database encryption states, key management rules, Terraform checks, exception approvals, and evidence capture.
That is why cloud security frameworks matter in 2026. Not because teams need more governance language. They need a way to make security decisions travel cleanly from board-level risk to provider-specific enforcement without losing ownership halfway through.
7 Reasons why a cloud security framework matters in 2026
Cloud security in 2026 is not falling apart because teams lack controls.
The fracture happens later, when the control has to survive AWS, Azure, GCP, Kubernetes, SaaS, CI/CD, identity providers, on-prem dependencies, AI experiments, business exceptions, and the most dangerous phrase in cloud operations: “I thought that belonged to another team.”
That is why a cloud security framework matters now. It gives security leaders a way to turn standards into ownership, ownership into action, and action into evidence.
1. Hybrid cloud made “one control, one implementation” obsolete
73% of organizations operate hybrid cloud estates in 2026. (Flexera)
The old model was neat. One platform. One control plane. One team that knew where everything lived.
That is not the 2026 estate.
A single storage security rule now has to translate across S3 Block Public Access, Azure Storage public network access, GCP bucket IAM, private endpoints, KMS keys, audit logs, VPC Service Controls, and whatever file share still lives on-prem because the migration team ran out of budget.
Here is the argument: hybrid cloud does not break security because it has more platforms. It breaks security because every platform expresses the same control differently.
A framework keeps the intent stable. The implementation can change by provider, but the security question stays clean:
- Is this asset exposed?
- Is it encrypted?
- Who owns it?
- Was the exception approved?
- Can we prove the current state?
Without that layer, teams collect findings. They do not govern risk.
2. Complexity has become a security finding before the finding even exists
55% of organizations say securing cloud environments is more complex than securing on-premises environments. (Thales Group)
A security architect opens the dashboard and sees 1,800 misconfigurations.
Not great.
But the real problem is not the number. The real problem is that 600 of them have no clear application owner, 200 are tied to “temporary” environments, 90 sit in production-adjacent subscriptions, and nobody can explain whether that legacy VPN route is still required.
That is cloud complexity in its most expensive form.
It does not always announce itself as a breach. Sometimes it shows up as:
- a stale service account nobody wants to delete
- a Kubernetes namespace owned by a team that reorganized twice
- a public endpoint approved for testing and never reviewed again
- a SaaS connector with broad permissions because the integration “needed it once”
- a logging gap hidden behind three different dashboards
A cloud security governance framework matters because it gives complexity a routing system. Scope. Control. Owner. SLA. Exception. Evidence.
No drama. Just accountability.
3. Sensitive data moved into places security teams do not always inspect first
54% of cloud data was classified as sensitive in 2025, up from 47% in 2024. Only 8% of organizations encrypted 80% or more of their cloud data. That’s a fact from Thales Group research.
This is where the conversation gets uncomfortable.
Sensitive data is not only in the primary production database anymore. It is in logs, data lakes, snapshots, backups, model prompts, exported reports, temporary pipeline outputs, replicated buckets, and analytics workspaces created by teams that were “just testing something.”
So the question cannot stay at the policy level. “Do we protect sensitive data?” is too soft.
The better questions sound like an auditor with a flashlight:
- Which cloud asset holds the data?
- What classification does it carry?
- Is encryption enabled?
- Who owns the key?
- Which identities can read it?
- Are backups protected too?
- When was access last reviewed?
- Where is the evidence?
The argument is simple. Data protection fails when classification, access, encryption, retention, and evidence live in different conversations. A framework pulls those threads into one operating model.
Read also: Multi-Cloud Security Architecture - Reference Model, Layers, and Best Practices
4. Identity risk is no longer a side control. It is the control plane.
Among organizations with cloud-related breaches, excessive permissions were a cause in 31% of cases, inconsistent access controls in 27%, and weak identity hygiene in 27%. (Cloud Security Alliance)
That is the part most identity programs underestimate.
Cloud identity is not just employees logging into a console. It is service accounts, workload identities, federated roles, CI/CD tokens, API keys, OAuth grants, break-glass users, contractors, SaaS integrations, and old automation that still has write access because nobody wants to break deployment.
A mature framework does not stop at “review access quarterly.”
It defines what high-risk access means in AWS IAM, Azure Entra ID, GCP IAM, Kubernetes RBAC, and SaaS admin roles. It forces ownership for non-human identities. It expires exceptions. It tracks stale keys. It records why privileged access exists and who approved it.
The argument: least privilege is not a principle until your team can operate it across human and machine identities.
5. AI turned “shadow IT” into “shadow data movement”
IBM’s 2025 Cost of a Data Breach research found that 63% of breached organizations studied lacked AI governance policies. AI rarely enters the company wearing a badge that says “new enterprise risk.”
It arrives as a shortcut.
Support connects a chatbot to ticket history. Engineering lets an assistant read deployment notes. Finance uploads billing exports into a forecasting tool. Product analytics tests customer data against a model. Someone in compliance uses AI to summarize evidence packs.
Useful? Yes.
Governed? Often, no.
IBM also reported that one in five studied organizations had breaches linked to shadow AI, with those incidents adding as much as USD 670K to average breach cost. Source URL: IBM data breach insights.
This is why cloud security teams need to treat AI workflows like cloud assets.
Not vibes. Not panic. Asset logic.
- What can the AI tool access?
- Which cloud data does it touch?
- Where does output go?
- Is retention defined?
- Can prompts contain regulated data?
- Who approved the integration?
- What happens when the tool changes?
The argument: AI governance cannot sit outside cloud governance, because AI now consumes cloud data, cloud logs, cloud identities, and cloud cost data.
6. Cloud waste is often the first clue that ownership is broken
Estimated wasted cloud spend rose to 29% in 2026, reversing a five-year downward trend.
This one looks like FinOps.
It is not only FinOps.
An idle VM may be unpatched. A forgotten database may still hold regulated data. An old snapshot may be unencrypted. A test environment may have public exposure because everyone assumed it would be deleted after the sprint. A resource with no tags may also have no owner, no monitoring, no lifecycle state, and no remediation path.
Cloud waste is not automatically a security issue. But unmanaged spend is often sitting next to unmanaged risk.
A framework helps teams separate the categories that matter:
- expensive, approved, and business-critical
- idle, but intentionally retained
- forgotten, exposed, and ownerless
- noncompliant, but covered by an approved exception
- risky, production-linked, and overdue for remediation
The argument: when asset inventory, cost data, ownership, and policy status are disconnected, both FinOps and security work from partial truths. That is how waste survives. That is how risk survives too.
7. Attackers moved the timeline. Quarterly governance did not get the memo
Third-party software-based entry accounted for 44.5% of initial access vectors in H2 2025, up from 2.9% in H1 2025. The window between disclosure and mass exploitation collapsed from weeks to days. That’s data from Google Cloud Threat Horizons Report H1 2026.
Now put that into an actual cloud
Monday: a critical CVE drops.
Tuesday: exploit attempts start hitting internet-facing workloads.
Wednesday: someone discovers one affected service is tied to a production API.
Thursday: the app owner says the patch needs testing.
Friday: security asks whether a WAF rule, isolation, or compensating control is already in place.
Google observed XMRig miners deployed within about 48 hours of CVE-2025-55182’s public disclosure in multiple incidents. The same report recommends moving toward automated defenses, including virtual patching targets under 24 hours and full remediation under 72 hours.
That is the argument.
A control review that runs once a quarter cannot govern a threat window measured in days. A 2026-ready framework needs continuous asset discovery, exposure context, vulnerability prioritization, emergency routing, compensating controls, exception approval, fix verification, and evidence capture.
Otherwise, cloud security becomes a race between the attacker and whoever happens to notice first. And that is not a strategy.
The 7 most important cloud security frameworks compared
Choosing between cloud security frameworks is a little like walking into a security review with seven people speaking seven versions of the truth.
- The CISO wants governance.
- The cloud architect wants implementable controls.
- The auditor wants evidence.
- Procurement wants a report.
- Engineering wants to know which rule blocks the release.
Nobody is wrong. They are just solving different parts of the same cloud security problem.
That is why mature teams rarely “pick one framework.” They build a mapped control model: one governance layer for risk, one technical baseline for hardening, one assurance layer for customers or regulators, and cloud-specific checks underneath.
| Framework | Best for | Mandatory? | Cloud-specific? | Effort to implement |
|---|---|---|---|---|
| NIST CSF 2.0 | Enterprise cyber risk governance | Usually no | No, but cloud-ready | Medium |
| CIS Controls v8 + CIS Benchmarks | Technical hardening and prioritized operations | No | Benchmarks can be cloud-specific | Low to high |
| ISO/IEC 27017 and 27018 | Cloud security and cloud privacy assurance | Voluntary, often buyer-driven | Yes | Medium to high |
| CSA CCM v4 / v4.1 | Cloud-native control mapping | No, unless required by contract or CSA STAR | Yes | Medium |
| FedRAMP and StateRAMP / GovRAMP | Public sector cloud authorization | Yes for covered government work | Yes | Very high |
| SOC 2 Type I / Type II | SaaS buyer trust and vendor assurance | Not legal, but often commercially required | No, but common for cloud services | Medium to high |
| PCI DSS 4.0 / 4.0.1 | Cardholder data environments | Yes if cardholder data is involved | Not cloud-only, but cloud-applicable | High |
NIST Cybersecurity Framework 2.0
NIST CSF 2.0 is the one you use when the board asks, “Do we understand our cyber risk?” It organizes security outcomes across Govern, Identify, Protect, Detect, Respond, and Recover. The big 2.0 move is "Govern," which makes it a natural anchor for a cloud security governance framework: policy, accountability, risk appetite, oversight, and decision rights finally sit in the model instead of floating above it.
