NIST cloud security seems straightforward until AC-2 turns into 400 IAM roles, CM-6 turns into policy exceptions across three providers, and AU-6 turns into a question nobody wants during the audit: who reviewed the logs, when, and what changed because of it?
This guide is based on NIST guidance, Cloudaware implementation experience, and practitioner discussion from the NISTControls community. The focus is on the translation layer: how controls become cloud services, owners, tickets, evidence, exceptions, and audit conversations.
TL;DR
- NIST cloud security is not one standard. CSF 2.0 gives the outcome model, SP 800-53 gives the control catalog, FedRAMP gives cloud interpretation, and the architecture decides where proof has to come from.
- CSF 2.0 can organize the program, but it cannot implement the control. Govern, Identify, Protect, Detect, Respond, and Recover need to be mapped to services, owners, and testable evidence before they mean anything operationally.
- The hard part is control applicability. A provider or CSPM mapping may connect one setting to one control, but that does not prove the control requirement is met or even applicable to that workload.
- Audit failures usually start with a scope, ownership, and evidence lifecycle. If assets, exceptions, identities, and findings are not tied to live cloud state, the team ends up reconstructing reality during the audit.
- Cloud compliance is a many-to-many mapping problem. One control can depend on identities, logs, network paths, workload configuration, and process evidence, while one cloud setting can only partially satisfy several controls.
What is NIST cloud security?
NIST cloud security is not a single framework. It is a collection of publications from the National Institute of Standards and Technology that define security outcomes, control requirements, and audit expectations for information systems, including cloud environments.
In practice, teams use NIST CSF 2.0 to define outcomes, SP 800-53 Rev. 5 to define controls, and FedRAMP to define cloud-specific implementation. The work starts when controls are implemented in cloud services and tied to evidence that can be validated continuously.
One recurring theme from engineers working with NIST in production environments is that frameworks are often misused as “apply every control everywhere” checklists. In turn, controls must be interpreted in the context of system risk, operational impact, architecture, and shared responsibility boundaries.
Why NIST guidance matters beyond federal compliance
NIST shows up far outside federal environments because other frameworks reuse the same control logic. ISO 27001, SOC 2, HIPAA, PCI DSS, CIS benchmarks, and cloud provider security packs all overlap with SP 800-53 somewhere.
That overlap creates another implementation problem. One IAM setting may map to multiple frameworks, while one NIST control may depend on identity data, logging, tickets, approval records, and exception tracking at the same time.
AC-2 is a good example. The control sounds simple: manage accounts and access. The actual implementation spreads across IAM roles, SSO, federation, workload identities, lifecycle automation, access reviews, and activity logs. Auditors usually care less about the policy text than whether you can show who had access, why they had it, and when it changed.
NIST cloud security standards
There is no single NIST cloud security standard. The useful model is a stack of documents, each answering a different question.
The core set is: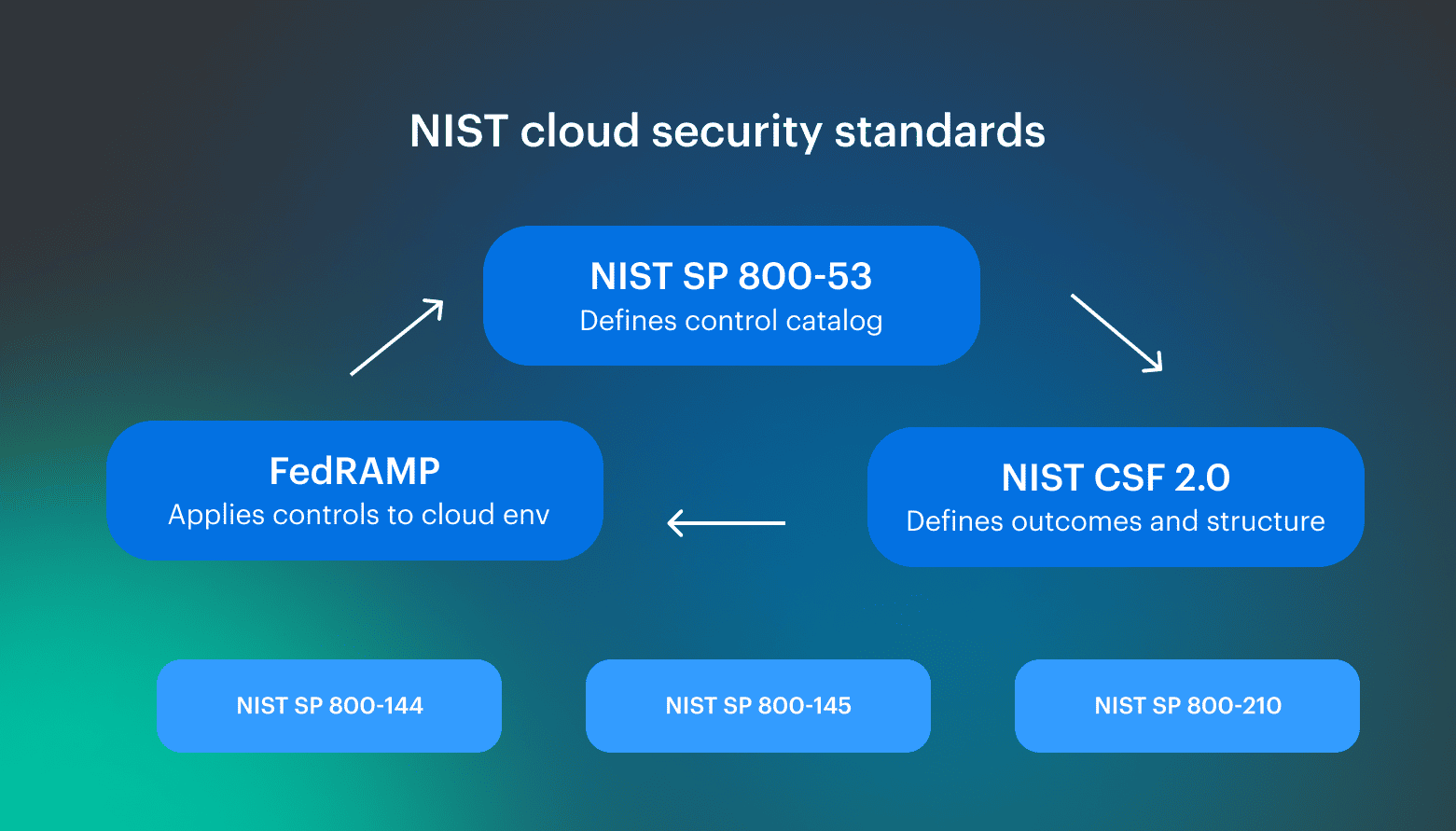
- NIST SP 800-53 Rev. 5: defines the control catalog (AC-2, CM-6, AU-6, CA-7)
- NIST CSF 2.0 (2024): defines security outcomes and program structure
- NIST SP 800-144: explains how controls apply in public cloud environments
- NIST SP 800-145: defines cloud service models (IaaS, PaaS, SaaS)
- NIST SP 800-210: provides access control guidance relevant to cloud identity
- FedRAMP baselines: apply SP 800-53 controls to cloud systems with inheritance and responsibility boundaries
But don’t treat any of them as “the standard,” or you will miss parts of the model:
- CSF without 800-53 = no enforceable controls
- 800-53 without FedRAMP = no cloud interpretation
- Controls without architecture = no proof
The NIST Cloud Security Framework explained
The NIST Cloud Security Framework most teams refer to is CSF 2.0. It organizes security work into six functions: Govern, Identify, Protect, Detect, Respond, and Recover.
CSF does not tell you:
- Which cloud services enforce control
- How inherited controls change responsibility
- Which evidence satisfies the auditor
- How exceptions are tracked
- How drift is monitored over time
That translation work usually happens through SP 800-53 mappings, cloud-native controls, CSPM policies, IaC standards, and audit procedures.
Daria, Сloud Security Expert at Cloudaware:
CSF works well for structuring ownership and reporting. It breaks down when teams try to operationalize it without a control mapping layer underneath.
The six functions of NIST CSF 2.0 in a cloud context
CSF tells you that you must be able to identify assets, protect them, detect issues, and respond with evidence.
| Function | What it means in cloud | Example implementation (AWS / Azure / GCP) |
|---|---|---|
| Govern | Define cloud risk ownership, policies, and accountability | Account structure, management groups, tagging strategy, SCPs |
| Identify | Maintain inventory of assets, identities, and data | Multi-cloud CMDB, asset discovery, data classification |
| Protect | Enforce access control, encryption, and hardening | IAM roles, KMS, network segmentation, CIS baselines |
| Detect | Monitor for misconfigurations and threats continuously | AWS GuardDuty, Azure Defender, GCP SCC, log pipelines |
| Respond | Execute incident response actions consistently | Runbooks, ticketing, SOAR integrations |
| Recover | Restore services and validate resilience | Backups, DR plans, post-incident reviews |
How CSF 2.0 maps to SP 800-53 control families
One CSF category usually maps to multiple SP 800-53 families. One technical control often partially satisfies multiple requirements simultaneously. That creates a many-to-many mapping problem auditors eventually dig into.