NIST says Govern establishes and monitors cybersecurity risk management strategy, expectations, and policy.
Who needs it? Security leaders, risk teams, and cloud governance owners.
Cloud controls: asset inventory, risk prioritization, identity governance, third-party risk, incident response, resilience.
Common pitfall: using it as a checkbox list. NIST CSF tells you what outcomes matter. Your cloud platform still has to translate them into enforceable AWS, Azure, GCP, Kubernetes, and on-prem controls.
CIS Critical Security Controls v8 + CIS Benchmarks
CIS is where the conversation stops being “improve security posture” and starts sounding like work.
There are two pieces. CIS Controls v8 gives prioritized cyber defense actions. CIS Benchmarks give secure configuration guidance for specific technologies, including cloud platforms, operating systems, Kubernetes, databases, and network devices.
CIS also uses Implementation Groups:
- IG1 for essential cyber hygiene,
- IG2 for more mature teams with higher risk,
- and IG3 for organizations facing advanced threats or stricter requirements.
Who uses it? Platform engineering, DevSecOps, cloud security, infrastructure, and teams that need technical baselines fast.
Cloud controls: MFA, logging, secure configuration, vulnerability management, inventory, access control, continuous monitoring.
Watch the trap: CIS Benchmarks can become dangerous when applied without context. A public-facing payment workload and a short-lived sandbox do not deserve the same operating treatment.
Read also: Cloud Security Best Practices: Strategy, Checklist, Monitoring, and Automation
ISO/IEC 27017 and ISO/IEC 27018
ISO 27017 and 27018 are for the moment when “we are ISO 27001 certified” is not enough.
ISO/IEC 27017 extends ISO security guidance into cloud service environments. It helps clarify cloud-specific responsibilities between provider and customer.
ISO/IEC 27018 focuses on protecting personally identifiable information in public cloud services, especially when the cloud provider acts as a PII processor.
Who should care? SaaS vendors, cloud service providers, enterprise security teams, privacy teams, and procurement-heavy organizations.
Cloud controls include tenant separation, cloud admin operations, monitoring, secure deletion, data return, customer responsibilities, and PII handling.
Common pitfall: assuming ISO 27001 alone proves cloud maturity. It proves the management system. You still need cloud-specific scope, shared responsibility clarity, and evidence tied to actual services.
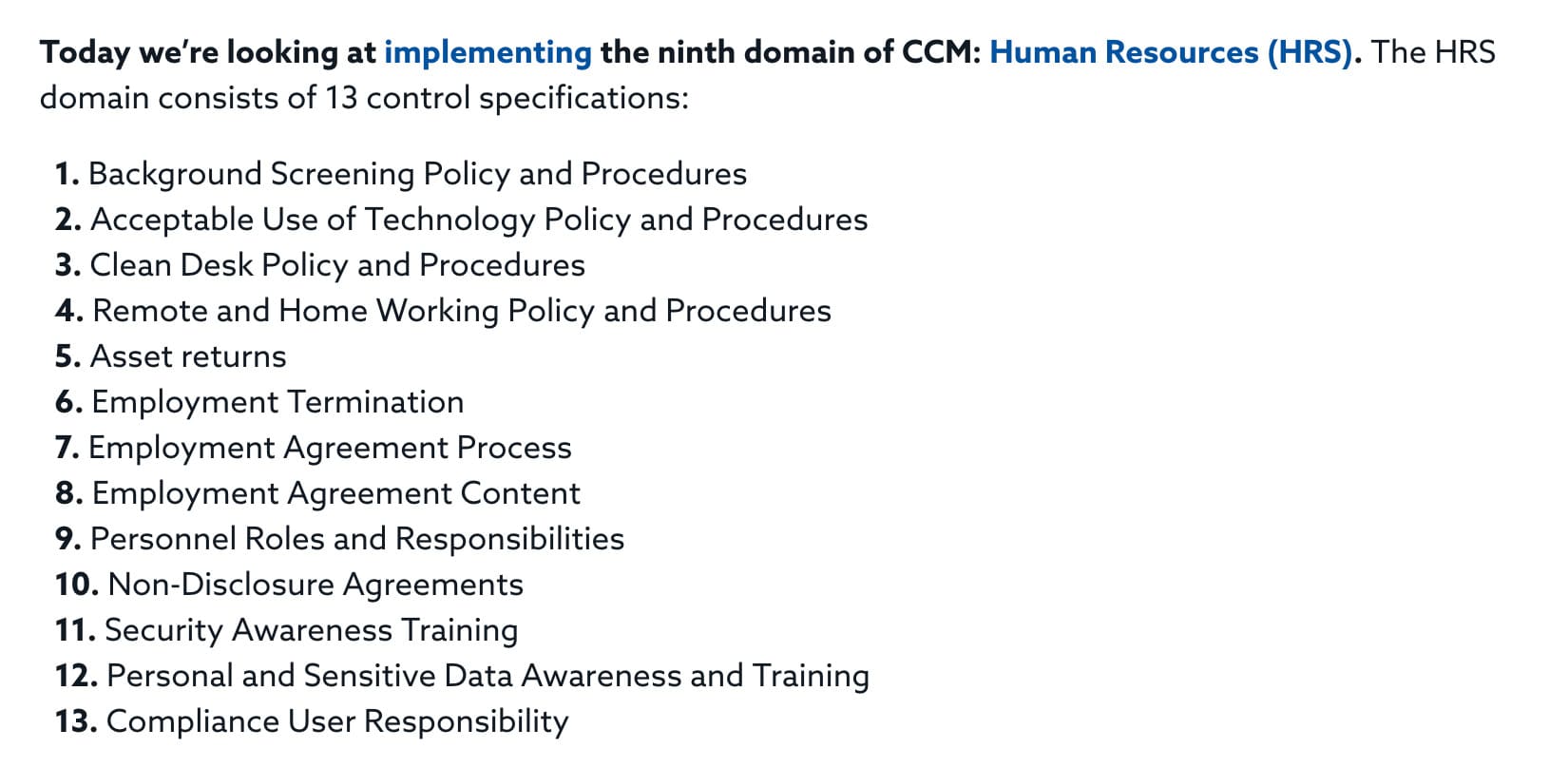
CSA Cloud Controls Matrix v4 / v4.1
If NIST is the governance map, CSA CCM is the cloud-native control library you bring into the war room.
The Cloud Security Alliance describes CCM as a cybersecurity control framework for cloud computing, structured across 17 domains with 197 control objectives. Its newer v4.1 materials also connect CCM with practical guidance for the shared responsibility model, which matters because cloud failures often begin with “we thought the provider handled that.”
Who uses it? Cloud providers, cloud customers, auditors, GRC teams, security architects, and organizations preparing for CSA STAR.
Cloud controls span IAM, encryption, infrastructure security, application security, data governance, logging, supply chain, vulnerability management, and interoperability.
The usual mistake: turning CCM into a spreadsheet nobody operates. Its value shows up when every control maps to an asset, service owner, cloud account, evidence source, and remediation path.
Read also: How to Conduct a Cloud Security Assessment [A Step-by-Step Guide]
FedRAMP and StateRAMP / GovRAMP cloud security framework
This one is not casual compliance.
FedRAMP is the authorization gate for cloud services used by U.S. federal agencies. GovRAMP, formerly StateRAMP, serves a similar assurance role for state, local, education, and related government buyers.
Both are built around NIST 800-53 style control rigor, third-party assessment, authorization status, and continuous monitoring expectations.
FedRAMP’s own continuous monitoring guidance says cloud service providers are responsible for implementing, maintaining, monitoring, and reporting on the controls documented in their System Security Plan.
Who must use it? Cloud providers selling into covered public-sector environments.
Cloud controls: vulnerability scanning, POA&M management, incident response, encryption, boundary protection, access control, configuration management, logging, and continuous evidence.
Pitfall: budgeting for paperwork, then discovering the operational lift. FedRAMP changes engineering cadence, support processes, vulnerability response, evidence collection, and release governance.
SOC 2 Type I / Type II
SOC 2 is the framework that your SaaS buyer requests immediately after they express interest in the demo.
It is not cloud-specific, but cloud companies live inside it because enterprise buyers want assurance around customer data. SOC 2 reports evaluate controls relevant to Security, Availability, Processing Integrity, Confidentiality, and Privacy.
- Type I checks whether controls are designed properly at a point in time.
- Type II tests whether they actually operate over a review period.
Who needs it? SaaS companies, data platforms, API providers, cloud service vendors, and any technology company selling into enterprise procurement.
Cloud controls often include access reviews, change management, encryption, monitoring, incident response, vendor risk, backups, and availability.
Common pitfall: treating SOC 2 like an audit sprint. Type II rewards boring consistency: approved changes, reviewed access, closed tickets, handled alerts, retained evidence.
PCI DSS 4.0 / 4.0.1
PCI DSS enters the room when cardholder data does.
If your cloud environment stores, processes, or transmits payment account data, PCI scope becomes a design problem, not only a compliance one.
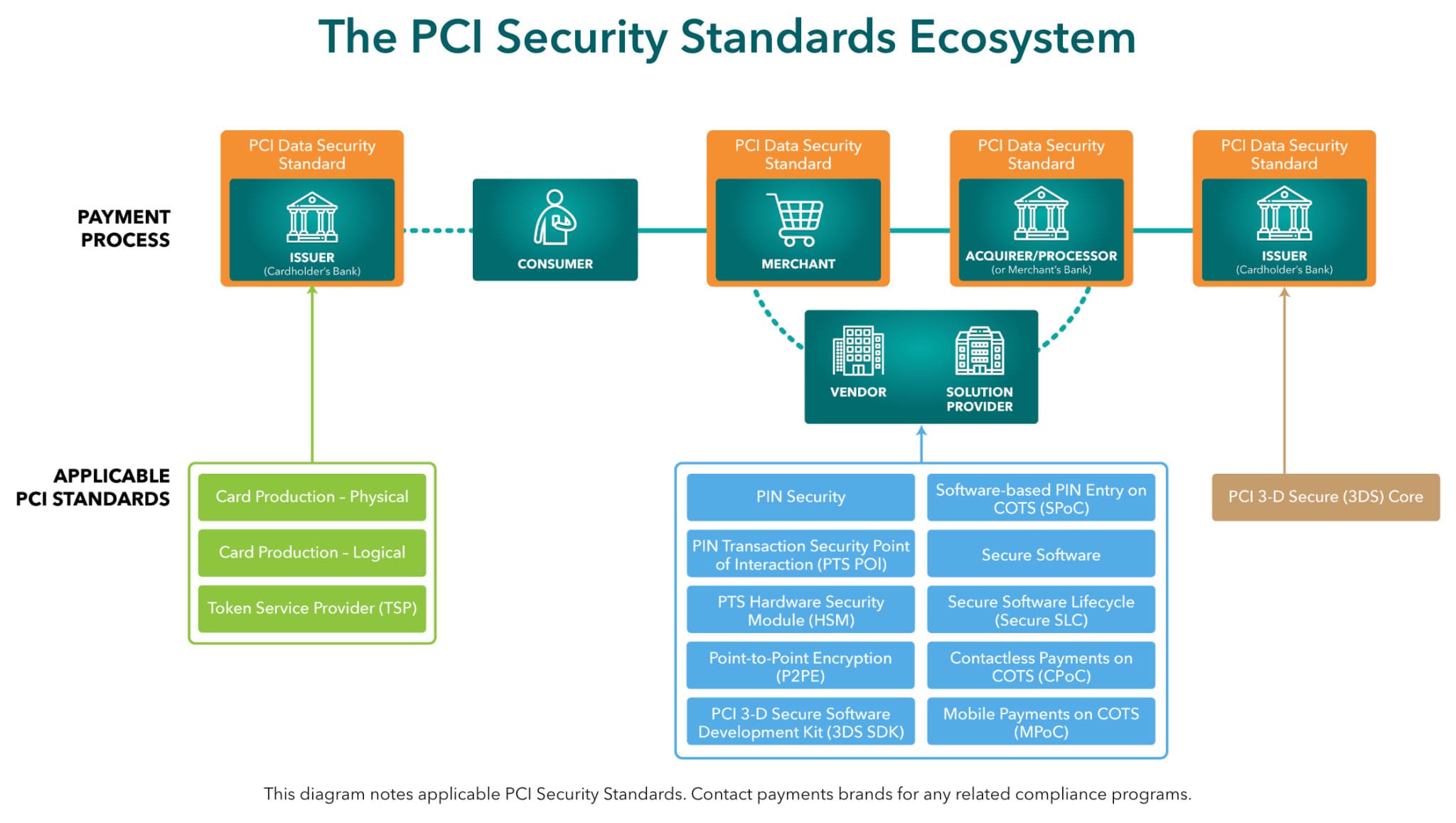
PCI DSS v4.x keeps the core payment-security requirements but adds more flexibility through targeted risk analysis and customized approaches, which sounds nice until you realize flexibility means stronger justification and better proof.
Who must use it? Merchants, payment processors, SaaS platforms in the payment flow, service providers, and any team touching cardholder data environments.
Cloud controls: segmentation, strong authentication, encryption, logging, vulnerability management, secure development, restricted access, and continuous testing.
The pitfall is scope. Too wide, and the program becomes painful. If it's too loose, you miss out on real exposure. In cloud, PCI scope lives in network paths, identity boundaries, data flows, connected services, and evidence.
Read also: Hybrid Cloud Security Architecture - Reference Architecture, Diagram, and Best Practices
How to choose a cloud security framework
The wrong way to choose a cloud security framework is to begin with the framework itself.
Sounds backwards, I know. But cloud teams do this all the time. Someone says, “We should align with NIST.” Another person says, “Buyers keep asking for SOC 2.” Compliance wants ISO. The payment team suddenly remembers PCI DSS. Then the cloud architect, who has been quietly watching AWS, Azure, GCP, Kubernetes, and on-prem drift in five directions, asks the better question:
Which requirement can actually block the business?
Start there.
If a regulator can stop the launch, lead with the regulatory framework. If enterprise buyers can delay deals, prioritize the assurance framework. If the real problem is cloud sprawl, identity drift, and control inconsistency across providers, use a governance spine first, then map technical controls underneath it.
That is the filter. Not “Which standard sounds most mature?” More like: Which one helps us make a decision on Monday morning when the finding is live, the auditor is asking, and the app owner wants proof this is really their problem?
1. Find the pressure source
Every company has one. Sometimes several.
A SaaS company selling into enterprise accounts usually feels buyer pressure first. SOC 2 Type II becomes the trust ticket. ISO 27001 adds credibility. ISO 27017 helps when buyers ask cloud-specific questions about shared responsibility, admin operations, tenant separation, and provider controls.
A payment platform has less freedom. If cardholder data is stored, processed, or transmitted, PCI DSS sits at the center. The design conversation becomes sharper: segmentation, encryption, logging, access restrictions, vulnerability management, secure development, and evidence around the cardholder data environment.
A cloud provider selling to U.S. federal agencies has a different reality again. FedRAMP is not an accessory. It changes the operating model: NIST 800-53 controls, continuous monitoring, POA&Ms, vulnerability scanning, incident response, change control, and ongoing evidence.
No hard compliance pressure yet? Lucky you. Use that time well. NIST CSF 2.0 gives you the governance spine, especially with the Govern function. CIS Controls IG1 gives the team a sane technical starting point before the cloud estate grows teeth.
2. Then check whether the framework can survive your architecture
This is where a lot of programs get exposed. A framework can look clean in a slide and fall apart inside the estate.
Ask:
- Can it handle AWS accounts, Azure subscriptions, GCP projects, Kubernetes clusters, SaaS apps, and on-prem systems?
- Does it separate control intent from provider-specific implementation?
- Can one encryption requirement map to S3, Azure Storage, Cloud Storage, databases, snapshots, and backups?
- Does it define who owns exceptions?
- Can it produce evidence without turning compliance into a scavenger hunt?
- Will engineers understand what to fix?
If the answer is no, you may still have a useful standard. You just do not have an operating model yet.
That is why multi-cloud teams often need CSA CCM as a cross-walk. It gives cloud-native control structure, especially around shared responsibility. Not because it replaces NIST, CIS, SOC 2, ISO, or PCI. It helps translate between them when one workload touches three providers and two accountability models.