For example:
- Identify (ID.AM): CM-8 (Asset Inventory), RA-2 (Risk Assessment)
- Protect (PR.AC): AC-2 (Account Management), AC-6 (Least Privilege)
- Detect (DE.CM): SI-4 (System Monitoring), AU-6 (Audit Review)
- Respond (RS): IR-4 (Incident Handling)
- Recover (RC): CP-9 (Backup), CP-10 (Recovery)
A useful rule: CSF is for describing security posture. SP 800-53 is for proving it.
Download the NIST cloud security framework PDF
If you are looking for the official framework, NIST publishes CSF 2.0 as a downloadable PDF on its website. The PDF explains structure and terminology, but it does not help you implement or prove controls.
Usually, teams need a cloud-adapted version:
- CSF functions mapped to SP 800-53 controls
- Controls mapped to AWS, Azure, and GCP services
- Evidence sources defined per control
Read also: Cloud Security Frameworks. 7 Top Standards Compared (2026)
How NIST actually works
NIST works in the cloud only when you separate four layers: outcome, control, responsibility, and evidence. And failures usually sit between those layers. 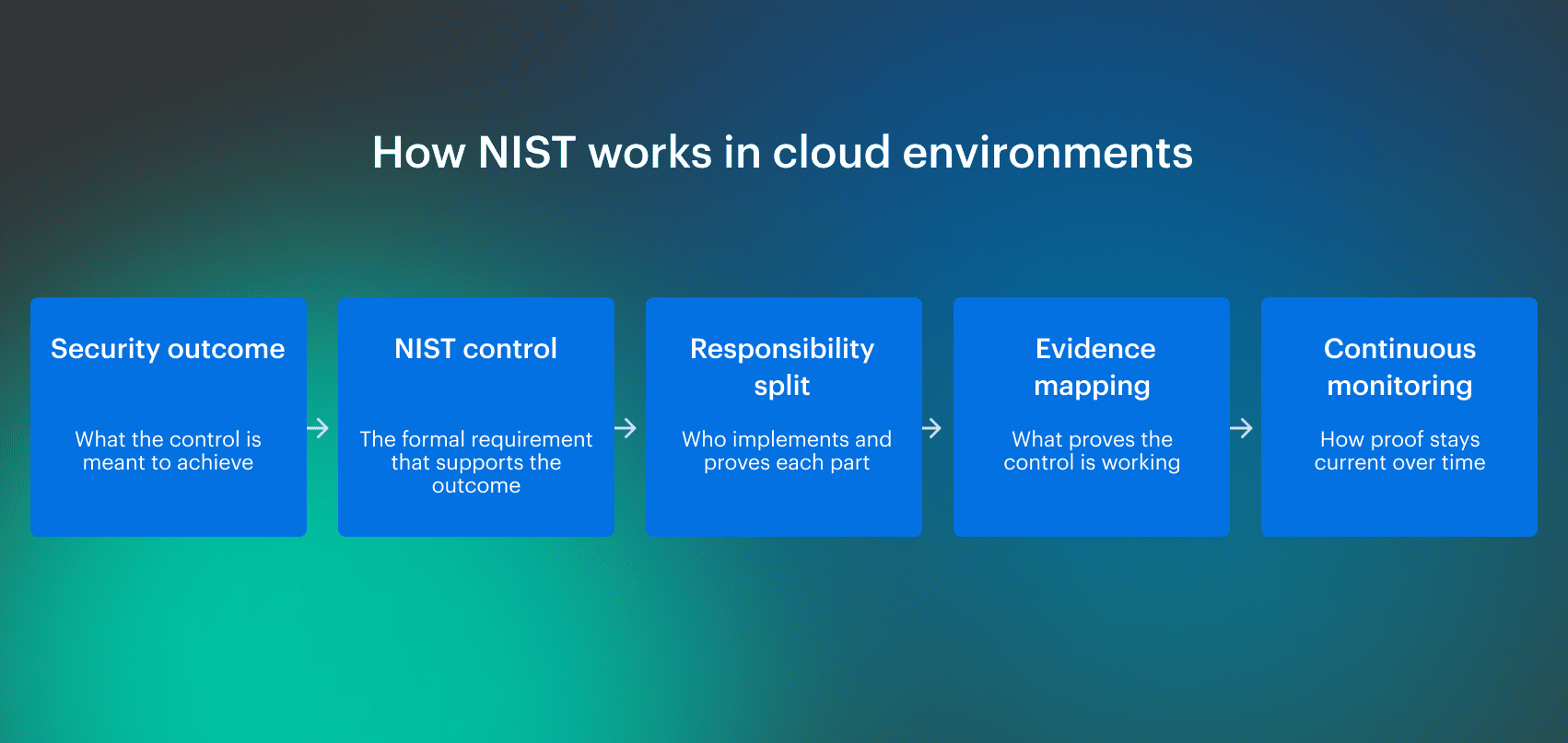
The shared responsibility model breaks traditional NIST assumptions
NIST SP 800-144 makes one thing explicit: you do not control the full system in the cloud. Controls that assume full infrastructure ownership must be split across provider and customer boundaries.
SC-8 is a clean example. The control covers data in transit, but the implementation depends on the traffic path.
| Scope | Control responsibility | Evidence |
|---|---|---|
| Physical network and data center | Provider-owned | Provider attestation, FedRAMP package, SOC report |
| External traffic | Customer-owned | TLS configuration, certificate inventory, ingress policy |
| Service-to-service traffic | Customer-owned or shared | mTLS policy, service mesh config, network policy |
| Managed service backbone | Provider-owned or inherited | Provider documentation, CRM entry |
| Workload identity and authorization | Customer-owned | IAM roles, workload identities, access logs |
The auditor will not accept “the cloud provider handles it” unless the control is clearly inherited. The customer-owned side still needs implementation evidence.
Control inheritance and the Customer Responsibility Matrix (CRM)
Control inheritance is how cloud environments stay auditable at scale. Instead of implementing every control from scratch, you inherit a portion of them from the provider through programs like FedRAMP.
In practice, this is captured in a Customer Responsibility Matrix (CRM):
- Fully inherited controls: implemented and evidenced by the cloud provider
- Partially inherited controls: shared responsibility
- Customer-implemented controls: fully your responsibility
Example:
| CM-8 (Asset Inventory) | AC-2 (Account Management) |
|---|---|
| Provider: infrastructure-level assets | Provider: platform access controls |
| Customer: cloud resources, workloads, identities | Customer: IAM users, roles, federation |
Continuous monitoring vs point-in-time audits (CA-7)
SP 800-53 CA-7 defines Continuous Monitoring. It does not say “review controls annually,” that’s why you need an ongoing assessment of control effectiveness.
In cloud environments, this changes how controls must be implemented:
- Configuration controls (CM-2, CM-6): evaluated continuously via AWS Config, Azure Policy, GCP Asset Inventory
- Identity controls (AC-2, AC-6): monitored through IAM activity and change logs
- Logging controls (AU-2, AU-6): validated through centralized log pipelines
The evidence requirement shifts from static screenshots to time-based, API-backed proof
NIST cloud computing security controls
NIST cloud security controls are based on SP 800-53 Rev. 5, which defines a catalog of control families covering access, configuration, monitoring, and risk.
In cloud environments, controls are not written as AWS, Azure, or GCP instructions. They describe outcomes that have to be translated into IAM rules, logging coverage, network boundaries, policy checks, tickets, and evidence.
The 20 NIST SP 800-53 Rev. 5 control families
SP 800-53 organizes controls into 20 families. Each family groups related requirements that must be implemented and assessed.
- AC — Access Control
- AT — Awareness and Training
- AU — Audit and Accountability
- CA — Assessment, Authorization, and Monitoring
- CM — Configuration Management
- CP — Contingency Planning
- IA — Identification and Authentication
- IR — Incident Response
- MA — Maintenance
- MP — Media Protection
- PE — Physical and Environmental Protection
- PL — Planning
- PS — Personnel Security
- PT — PII Processing and Transparency
- RA — Risk Assessment
- SA — System and Services Acquisition
- SC — System and Communications Protection
- SI — System and Information Integrity
- SR — Supply Chain Risk Management
- PM — Program Management
Igor K., DevOps Engineer:
“Some families map cleanly to cloud settings. Others live in process, ownership, approvals, training records, contracts, or physical controls inherited from the provider. Treating every family like a CSPM check creates false findings and missed risk.”