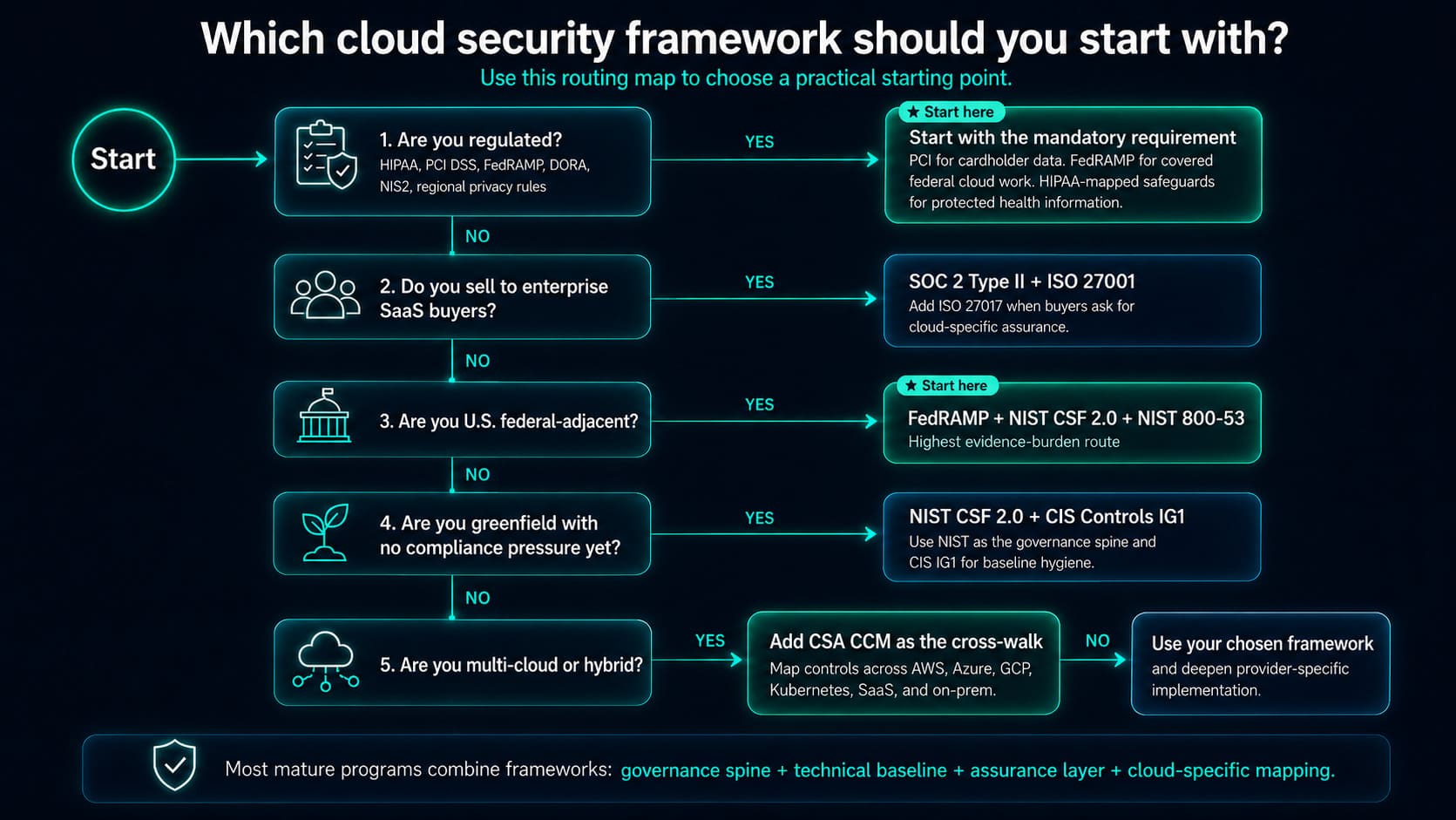
Most cloud teams should not choose one framework and call it done. A stronger model looks like this:
- Use NIST CSF 2.0 to organize governance and risk ownership.
- Add CIS Controls and CIS Benchmarks so platform and DevSecOps teams have concrete hardening guidance.
- Bring in CSA CCM when multi-cloud mapping gets messy.
- Layer SOC 2, ISO 27017, PCI DSS, FedRAMP, or HIPAA-mapped controls when buyers, regulators, or markets require proof.
That is how cloud security frameworks become useful. Not as competing documents. As one control system that tells the same story from executive risk to cloud configuration to audit evidence.
Cloud security governance framework
A cloud security governance framework defines who decides, who executes, and who verifies security controls across your cloud estate.
That sentence sounds calm. The real cloud estate is not.
One team owns the AWS account. Another owns the Azure subscription. GCP was opened for analytics and somehow became production-adjacent. Kubernetes moves faster than the approval board. On-prem identity still feeds access. Compliance asks for evidence from six months ago.
Governance is the part that stops everyone from saying, “I thought security owned that.”
The 4 pillars of cloud security governance: SPRC
- Use the SPRC model: Strategy, Policy, Risk, Compliance. Simple enough to remember. Serious enough to run a hybrid cloud program.
- Strategy sets the risk line. This is where leadership decides what matters most. Customer PII in production? Zero tolerance for public exposure. Missing tags in a dev sandbox? Fix it, but do not wake up the CISO. Strategy defines approved providers, critical services, risk appetite, escalation paths, and remediation expectations. Without it, every alert fights for the same oxygen.
- Policy turns intent into rules engineers can follow. A useful policy does not say “secure access.” It says privileged cloud roles need MFA, named ownership, quarterly review, and exception expiry. Public storage is blocked by default. Production encryption uses approved key management. Internet-facing workloads need logging. A RACI belongs here because cloud teams need clean lines between security, platform, app owners, compliance, and the control owner.
- Risk keeps the register connected to reality. A risk register should not be a graveyard of vague statements. In cloud, it should connect to assets, accounts, subscriptions, projects, environments, vulnerabilities, misconfigurations, owners, and business services. A broad IAM role on a production payment workload is not the same risk as a weak tag on a test VM.
- Compliance proves the control actually worked. Auditors do not need poetry. They need timestamps, approval history, change records, ticket links, exception status, scan results, and current configuration evidence.
That is the job: decision, rule, risk, proof. Not governance theater. Actual control ownership.
Read also: Cloud workload security - A cross-cloud guide for 2026
Roles and RACI for cloud security governance
A RACI table looks boring until a production control fails at 4:40 PM on a Thursday.
Then it becomes very interesting.
An AWS IAM role has admin-like permissions. An Azure Storage Account allows public network access. A GCP project has logging disabled. The finding is high severity. The control maps to SOC 2, ISO 27017, and maybe PCI DSS if payment data is nearby.
Now comes the real question.
Who decides whether this is acceptable risk?
Who changes the configuration?
Who owns the guardrail so it does not happen again?
Who keeps the evidence?
Who checks that the process actually worked?
That is why RACI matters in cloud security frameworks. Not as a corporate artifact. As the routing layer between risk, engineering, compliance, and audit.
Quick reminder:
- Responsible: does the work.
- Accountable: owns the outcome.
- Consulted: gives input before action.
- Informed: needs visibility, but does not drive the task.
Here is the simple working version.
| Cloud security governance activity | CISO | Cloud Platform Lead | Cloud Engineer | GRC | Internal Audit |
|---|---|---|---|---|---|
| Set cloud security strategy and risk appetite | A | C | I | C | I |
| Approve framework and control baseline | A | R | C | R | C |
| Translate controls into AWS, Azure, GCP, Kubernetes, and on-prem checks | C | A | R | C | I |
| Build preventive guardrails | I | A | R | C | I |
| Fix failed technical controls | I | A | R | C | I |
| Approve exceptions and risk acceptance | A | C | C | R | I |
| Maintain audit evidence and control history | I | C | C | A/R | C |
| Test whether governance works as designed | I | C | I | C | A/R |
The table is not the point, though. The handoff is.
Say production storage is exposed. The cloud engineer changes the setting. The cloud platform lead updates the guardrail or Terraform module. GRC confirms which control failed and stores the evidence: finding timestamp, affected asset, owner, change ticket, approval trail, and post-fix scan. The CISO decides whether any exception is acceptable. Internal audit later checks the pattern, not just the one fix.
That is the whole game.
Cloud governance does not need more people in meetings. It needs fewer orphaned decisions. A good RACI makes every failed control move somewhere useful: to an owner, to a fix, to an exception, or to evidence.
Governance metrics that actually matter
The RACI table gave every control a route. Now governance needs a speedometer.
Because “CISO accountable, engineer responsible, GRC consulted” sounds fine until a critical public-storage finding sits open for 19 days because nobody knows whether the app is production, whether the data is regulated, or whether the exception from last quarter still applies.
That is the gap metrics should expose.
A cloud security framework is only useful if it shows where risk moves, where it stalls, and where proof is missing. Counting findings is the easy part. Measuring governance health is harder.
Start with guardrail coverage
The first number I’d want on the dashboard is simple: What percentage of cloud accounts are actually under baseline guardrails?
Not “known.”
Not “scanned.”
Under guardrails.
Say the estate has 240 AWS accounts, Azure subscriptions, and GCP projects. If 198 enforce baseline controls, coverage is 82.5%. That missing 17.5% is where the story begins.
Are those accounts from an acquisition? New dev sandboxes? Analytics projects? Shadow environments? Production-adjacent workloads with weak tags?
Track guardrail coverage by provider, environment, business unit, and criticality. Production should be boringly close to 100%. Anything connected to regulated data should be treated like a live wire.
Read also: Inside the DevSecOps Lifecycle - Decisions, Gates, and Evidence
Then watch MTTR for critical misconfigurations
Mean time to remediation tells you whether ownership leads to action. A critical misconfiguration is not closed when Jira gets a ticket. It is closed when the fix is applied, verified, and attached to evidence.
Good examples to track:
- public storage touching sensitive data
- admin-level IAM without approval
- exposed SSH or RDP
- disabled production logging
- unencrypted regulated datastore
- internet-facing workload with a critical vulnerability
If MTTR stays high, the engineer may not be the bottleneck. The delay might be missing asset ownership, no approved fix pattern, unclear severity, or GRC asking for proof after the work is already done.
Evidence automation is the audit stress test
Manual evidence collection looks manageable until SOC 2, ISO 27017, PCI DSS, internal audit, and a customer security review land in the same quarter.
Then the team starts archaeology. Screenshots. Ticket links. Slack messages. Old scan exports. Someone asking, “Was encryption enabled before or after the audit window?”
Measure the percentage of controls with automated evidence: configuration state, asset record, owner assignment, change history, approval trail, remediation ticket, exception status, and post-fix verification timestamp.
Start with IAM, encryption, logging, public exposure, vulnerability remediation, and production change approvals. Those controls create the most pain when proof is manual.
Finally, measure the framework coverage gap
This is the “are we kidding ourselves?” metric. Take the frameworks you claim to follow: NIST CSF 2.0, CIS Benchmarks, CSA CCM, SOC 2, ISO 27017, PCI DSS, FedRAMP. Now check whether each control maps to real assets, owners, environments, and evidence.
A coverage gap appears when the control exists in the framework but not in operations.
Example: CSA CCM expects shared responsibility clarity. Good. Can your team prove who owns encryption keys across AWS KMS, Azure Key Vault, and Google Cloud KMS? Can they show backup ownership, logging retention, access review status, and exception approval for each production workload?
If not, the gap is not theoretical.
It is sitting in the estate.
Good governance metrics make risk harder to hide. They show the unguarded account, the slow fix, the manual evidence trail, and the control that never made it from framework language into cloud reality.
Cloud security framework for AWS
An AWS cloud security framework combines the AWS Well-Architected Security Pillar with an external standard, such as NIST CSF or CIS, to produce auditable, AWS-specific controls.
That matters because AWS already gives you strong native building blocks. The hard part is turning them into a control system that your security team, platform engineers, GRC, and audit can all interpret in the same way.
AWS Well-Architected gives the architecture lens. NIST CSF gives governance outcomes. CIS adds hardening discipline. Your internal policies decide what is mandatory for production, regulated data, internet-facing workloads, and exceptions.
The phrase cloud security framework AWS sounds like one thing. In practice, it is a stack.
AWS Well-Architected Security Pillar: the 7 design principles
AWS frames the Security Pillar around protecting data, systems, and assets in ways that use cloud capabilities to improve security. Its seven design principles are a useful starting point because they read like the checklist every cloud team wishes had existed before the first 80 AWS accounts appeared.
AWS lists them as:
implement a strong identity foundation,
- enable traceability,
- apply security at all layers,
- automate security best practices,
- protect data in transit and at rest,
- keep people away from data,
- and prepare for security events.
The translation is pretty direct.
Identity means IAM, IAM Identity Center, SCPs, permission boundaries, and short-lived access. Traceability means CloudTrail, Config, Security Hub, GuardDuty, and log retention that survives account sprawl. “Keep people away from data” is the grown-up version of “stop using humans as production data processors.” Use automation, tokenization, scoped access, and controlled workflows instead.
Mapping NIST CSF and CIS Controls to AWS native services
| Control family | AWS-native services to start with |
|---|---|
| Identify | AWS Config + AWS Resource Explorer |
| Protect | IAM, KMS, GuardDuty |
| Detect | CloudTrail, Security Hub |
| Respond | Amazon Detective, Systems Manager Incident Manager |
AWS Config helps assess, audit, and evaluate resource configurations, while Resource Explorer helps teams search and discover resources across accounts and Regions using metadata such as names, tags, and IDs.
CloudTrail records user and API activity, and Security Hub brings together signals from AWS security services to give teams a broader security and compliance view.
Incident Manager helps coordinate response plans, escalations, runbooks, and post-incident analysis when something critical breaks.
2 AWS cloud security framework best practices
1. Design AWS guardrails at the organization layer, then let risk decide the account pattern
Account-by-account security sounds manageable until the estate has 80 accounts, 12 business units, three inherited environments from acquisitions, and a few “temporary” sandboxes that now touch production data.
Start with AWS Organizations as the control boundary. Use Service Control Policies, centralized logging, mandatory CloudTrail, AWS Config aggregation, approved Regions, public-access restrictions, encryption defaults, and baseline tagging before individual teams start building.
Then split the estate by risk.
Production should not live under the same control assumptions as experimentation. Regulated workloads should have cleaner account separation, tighter IAM boundaries, stricter change control, and a shorter exception leash. Shared services accounts need special handling because one weak permission there can ripple across the entire estate.
The useful test is simple: Can a new AWS account inherit the right logging, identity, encryption, network, and evidence rules on day one?
If not, the framework depends on memory. And memory is not a control.
2. Make every AWS finding tell a complete control story
A failed check is not enough. “Security Hub finding failed” does not help a platform team prioritize. “S3 bucket public” is better, but still incomplete. A useful AWS cloud security framework should turn that signal into a control story:
- Asset: s3-prod-customer-exports-eu
- Environment: production
- Application: customer analytics export
- Owner: data platform team
- Control: CIS storage public access / NIST Protect data security
- Risk: sensitive customer export exposed to public access
- Change: bucket policy modified by CI/CD role 6 hours ago
- Action: block public access, review pipeline permission, attach evidence
- Proof: updated config state, change ticket, post-fix scan, approval record
That is the difference.
AWS services can surface the signal. The framework has to connect it to ownership, severity, business context, remediation, and evidence.
Without that chain, the team has alerts. With it, they have work that can actually move.
Read also: 9 AWS Cloud Security Best Practices. A Practitioner’s Guide to Securing Your Cloud
Cloud security framework for Azure
An Azure cloud security framework typically anchors on the Microsoft Cloud Adoption Framework (CAF) Secure methodology and the Azure Security Benchmark, mapped to NIST CSF or ISO 27001.
That is the clean version.
- The real version starts when a company has 40 Azure subscriptions;
- Management groups built three reorganizations ago;
- A few production workloads sitting beside “temporary” analytics projects;
- And security findings split across Defender for Cloud, Sentinel, Azure Policy, Entra ID, and someone’s spreadsheet.
- Azure gives you the ingredients. The framework tells the team how to turn them into controls with owners, guardrails, evidence, and repeatable decisions.
Microsoft cloud adoption framework: secure methodology
Microsoft CAF Secure is useful because it treats security as an operating discipline, not a late-stage audit patch. In Azure landing zone design, Microsoft says security should be considered throughout the process, with the design area creating a foundation across Azure, hybrid, and multicloud environments.
It also points teams toward CAF Secure for deeper security process and tooling guidance.
The six Secure disciplines give cloud leaders a practical shape:
- Access control: Microsoft Entra ID, Conditional Access, PIM, RBAC, managed identities, least privilege.
- Modern security operations: Microsoft Defender for Cloud, Sentinel, alert routing, incident response, detection engineering.
- Infrastructure security: VNets, NSGs, private endpoints, Azure Firewall, DDoS protection, segmentation.
- Dev security: secure pipelines, IaC checks, secrets management, workload identity, release controls.
- Data security: Key Vault, encryption, data classification, storage access, database auditing.
- Asset protection: subscription hygiene, tagging, inventory, vulnerability context, backup protection.
The trap is treating CAF as an “Azure best practices.” It is more useful as the operating model for who governs what.
Microsoft сloud security benchmark (MCSB)
Here is the naming detail teams miss: Microsoft Cloud Security Benchmark is the successor to Azure Security Benchmark. Microsoft renamed ASB to MCSB in October 2022 and expanded the direction toward a broader cloud security control framework aligned with standards such as CIS, NIST, and PCI.
Why does that matter?
Because MCSB helps translate familiar control language into Azure-specific implementation guidance. Microsoft’s MCSB v2 maps controls to NIST SP 800-53 Rev. 5, PCI DSS v4, CIS Controls v8.1, NIST CSF v2.0, ISO 27001:2022, and SOC 2, while warning that those mappings show partial or full technical coverage, not automatic compliance.
That last bit is important.
An Azure Policy assignment can support a PCI or NIST control. It does not magically prove the whole control is compliant. You still need scope, ownership, review, exceptions, and evidence.