NIST SP 800-53 cloud security controls that matter most
For cloud teams, the highest-friction control families are the ones tied to identity, logging, configuration, incident response, risk, and runtime integrity. They create the most audit work because they change constantly
| Control Family | What it means in cloud | Typical implementation | Evidence source |
|---|---|---|---|
| AC — Access Control | Identity is the perimeter | IAM roles, RBAC, federation, least privilege | IAM policies, role usage logs |
| AU — Audit & Accountability | Logging validates all other controls | Centralized logging across all accounts | CloudTrail, Activity Logs, Audit Logs |
| CM — Configuration Management | Drift creates exposure | Policy enforcement, baseline configs | AWS Config, Azure Policy, GCP Asset Inventory |
| IA — Identification & Authentication | Strong identity for users and workloads | MFA, SSO, workload identity, certificates | IdP logs, certificate inventory |
| IR — Incident Response | Cross-cloud response capability | Runbooks, alert routing, SOAR | Incident tickets, response timelines |
| RA — Risk Assessment | Continuous risk visibility | Vulnerability scans, CSPM findings | Scan reports, risk dashboards |
| SC — System & Communications Protection | Network and encryption controls | TLS/mTLS, segmentation, private networking | KMS configs, network topology, TLS configs |
| SI — System & Information Integrity | Detect and fix issues in runtime | Patch management, EDR, integrity checks | Patch status, EDR alerts, remediation logs |
How FedRAMP tailors NIST controls for the cloud
FedRAMP takes SP 800-53 controls and turns them into cloud-ready baselines. It does this in two ways:
- Baseline selection. Controls are grouped into Low, Moderate, and High impact systems. Each level includes a predefined subset of controls.
- Control interpretation. Requirements are clarified for cloud environments, including inheritance from cloud providers.
For example:
- SC-8 (data in transit): clarified in terms of cloud networking and controlled boundaries
- CM-6 (configuration settings): enforced through provider-native policy engines
- CA-7 (continuous monitoring): expected to be automated, not manual
FedRAMP also introduces the Customer Responsibility Matrix, which defines which controls are inherited, shared, or customer-owned. In practice, most non-federal organizations still use FedRAMP baselines because they provide the closest thing to a cloud-specific implementation of SP 800-53.
The 8 critical NIST control families for cloud security
Based on field experience with cloud engineering and audit teams, these 8 NIST control families create most of the audit friction in cloud environments. Each family below is tied to a common failure pattern and backed by Cloudaware platform evidence that shows how the control is monitored, assigned, and proven over time.
1. Access Control (AC)
AC-2 and AC-6 look clean until IAM spreads across humans, roles, service accounts, workload identities, and cross-account access.
Cloud implementation: SSO, federation, role assumptions, service accounts, workload identity, and access reviews. The failure pattern is familiar: privilege gets granted during an incident or migration, then stays.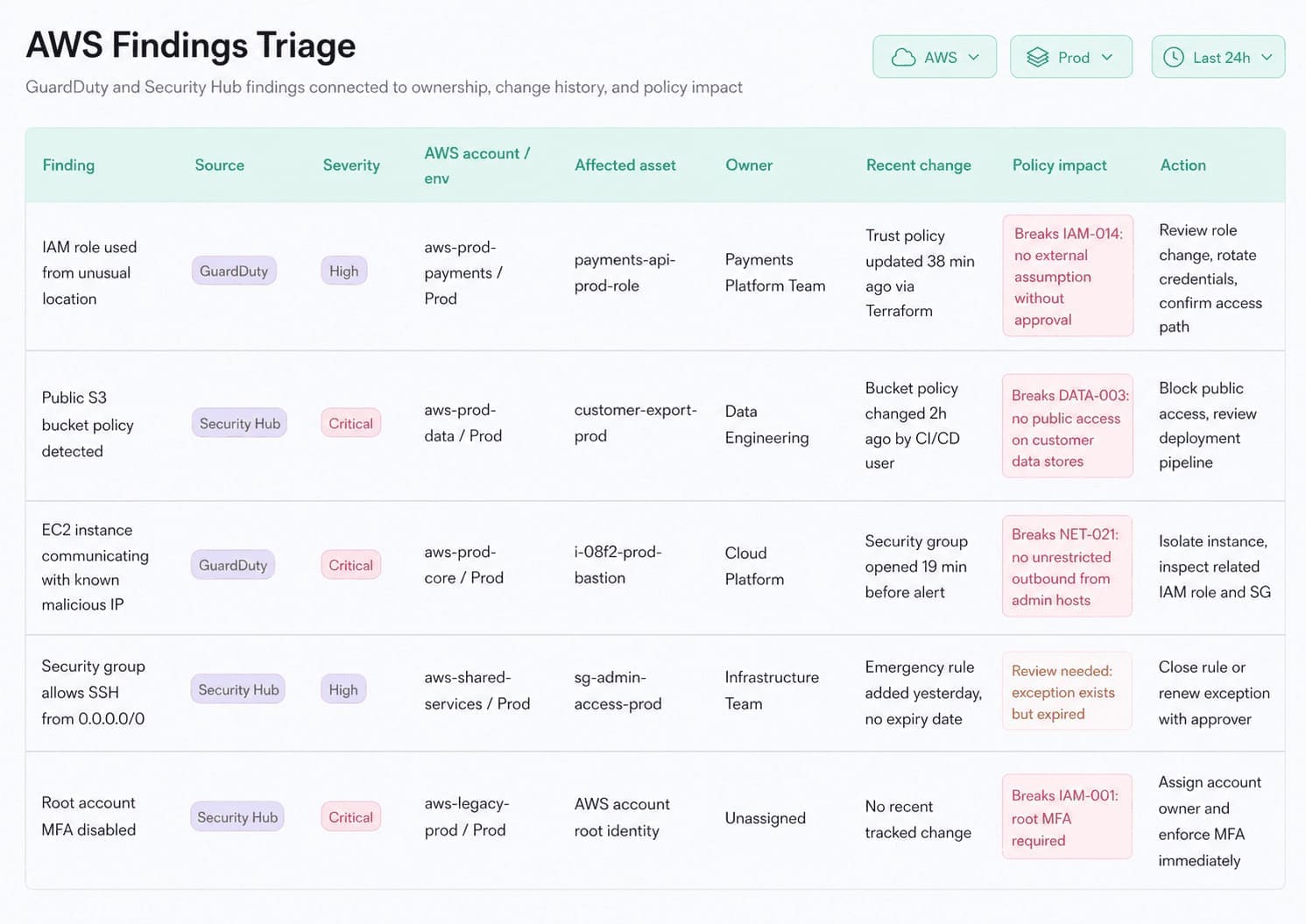 Cloudaware dashboard showing IAM policy violations, unusual role activity, ownership context, recent privilege changes, and remediation workflows for access control review.
Cloudaware dashboard showing IAM policy violations, unusual role activity, ownership context, recent privilege changes, and remediation workflows for access control review.
Audit evidence: role usage, last-used timestamps, access review records, approval history, and privilege reduction over time. A policy export only shows what exists. It does not show whether access was justified.
2. Audit and Accountability (AU)
AU-2 and AU-6 require logging and review of system activity to support accountability, investigation, and control validation.