Mapping framework controls to Azure native services
A practical cloud security framework for Azure should not say “use Microsoft security tools” and stop there. It should answer what each tool is supposed to prove.
| Control family | Azure-native services to use |
|---|---|
| Governance and posture | Azure Policy, Microsoft Defender for Cloud |
| Identity and access | Microsoft Entra ID, Conditional Access, Privileged Identity Management |
| Detection and response | Microsoft Sentinel, Defender for Cloud alerts |
| Data protection | Azure Key Vault, Storage encryption, database auditing |
| Compliance evidence | Defender for Cloud regulatory compliance dashboard, Azure Policy compliance state |
| Network and workload protection | NSGs, Azure Firewall, private endpoints, Defender plans |
Think of it like a control chain. Azure Policy says whether the configuration matches the rule. Defender for Cloud adds security recommendations and risk context. Entra ID and Conditional Access explain who can do what. Sentinel turns telemetry into investigation and response. Key Vault proves key control, but only if ownership, rotation, access, and audit logs are part of the evidence story.
A finding without that chain is just a signal. Useful, but incomplete.
Azure Landing Zone as a framework foundation
Azure Landing Zones are the point at which the framework transitions from theory to practical application.
Microsoft recommends planning subscription policies before creating subscriptions, using management groups to govern at scale, enforcing governance with Azure Policy, and separating production, nonproduction, and sandbox environments into different subscriptions.
That is the part cloud architects should care about.
Subscription vending gives workload teams speed without handing them a blank cloud. Management groups create inheritance. Azure Policy applies guardrails before teams drift. Separate landing zones keep production, dev/test, and sandbox from sharing the same risk profile.
One practical example:
A new application team requests a subscription. The platform team vends it under the right management group. Azure Policy applies required logging, allowed regions, tagging, private endpoint rules, and Defender coverage. Entra groups and RBAC are assigned at the proper scope. Security can see the workload. GRC can map controls. Engineering can build without negotiating every guardrail from scratch.
Read also: Azure Cloud Security Best Practices (A Practical Guide for Secure Environments)
Cloud security framework for SaaS
A cloud security framework for SaaS has to deal with the cloud you do not fully control.
That is the uncomfortable part.
In AWS, Azure, or GCP, your team can usually chase the risk back to a resource: an instance, a bucket, a subnet, a policy, a key. SaaS is different. The asset might be a Workday tenant, a Salesforce integration, a Slack workspace, a Google Workspace OAuth grant, a Rippling admin role, or a Notion page synced through a third-party app that nobody remembers approving.
The control plane is not only the SaaS app.
It is the identity provider. SCIM. OAuth. Admin roles. API tokens. Vendor settings. Audit logs. Data exports. Browser sessions. Contractor access. External sharing.
That is why SaaS needs its own framework lens.
Why SaaS needs its own framework lens
SaaS risk rarely arrives with flashing lights. It usually arrives through convenience.
A team signs up for a tool. Someone connects SSO. Someone else approves OAuth access because the integration needs to “read calendar data.” SCIM provisioning gets enabled, but deprovisioning is only half-configured. Admins are added during setup.
Six months later, the app contains customer exports, employee records, contracts, support tickets, billing details, source snippets, and compliance evidence.
At that point, “shadow IT” is not the full story.
The better word is shadow access.
SSPM, or SaaS Security Posture Management, helps because SaaS has a different control surface:
- OAuth grants with broad read/write permissions
- local users bypassing SSO
- dormant admins after team changes
- missing SCIM deprovisioning
- external sharing across files, channels, boards, or records
- audit logs that are not exported into the security evidence trail
- API tokens with no owner or expiry
- SaaS apps connected to the identity provider but not reviewed by security
Frameworks most relevant to SaaS
Not every standard sees SaaS clearly.
- SOC 2 usually comes first for SaaS companies because enterprise buyers understand it. They want to know whether your controls around security, availability, confidentiality, processing integrity, and privacy actually operate over time.
- ISO 27001 gives the management-system layer. ISO 27017 adds cloud-specific guidance, which helps when control ownership is split between the SaaS provider and the customer.
- CSA CCM is stronger when the estate gets cloudy in the modern way: SaaS connected to IaaS, identity, APIs, data pipelines, and third-party vendors.
- NIST CSF gives leadership the operating model. Govern. Identify. Protect. Detect. Respond. Recover. Clean enough for executives, flexible enough for security architects.
The practical SaaS control questions are sharper than “Are we compliant?”
Ask this instead:
- Which SaaS apps are approved, tolerated, or blocked?
- Which ones connect to Microsoft Entra ID, Okta, Google Workspace, or another identity provider?
- Where is SCIM enabled, and where does deprovisioning still depend on a human?
- Which OAuth grants can read files, export data, edit records, or manage users?
- Which tenants contain regulated, customer, financial, source-code, or employee data?
- Can audit logs be exported and retained?
- Who owns the integration when the original admin leaves?
HR cloud security framework: protecting Workday, BambooHR, Rippling
An HR cloud security framework is not a separate global standard. It is the SaaS governance lens applied to HR platforms like Workday, BambooHR, Rippling, HiBob, Personio, Deel, Greenhouse, or Lever.
HR SaaS deserves stricter treatment because it often holds the densest PII stack in the company.
Legal names. Home addresses. Salaries. Tax IDs. Bank details. Contracts. Performance notes. Leave records. Benefits. Immigration documents. Emergency contacts. Sometimes health-related information. Sometimes background-check data.
That is not “just another business app.”
For HR SaaS, the baseline should feel tighter:
- SSO enforcement: regular users should not rely on local passwords. Break-glass access needs a named owner, monitoring, and review.
- Role-based access: payroll, HR admins, recruiters, managers, finance, and IT should not inherit broad permissions by convenience.
- SCIM lifecycle control: joiner, mover, leaver workflows need to work cleanly. A terminated employee should not stay active because HR and IT systems missed a sync.
- Audit log export: login events, role changes, employee record edits, data exports, integration activity, and admin actions should leave the vendor portal and enter the evidence trail.
- Data residency and retention: know where employee data is stored, where it is processed, and how long it stays after offboarding.
- Sub-processor review: HR platforms often rely on payroll, benefits, background checks, e-signature, analytics, and support vendors. That chain matters.
- OAuth and API governance: integrations need scoped permissions, named owners, review dates, and removal when the business use case ends.
The final test is simple. Could your team prove who accessed compensation data, which integration exported employee records, whether the user was active, what role allowed access, and which control reviewed that permission?
If not, HR SaaS is not governed yet.
It is trusted.
Those are very different things.
Vendor and provider cloud security standards
Not every useful cloud security framework comes from NIST, ISO, CIS, or CSA.
Sometimes the most practical patterns come from vendors that had to secure large, distributed, highly audited environments before the rest of us had clean names for the mess.
I would not copy a vendor model blindly. Cisco, Google, AWS, and Microsoft have different architectures, teams, telemetry, and risk profiles. But their published frameworks are worth studying because they show how mature cloud security programs behave when theory meets production: controls get mapped, evidence gets reused, identity becomes central, and security moves closer to engineering.
Cisco cloud infrastructure security standards
Cisco’s Cloud Controls Framework is the rare vendor-published enterprise framework that deserves a real look beside NIST CSF and CSA CCM.