Cloud implementation: CloudTrail, Azure Activity Logs, GCP Audit Logs, SIEM routing, retention rules, alert logic, and review workflows. Enabling logs is the easy part. Proving they cover every account, project, service, and privileged action is harder.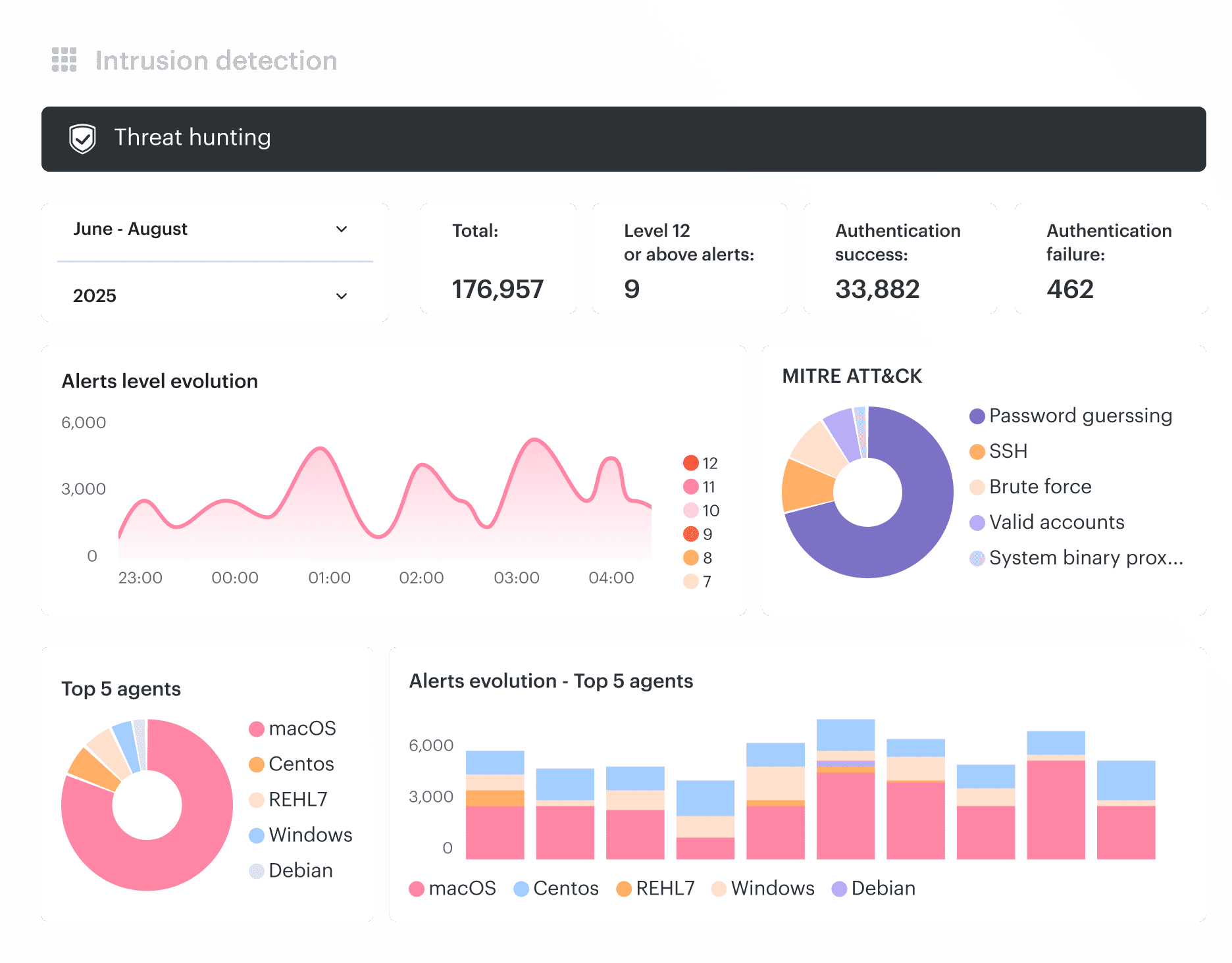 Cloudaware audit monitoring dashboard correlating authentication events, alert severity, monitored agents, and investigation telemetry for continuous audit review.
Cloudaware audit monitoring dashboard correlating authentication events, alert severity, monitored agents, and investigation telemetry for continuous audit review.
Audit evidence: log coverage reports, retention settings, review tickets, saved searches, alert history, and incident links. A log bucket without review activity is storage, not accountability.
3. Configuration Management (CM)
CM-2 and CM-6 become drift and exception problems.
Cloud implementation: AWS Config, Azure Policy, GCP Org Policy, Terraform checks, CIS benchmarks, STIGs, and approved baselines. The failure pattern is stale exceptions: one team gets a temporary bypass, the workload changes, and the exception never closes.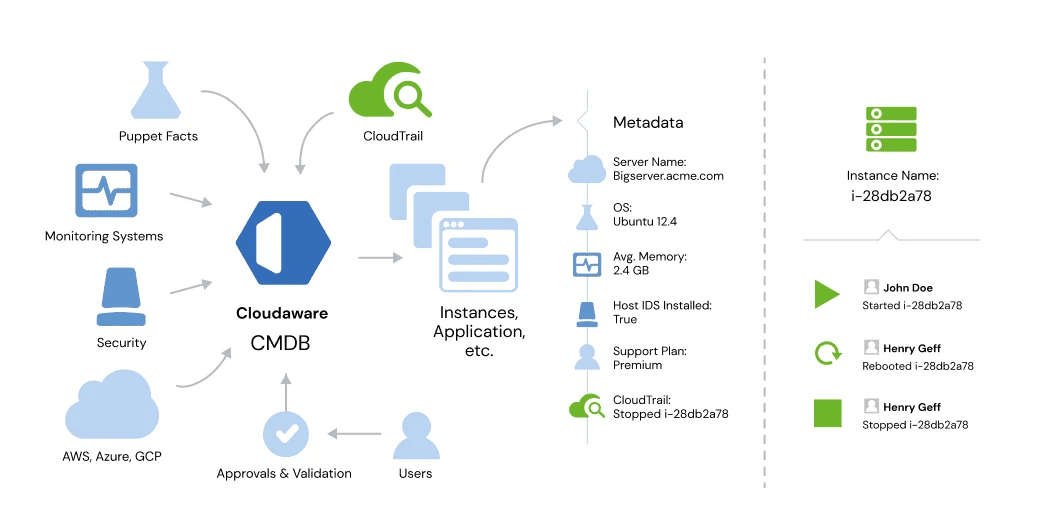 Cloudaware’s CMDB-driven configuration tracking that correlates CloudTrail events, infrastructure metadata, approvals, and operational state changes for CM-2 and CM-6 validation.
Cloudaware’s CMDB-driven configuration tracking that correlates CloudTrail events, infrastructure metadata, approvals, and operational state changes for CM-2 and CM-6 validation.
Audit evidence: policy results, drift history, baseline changes, exception owners, approval dates, and expiration dates. A baseline without exception tracking will not explain real cloud state.
4. Identification and Authentication (IA)
IA breaks when workload identity is treated as secondary to human identity.
Cloud implementation: MFA, SSO, service principals, access keys, certificates, workload identity federation, and short-lived credentials. Long-lived keys and unmanaged service accounts usually create the findings.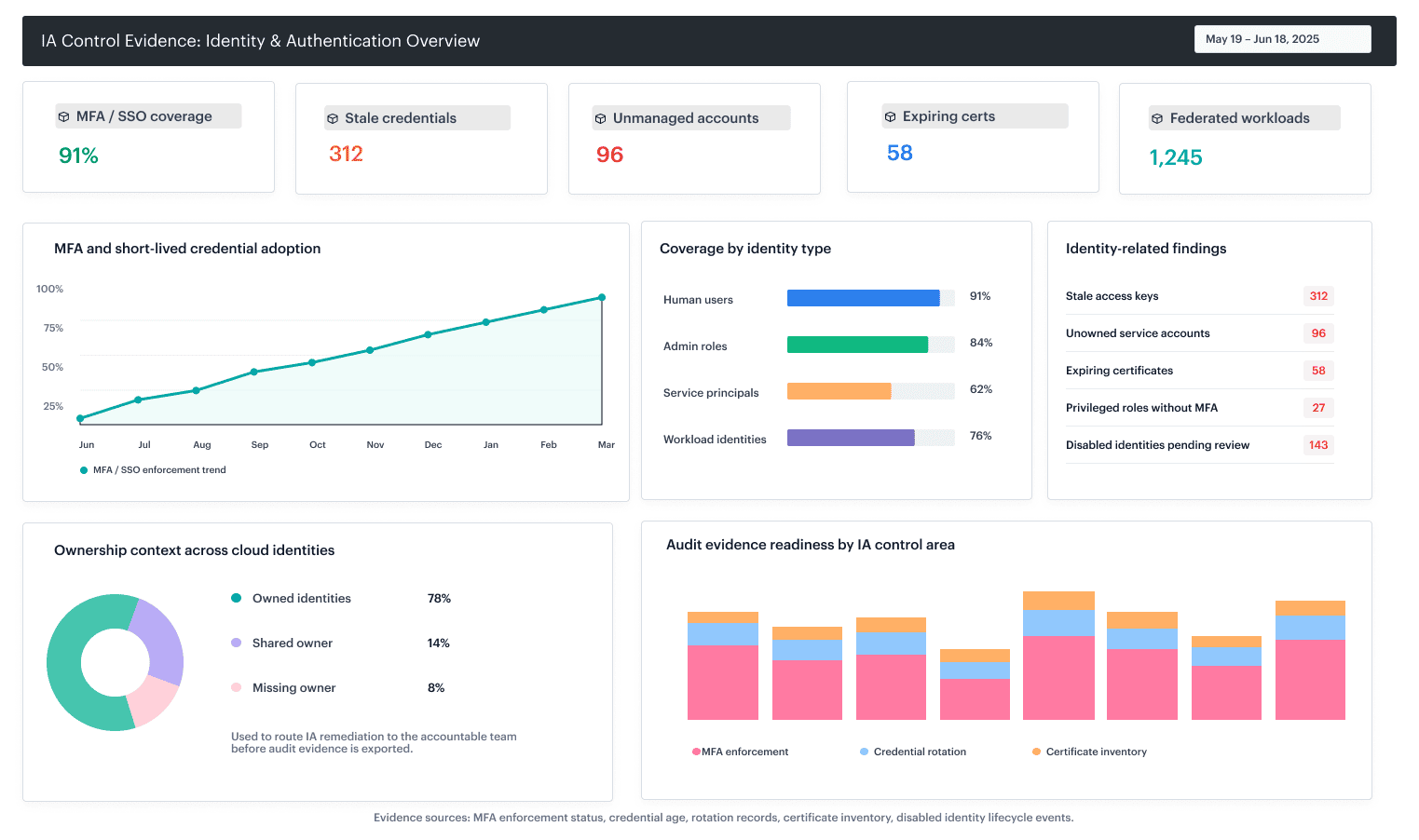 Cloudaware dashboard showing identity-related findings, stale credentials, MFA coverage, service account exposure, certificate inventory, and ownership context across cloud identities.