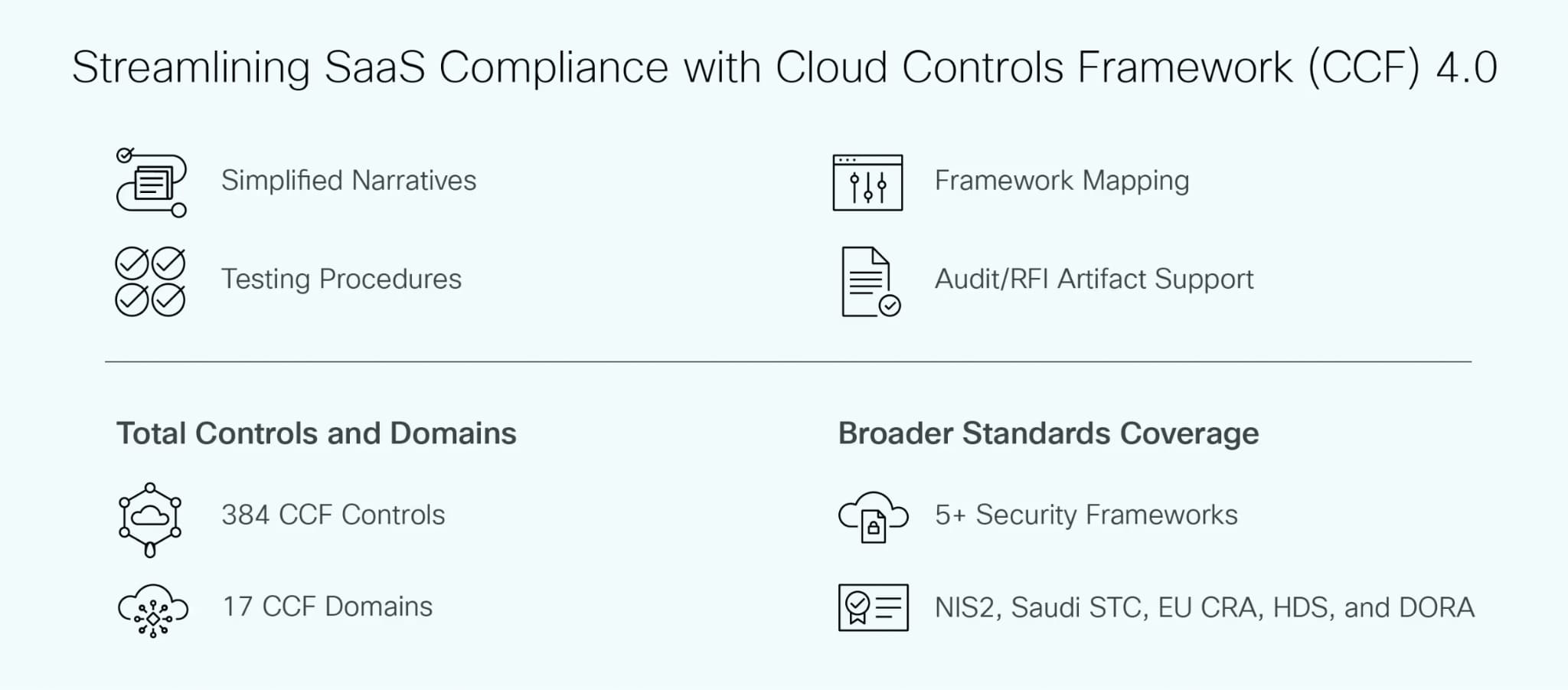
Cisco describes CCF as a consolidated set of international and national security compliance and certification requirements, aggregated into one framework with control mappings, implementation guidance, and audit artifacts.
That is the interesting part - the “build once, map many times” operating pattern.
For cloud security leaders, that pattern is useful because compliance rarely arrives one framework at a time.
SOC 2 asks for evidence. ISO wants control structure. NIST wants risk language. PCI DSS wants scope discipline. DORA, NIS2, and regional requirements add more pressure. A control like privileged access review should not become seven separate rituals. It should become one governed control with one owner, one workflow, one evidence trail, and multiple mappings.
Cisco’s broader cloud security reference story also touches two practical areas:
- Secure Workload focuses on workload visibility and policy enforcement across hybrid and multicloud environments, including bare metal, virtualized, cloud-based, and container-based workloads.
- Secure Cloud Insights, now referenced in Cisco materials as Attack Surface Management, was positioned around asset visibility, posture insight, relationship mapping, and compliance risk reduction. Cisco has also published end-of-sale and end-of-support notices, so in 2026 it is safer to treat it as a reference pattern than as a fresh tool recommendation.
The lesson is: Can your cloud security team map one failed control across AWS, Azure, GCP, SaaS, containers, and on-premises without rebuilding the evidence story every time?
A Cloudaware control dashboard shows that exact problem as a working view:
framework control, affected asset, provider, environment, owner, related change, evidence status, and mapped standards in one record. That is the kind of control reuse vendor frameworks are really pointing toward.
Other vendor-published frameworks worth knowing
👉 Google’s BeyondProd is the one to study when your architecture has moved past perimeter comfort.
Google describes BeyondProd as a cloud-native architecture of services and controls that protect workloads, including how code changes happen and how user data is accessed.
The idea is service identity, workload isolation, controlled change, data access boundaries, and security checks closer to production behavior.
That matters for teams running Kubernetes, microservices, service mesh, CI/CD, workload identity, and internal APIs. BeyondProd gives security architects a useful mental model: production trust should be earned by service identity, code provenance, runtime context, and policy enforcement. Not by network location.
👉 SLSA belongs in the supply-chain drawer, but honestly, that drawer is now part of cloud security. SLSA defines a framework of standards and controls to prevent tampering, improve software artifact integrity, and secure packages and infrastructure.
Use it when the weak point is not the cloud resource itself, but the thing being shipped into it: container images, build pipelines, dependencies, artifacts, provenance, and release integrity.
👉 AWS Well-Architected Security Pillar is more workload-design oriented. AWS frames it around design principles such as strong identity foundations, traceability, security at all layers, automation, data protection in transit and at rest, reducing direct human access to data, and preparation for security events.
Great for AWS architecture reviews. It is not enough on its own for enterprise-wide governance.
👉 Microsoft SDL sits closer to the engineering system. Microsoft describes SDL as its approach for integrating security into DevOps, with core phases across requirements, design, implementation, verification, and release.
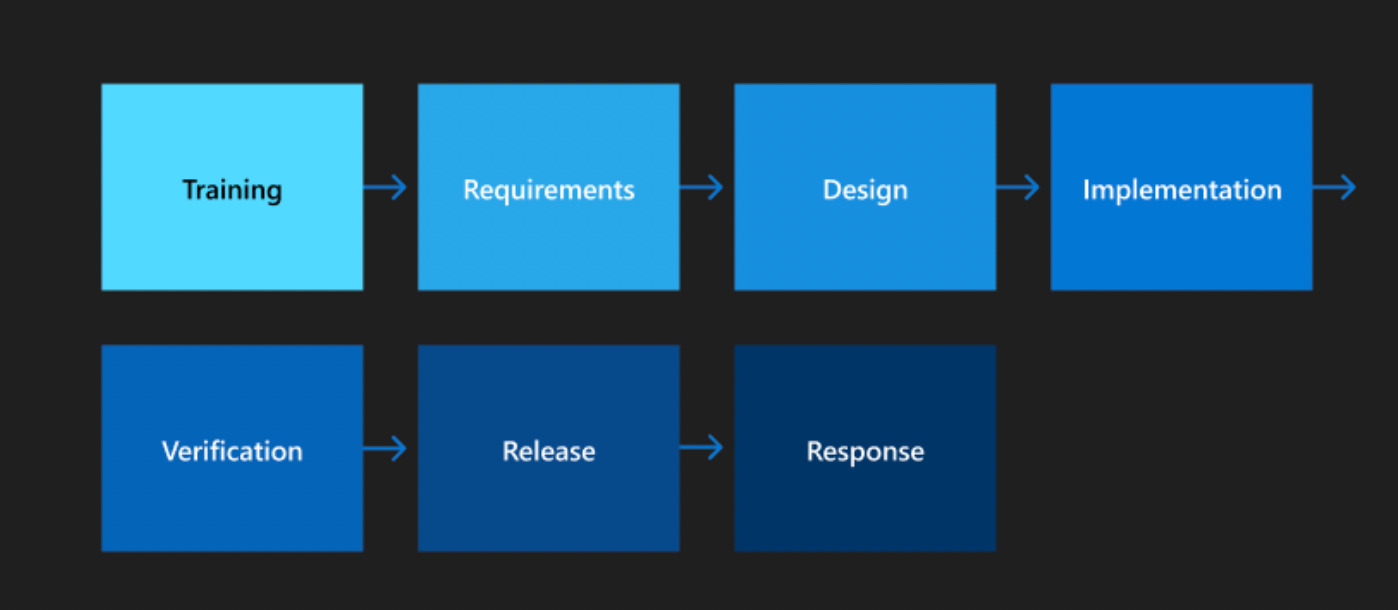
That makes it useful when the cloud risk starts in code, design, dependency choice, threat modeling, or release approval.
How to actually use vendor frameworks
Treat vendor cloud security frameworks as implementation patterns, not compliance replacements.
- Google helps you think about production service trust.
- SLSA gives structure to software supply-chain integrity.
- AWS Well-Architected improves workload security design.
- Microsoft SDL brings security into delivery.
- Cisco CCF shows how one enterprise can consolidate controls and reuse evidence across many obligations.
The practical move is to pull the useful parts into your own control model.
One control library.
Provider-specific checks underneath.
Evidence tied to assets, owners, changes, and exceptions.
No duplicate audit circus every time a buyer, regulator, or internal team asks the same question in different languages.
That is the real value here. Vendor frameworks are not the destination. They are clues from companies that already had to solve pieces of the cloud governance problem at scale.
Turn controls into cloud work with Cloudaware
The challenging part of cloud security frameworks is not finding the controls.
NIST has controls. CIS has controls. ISO, CSA CCM, SOC 2, PCI DSS, HIPAA all have controls.
The hard part is getting those controls to line up with the messy reality of a hybrid estate: AWS accounts, Azure subscriptions, GCP projects, OCI workloads, Kubernetes clusters, SaaS apps, VMware, on-prem dependencies, owners, exceptions, and tickets that may or may not have the full story.
A framework says: protect sensitive data.
The cloud asks back:
Which asset?
Which provider?
Which environment?
Which app?
Which owner?
Which exception?
Which evidence?
Which control family does this satisfy?