Cloudaware dashboard showing identity-related findings, stale credentials, MFA coverage, service account exposure, certificate inventory, and ownership context across cloud identities.
Audit evidence: MFA enforcement, credential age, rotation records, certificate inventory, disabled identities, and lifecycle events. Auditors will look for stale credentials before they read the access policy.
5. Incident Response (IR)
IR-4 depends less on the runbook and more on whether alerts become owned work.
Cloud implementation: runbooks, routing rules, ticket creation, escalation paths, cloud-specific playbooks, and post-incident review. The failure pattern is a clean runbook with no execution trail.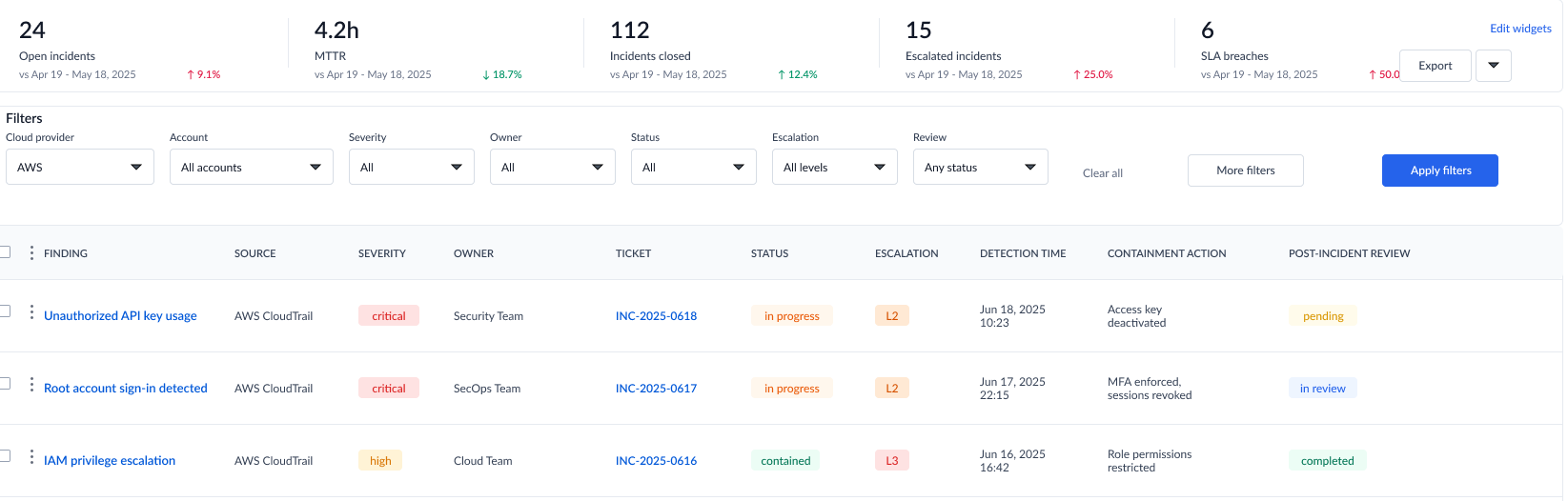 Cloudaware-style incident response dashboard showing findings routed to owners, linked tickets, escalation state, containment actions, and post-incident review status.
Cloudaware-style incident response dashboard showing findings routed to owners, linked tickets, escalation state, containment actions, and post-incident review status.
Audit evidence: incident tickets, detection-to-response timestamps, escalation records, containment actions, remediation links, and post-incident changes. If the workflow stops at an alert, the control is weak.
6. Risk Assessment (RA)
RA-5 fails when vulnerability and CSPM findings become a volume rather than a risk.
Cloud implementation: scanner results, CSPM findings, exposure data, asset criticality, internet reachability, and exploitability. The issue is prioritization. A critical CVE on an isolated test box is not the same as the same CVE on an internet-facing production workload.
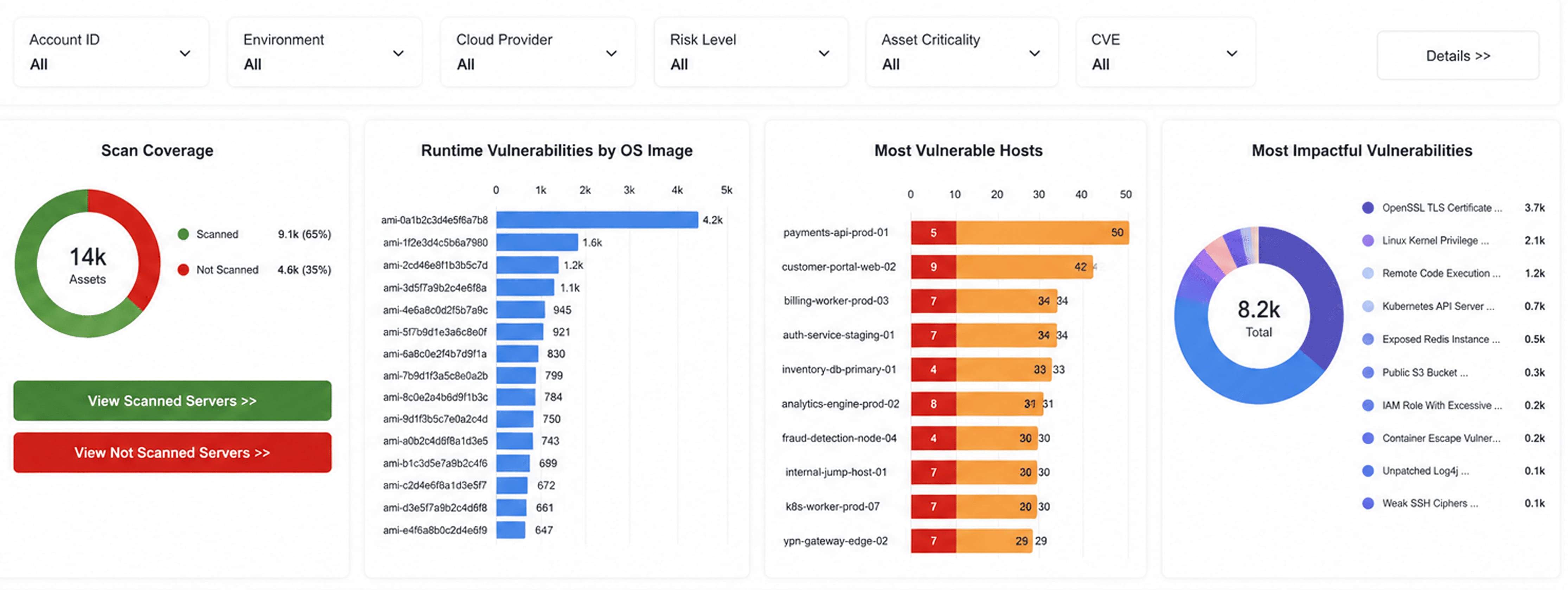
Cloudaware’s vulnerability and risk dashboard showing scan coverage, SLA aging, MTTR, vulnerable hosts, and remediation backlog tied to runtime exposure and asset context.
Audit evidence: scan history, risk scoring, remediation SLAs, accepted-risk records, and proof that high-risk findings move faster than low-risk noise.
7. System and Communications Protection (SC)
SC-8 and SC-13 get messy when traffic paths cross managed services, service meshes, private endpoints, and provider backbones.
Cloud implementation: TLS, mTLS, KMS, private networking, ingress control, egress control, segmentation, and service-to-service policy. Sidecars, mesh modes, and managed service.