Cloudaware is used by cloud security, platform, DevSecOps, GRC, and audit teams that need framework controls to become operational. Not “mapped in a spreadsheet.” Mapped to real assets, real owners, live posture, remediation tickets, and audit-ready evidence.
That is the useful layer: one place where security leaders see governance, engineers see fix context, and compliance teams see proof.
From Framework Language to Cloud Work: How Cloudaware Makes Controls Operable
The hard part of cloud security frameworks is not finding the controls.
NIST has controls. CIS has controls. ISO, CSA CCM, SOC 2, PCI DSS, HIPAA, and internal policy libraries all have controls.
The real problem starts when those controls meet the estate: AWS accounts, Azure subscriptions, GCP projects, Oracle Cloud workloads, Kubernetes clusters, VMware, SaaS tools, on-prem systems, owners, exceptions, tickets, and evidence trails that do not always agree with each other.
A framework says: protect sensitive data.
The cloud asks back:
Which asset?
Which provider?
Which environment?
Which application?
Which owner?
Which exception?
Which evidence?
Which control family does this satisfy?
Cloudaware helps cloud security, platform, DevSecOps, GRC, and audit teams turn framework controls into operational work. Not mapped in a spreadsheet. Mapped to real assets, owners, policy checks, violations, remediation paths, and audit-ready evidence.
That is the useful layer: security leaders see governance, engineers see fix context, and compliance teams see proof.
Cloudaware solutions that help operationalize cloud security frameworks
- Cloudaware CMDB gives teams a continuously updated system of record across hybrid and multi-cloud environments, including AWS, Azure, GCP, Oracle Cloud, Kubernetes, VMware, and on-prem infrastructure. Cloudaware positions the CMDB as the inventory layer that normalizes cloud and non-cloud assets into one operating model.
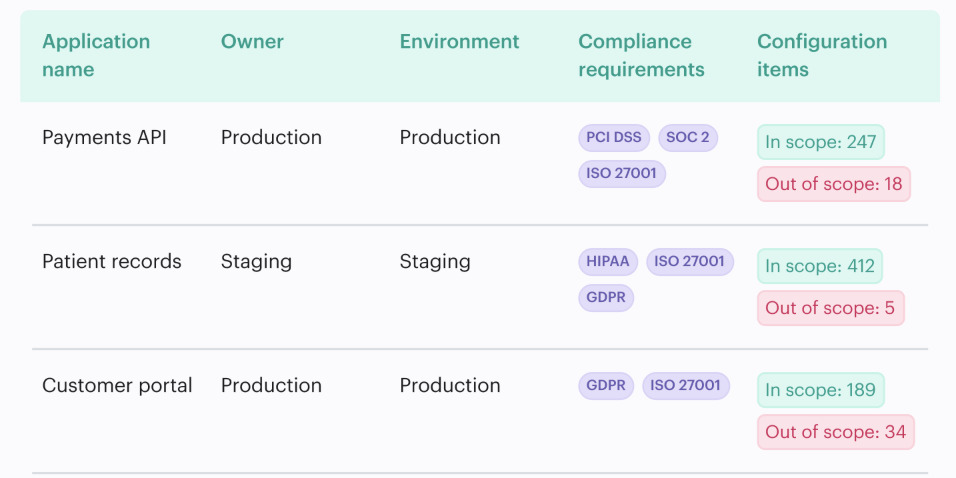
That matters because framework mapping starts with knowing what exists. A NIST, CIS, CSA CCM, SOC 2, PCI DSS, or ISO control cannot be enforced cleanly if the team cannot see which accounts, workloads, databases, identities, storage resources, tags, owners, and environments are in scope. - Cloudaware IT Compliance is the core module for turning framework requirements into compliance-as-code. It evaluates policies against CMDB data, transforms failed checks into trackable violations, supports time-boxed exceptions, and links assets and controls back to the CMDB with pass/fail status, ownership, gaps, run history, and evidence.
A failed control should not say only “noncompliant.” It should show the affected asset, environment, owner, policy result, exception status, remediation lifecycle, and evidence trail. - Control mappings across security standards and internal policies. Cloudaware’s compliance engine documentation describes policies based on standards such as PCI, HIPAA, NIST, ISO, GDPR, and CIS Benchmarks for AWS, Azure, and GCP, plus custom policies that can evaluate any CMDB data.
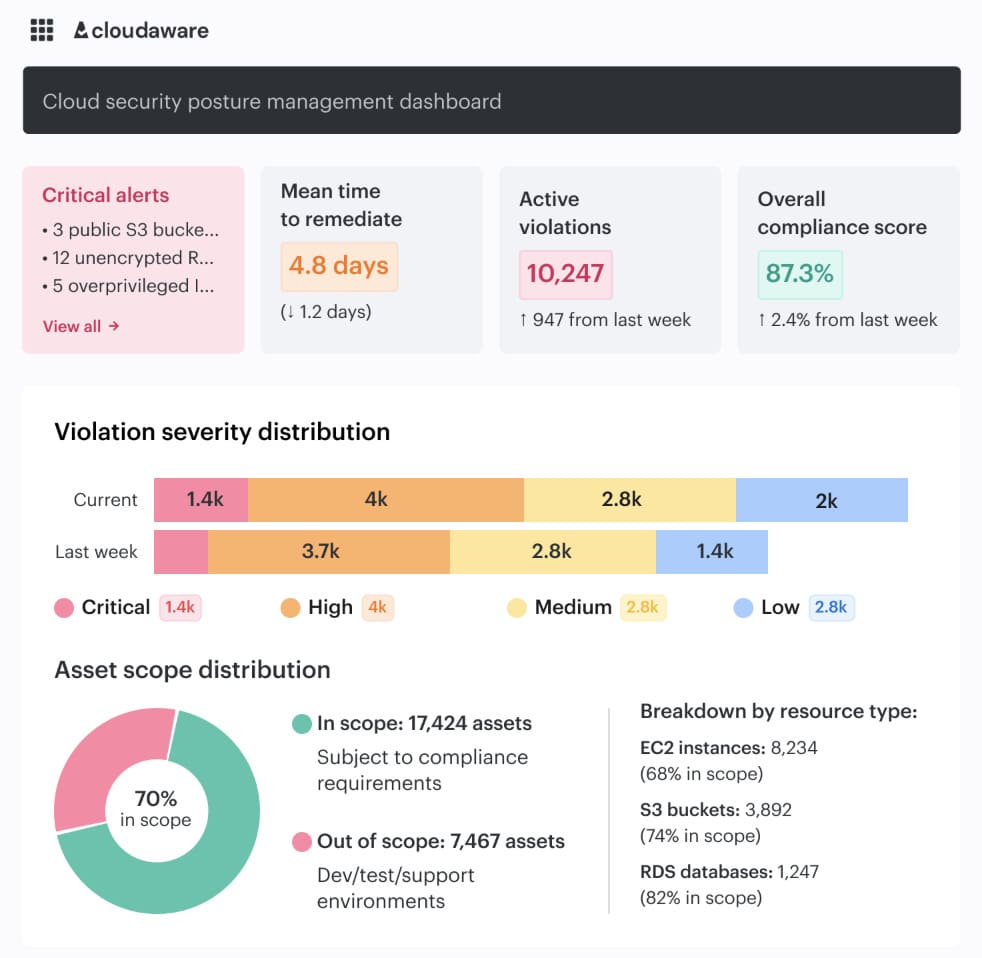
The practical win is reuse. One encryption control can support several frameworks when the evidence is tied to the asset, owner, environment, run history, and control result instead of rebuilt from scratch for every audit. - Scheduled evaluations, drift alerts, lifecycle tracking, owner notifications, and dashboards that let teams drill from top-line KPIs into exact check results.
This is where cloud security frameworks become useful day-to-day. Someone edits a bucket policy. A subscription appears outside the expected model. A logging rule stops applying after an IaC change. The point is not to discover the gap three months later during audit prep but to catch it while someone can still fix it. - Remediation workflows with ticketing context. Cloudaware treats failed checks as first-class rule findings with owner, severity, SLA, evidence, and lifecycle. Findings can open context-rich tickets in Jira or ServiceNow and route work by CMDB fields such as app, team, account, and environment.
- Owner-aware exception and risk tracking. Framework controls break when exceptions live outside the system. Cloudaware supports time-boxed exceptions and lifecycle tracking, so a production workload that violates an encryption policy can be treated as an approved exception, an expired risk acceptance, or a new policy breach that needs remediation.
- Audit-ready dashboards and exports. Cloudaware IT Compliance provides dashboards and exports with permanent run history, rule revisions, diffs, KPIs, controls, and evidence, so audits become retrieval instead of reconstruction.
The point is not to make Cloudaware another place to store framework language.
The point is to connect that language to the estate.
A control becomes useful when it can answer the operational questions: what failed, where it failed, who owns it, how serious it is, what changed, how it gets fixed, and where the proof lives.