Audit evidence: encryption enforcement, certificate state, KMS configuration, network topology, ingress and egress rules, and service mesh policy where used. The control fails when the trust boundary cannot be explained.
8. System and Information Integrity (SI)
SI-2 and SI-4 require detection, correction, and monitoring of flaws and malicious activity.
Cloud implementation: patching, EDR, workload protection, runtime detection, vulnerability remediation, and integrity monitoring. The hard cases are unmanaged instances, short-lived workloads, containers, and systems outside the agent footprint.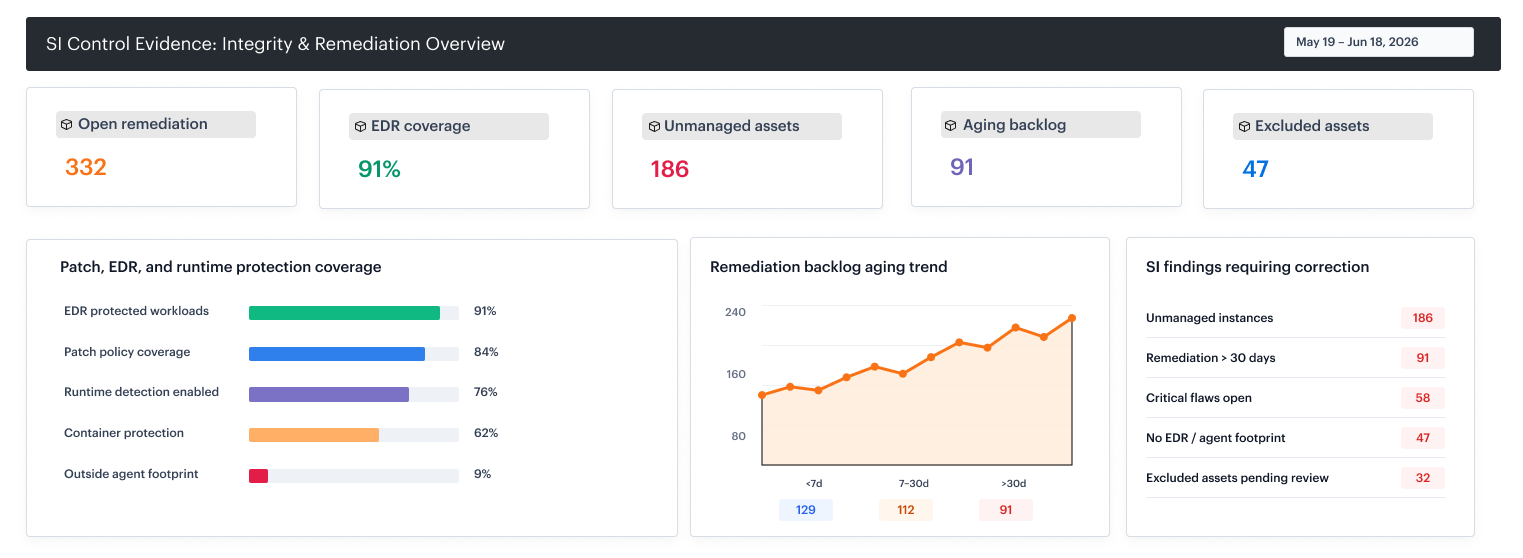 Cloudaware’s integrity and remediation dashboard showing remediation ownership, aging, resource exposure, backlog trends, and corrective actions across cloud workloads and environments.
Cloudaware’s integrity and remediation dashboard showing remediation ownership, aging, resource exposure, backlog trends, and corrective actions across cloud workloads and environments.
Audit evidence: patch timelines, EDR or workload protection coverage, remediation logs, detection history, and excluded assets with owners. Auditors will ask about what is missing, not only what is green.
These eight families matter most because they produce continuous, testable signals in cloud environments. Other families still apply, but these are the ones auditors will focus on when validating real security posture.
NIST cloud security best practices
This section is based on NIST SP 800-53 Rev. 5, NIST CSF 2.0, and FedRAMP baselines, and cloud provider implementation patterns.
Several practitioners also pointed to the CSA Cloud Controls Matrix (CCM) as a useful cloud-native translation layer because it maps cloud-specific operational controls back to frameworks like NIST SP 800-53.
NIST cloud security best practices for multi-cloud environments
- Build a complete asset inventory (CM-8, ID.AM). If you do not know what exists, no control is complete. In multi-cloud, this means aggregating AWS, Azure, and GCP assets into one inventory. Evidence comes from continuously updated asset data.
- Treat IAM as a continuous control (AC-2, AC-6). Least privilege is not a policy. It is a process. Roles, service accounts, and federated identities must be reviewed and reduced over time. Evidence is identity change history and access review records.
- Enforce configuration as code (CM-6). Baseline definitions are not enough. Policies must be enforced, and drift tracked. Evidence is a configuration state over time, including exceptions and remediation.
- Centralize and use logs (AU-2, AU-6). Logging without review does not meet the control. Logs must drive alerts, investigations, and tickets. Evidence is not log existence, but log usage.
- Encrypt with defined boundaries (SC-8, SC-13). Encryption must align with actual trust boundaries. In cloud-native systems, this includes service-to-service communication. Evidence is enforcement, not intent.
- Run continuous vulnerability management (RA-5, SI-2). Scanning alone is not sufficient. Risk must be prioritized and tracked for remediation. Evidence is remediation timelines, not scan volume.
- Operationalize incident response (IR-4). Runbooks must translate into executed actions. Evidence is real incidents, not documentation.
- Define control ownership (PL-2, PM-1). Every control needs an owner. Without ownership, controls degrade silently. Evidence is accountability, not structure.
- Map controls across frameworks once (CA-2). NIST mappings should also extend to ISO 27001, SOC 2, and other standards. Evidence reuse reduces audit overhead.
- Move to continuous monitoring (CA-7). Point-in-time checks do not hold in the cloud. Evidence must be continuously generated from APIs and the system state.
Read also: Cloud Security Best Practices. Strategy, Checklist, Monitoring, and Automation
Common pitfalls when applying NIST in AWS, Azure, and GCP
NIST treats cybersecurity risk management as a continuous process, which is where point-in-time audit habits break down.
1. Treating CSF as an implementation
CSF 2.0 is an outcome framework, not an engineering checklist. If you stop at Govern, Identify, Protect, Detect, Respond, and Recover, you get a reporting model, not an auditable control system.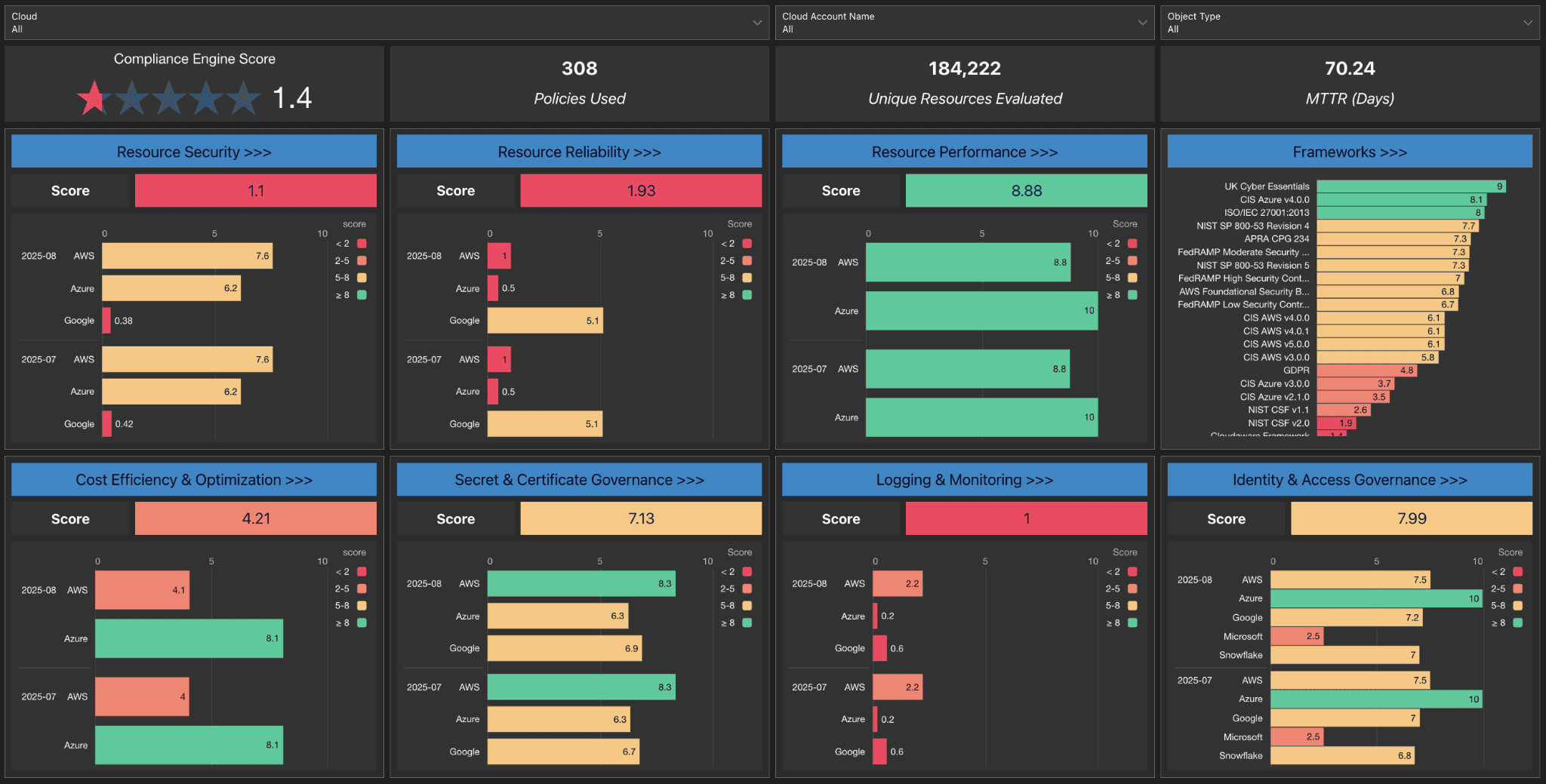 Cloudaware gives teams a control-mapping layer through its Compliance Engine, so NIST outcomes can be tied to actual policies, assets, findings, and evidence instead of staying in a spreadsheet.
Cloudaware gives teams a control-mapping layer through its Compliance Engine, so NIST outcomes can be tied to actual policies, assets, findings, and evidence instead of staying in a spreadsheet.
2. Assuming provider compliance covers customer controls
FedRAMP requires cloud providers to document customer responsibility through the CIS/CRM workbook. That means provider authorization does not cover your IAM roles, workload configurations, data classification, or logging decisions.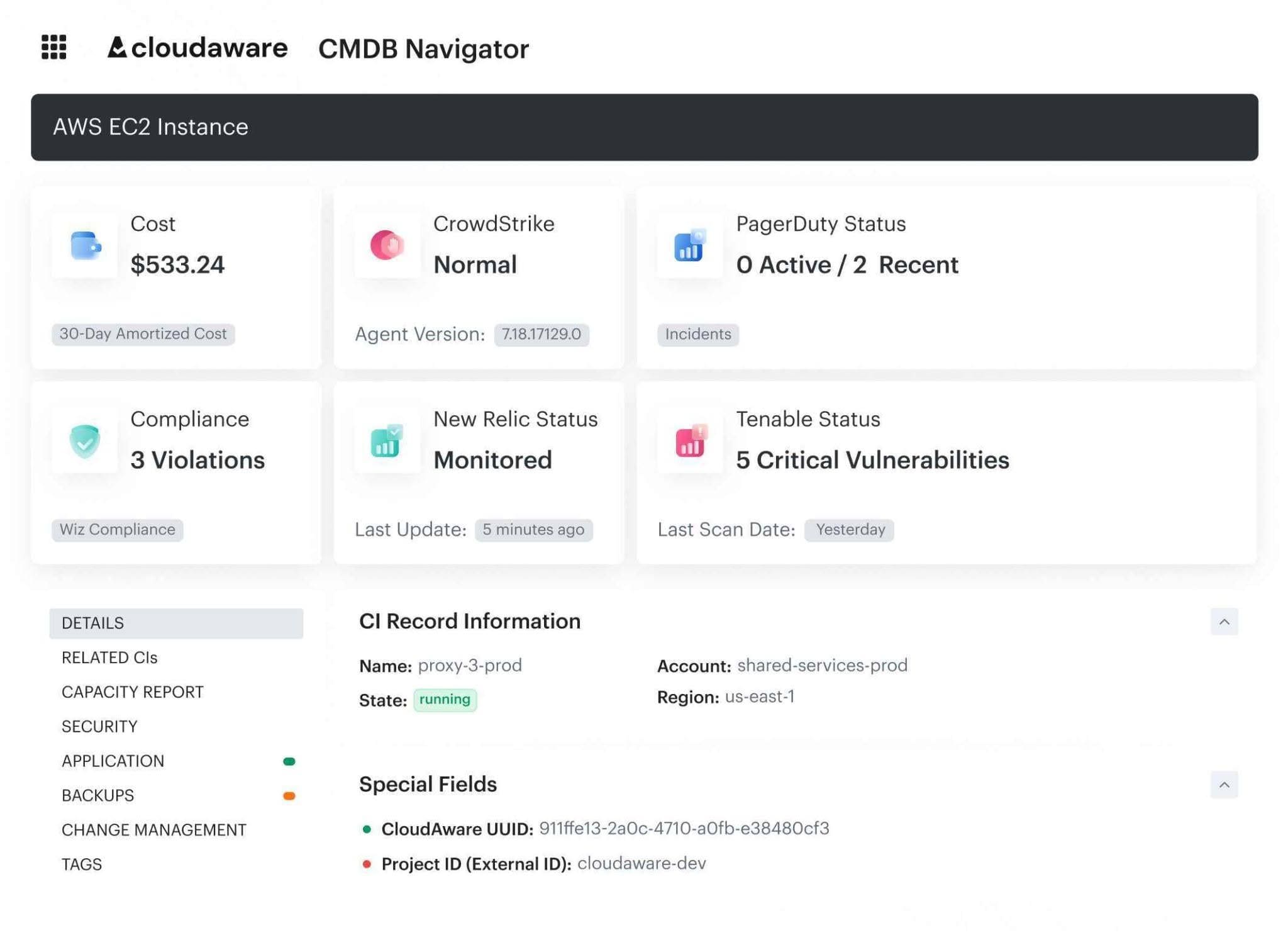 Cloudaware normalizes customer-owned assets across cloud and operational systems into one CMDB. For each CI, teams can see the account, region, state, compliance findings, vulnerability data, monitoring status, and incident context.
Cloudaware normalizes customer-owned assets across cloud and operational systems into one CMDB. For each CI, teams can see the account, region, state, compliance findings, vulnerability data, monitoring status, and incident context.
3. Treating evidence as point-in-time screenshots
CA-7 is about continuous monitoring, not annual screenshot collection. If evidence cannot show control state over time, it will not hold up well in a serious audit.
Cloudaware connects compliance findings to a live asset inventory and operational workflows. Learn more in the multi-cloud compliance case study.
4. Ignoring identity sprawl across accounts and environments
In the cloud, AC and IA controls extend beyond human users. They include service accounts, federated roles, workload identities, certificates, and cross-account access paths. The audit issue is usually “no IAM.”
Cloudaware gives IAM findings ownership and environment context across cloud accounts. Teams can filter access issues by provider, account, owner, product, and environment, then track open issue age and MTTR.
5. Treating vendor mappings as proof of compliance
Cloud providers and CSPM vendors often map individual settings directly to NIST controls, but a setting is not the same thing as a control requirement. Teams start overengineering environments and generating findings that are technically “mapped,” but not actually required by the control intent.
Engineers repeatedly run into this issue with CIS mappings, DLP recommendations, and provider security packs, where configuration status gets confused with actual control applicability.
NIST cloud security audit checklist
A NIST cloud security audit checklist is a repeatable test of control implementation and evidence. Each row should tie a control to a cloud-specific check and a source of proof that can be re-run at any time.
What does a strong NIST cloud security audit checklist contain
- Control ID (e.g., AC-2, CM-6)
- Plain-language requirement
- Cloud scope (AWS / Azure / GCP / multi-cloud)
- Asset scope (account, subscription, project, workload)
- Test procedure (how the control is validated)
- Data source (API, log, config service)
- Expected state (pass condition)
- Evidence type (log, config snapshot, report)
- Control owner (team or role)
- Frequency (continuous, daily, weekly)
- Current status (pass/fail /exception)
- Exception record (if applicable)
- Remediation action
- Target resolution date
- Last validated timestamp
Example: A company officially runs production workloads only in us-east-1 and us-west-2, but the cloud account still has access to 30+ AWS regions. A weak checklist marks every unused region as a failure for logging, encryption, network restrictions, and monitoring. The result is hundreds of irrelevant violations and no clear remediation owner.
A strong NIST cloud security audit checklist prevents that by separating cloud scope, asset scope, expected state, exception record, owner, and expiration date. The checklist should show that only approved regions are in scope, unused regions are excluded by documented exception logic, and any exception has a reason, owner, and review date.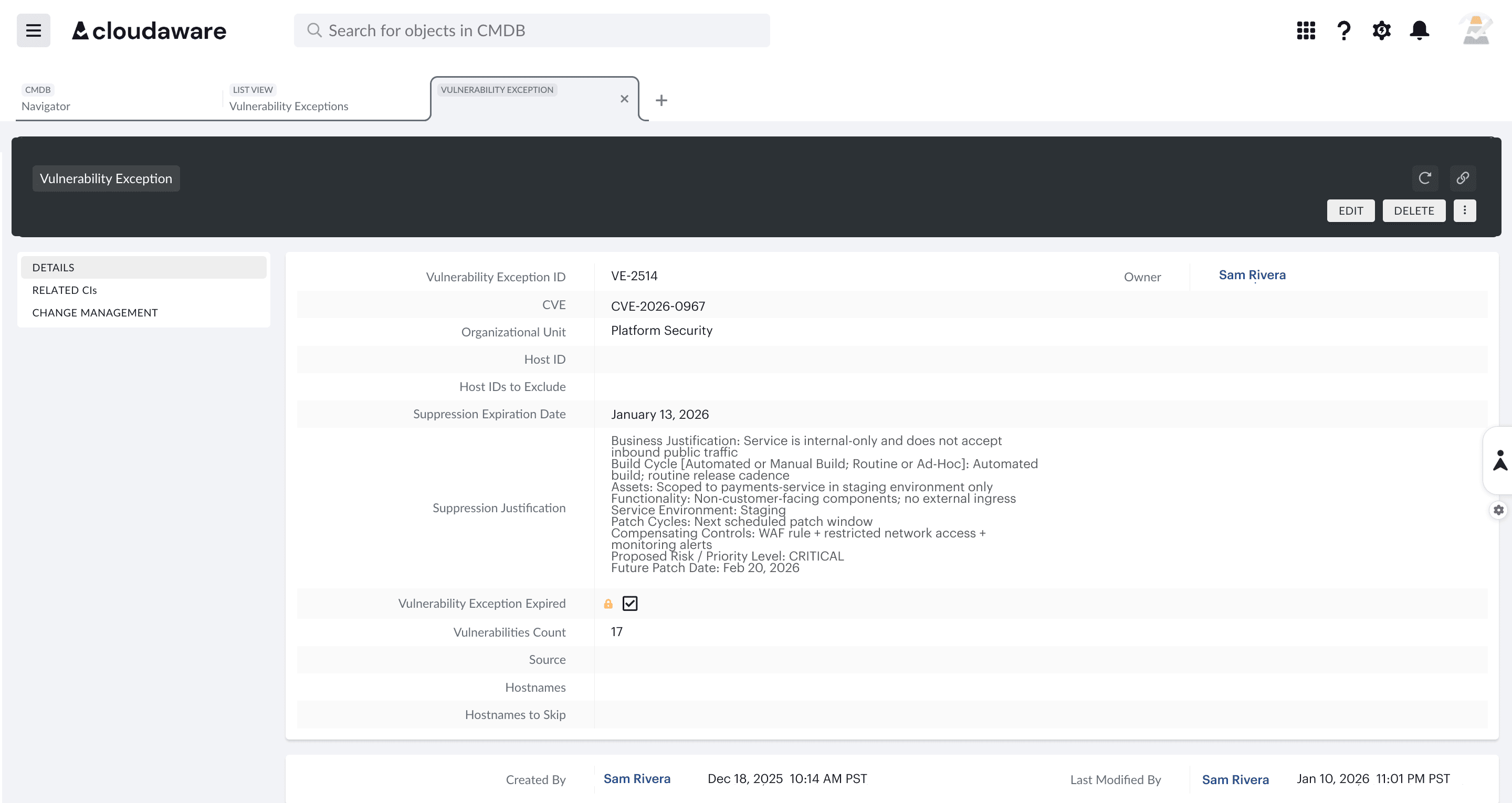 The scope can be tied to CMDB context and policy evaluation so the audit view reflects actual governance boundaries, not raw provider surface area.
The scope can be tied to CMDB context and policy evaluation so the audit view reflects actual governance boundaries, not raw provider surface area.
Sample audit checklist entries (AWS, Azure, GCP)
| Control | Cloud | Test procedure | Evidence | Pass condition |
|---|---|---|---|---|
| AC-2 Account Management | AWS | List IAM users and roles; verify unused accounts | IAM API, CloudTrail | No inactive or orphaned identities |
| CM-6 Configuration Settings | Azure | Evaluate policy compliance for resource configs | Azure Policy | All required policies enforced |
| AU-2 Audit Logging | GCP | Check audit logging enabled across projects | GCP Audit Logs | Logging enabled for all services |
How to prepare for a NIST cloud audit
NIST cloud audits fail for a few predictable reasons: unclear boundaries, unmapped controls, weak evidence, unowned findings, and mock audits that happen too late. The preparation process is about making sure every control can be tested against the live cloud state and explained to an auditor.
We share practical notes from Cloudaware engineers and Technical Account Managers who work with customers during audit preparation.
Step 1: Define system boundaries and assets
Start with the scope. SP 800-53 assumes you know what system is being assessed. In the cloud, that means accounts, subscriptions, projects, regions, workloads, and data flows.
This is where most audits break. Teams define boundaries in documents, but not in systems.
Alla L., Technical Account Manager: “The first issue we see is that teams cannot answer what exactly is in scope. Not at a document level, but at a resource level. If you cannot list the assets, you cannot prove any control.”
Step 2: Map controls to cloud services
Controls must be translated into a cloud-native implementation.
- AC-2: IAM users, roles, identity providers
- CM-6: AWS Config, Azure Policy, GCP Org Policy
- AU-2: CloudTrail, Activity Logs, Audit Logs
The failure is treating controls as abstract requirements instead of mapping them to services and configurations.
Igor K., DevOps Engineer: “Teams often say they meet a control, but cannot point to where it is implemented. In the cloud, every control should map to a service, a configuration, and an owner.”
Step 3: Collect and validate evidence
If evidence cannot be re-run, it will not hold.
- Configuration snapshots
- API outputs
- Logs and change history
Valentin Kel, Software Engineer: “Screenshots are the fastest way to fail an audit. Auditors want to see that a control works over time, not that it worked once.”
Step 4: Build POA&M and remediation plan
Not every control will pass, and that is expected. What matters is how findings are tracked and resolved.
- Define severity
- Assign ownership
- Set remediation timelines
Kristina S., Senior Technical Account Manager: “A finding without an owner is not a finding. It is noise. The audit looks at how quickly issues move, not just how many exist.”
Step 5: Run a mock audit
Before the real audit, test everything:
- Can you reproduce evidence on demand?
- Can you explain control ownership?
- Can you show the change history?
If any answer depends on manual reconstruction, the audit will expose it. The goal is not just “pass the audit,” but to make control validation repeatable without preparation cycles.
How Cloudaware helps to operationalize NIST cloud security
NIST becomes useful when controls are tied to live cloud assets, evaluated against current configuration state, mapped across frameworks, and explained with evidence that does not need to be rebuilt before every audit. Cloudaware closes that operating gap through CMDB-based policy evaluation, framework mapping, violation management, and remediation workflows.
- Single multi-cloud CMDB as the foundation for NIST Identify. Cloudaware builds normalized inventory across AWS, Azure, GCP, and connected systems, linking each resource to account, environment, owner, application, and operational context.
- IT Compliance Engine for mapped NIST policies. Cloudaware evaluates CMDB inventory against policies and framework mappings, including NIST, CIS, FedRAMP, SOC 2, PCI DSS, GDPR, HIPAA, ISO 27001, and ISO 27002. This lets teams analyze cloud infrastructure through the lens of NIST without treating NIST as a separate manual spreadsheet.
- Framework section visibility. Cloudaware can show compliance not only by framework, but also by framework section. Instead of one flat NIST score, teams can drill into identity, logging, network, encryption, vulnerability management, and other control areas to see where remediation should start.
- Cross-framework evidence reuse. The same policy can map to multiple standards, so one operational check can support several audit programs. A public bucket policy, for example, may map to NIST, CIS, PCI DSS, FedRAMP, and SOC 2 at once.
- Exception and suppression workflows. Cloudaware helps reduce compliance noise by tracking approved exceptions with suppression status, expiration dates, and exception logic. That matters when development, testing, or unused regions should not be treated the same as production scope.
- CMDB-based compliance processing. Cloudaware evaluates policies against CMDB data rather than repeatedly querying provider APIs for every check, which helps large environments avoid provider throttling issues while keeping inventory near real-time.
